“top US regulations affecting data security in 2025”
Related Articles
- “best Practices For Implementing Zero Trust Architecture In Business”
- “how To Secure Customer Data In E-commerce Platforms”
- “how To Train Employees To Prevent Phishing Attacks”
- “emerging Cybersecurity Solutions For Protecting Intellectual Property”
- “best VPN Services For Corporate Use”
Introduction
Join us as we explore “top US regulations affecting data security in 2025”, packed with exciting updates
By 2025, several US regulations will significantly impact how organizations handle sensitive information. Understanding these regulations isn’t just about compliance; it’s about proactive risk management and building a robust security posture that safeguards both your organization and your customers. This article delves into the top US regulations shaping data security in 2025, offering valuable insights and practical tips to navigate this complex terrain.

1. The California Consumer Privacy Act (CCPA) and its Evolution: Beyond 2025
The CCPA, while not new, continues to evolve and will remain a cornerstone of US data privacy regulation well into 2025. Its successor, the California Privacy Rights Act (CPRA), significantly expands its scope and enforcement. Understanding the intricacies of the CPRA is crucial. The "big secret" here isn’t about hidden loopholes, but rather about proactive interpretation.
-
Secret Tip 1: Focus on Data Minimization: The CPRA emphasizes limiting the collection of personal information to what is strictly necessary. Avoid over-collecting data, and ensure you have a clear justification for every data point you gather. This minimizes your exposure to potential breaches and simplifies compliance.
-
Secret Tip 2: Transparency is Key: The CPRA demands unprecedented transparency. Make your privacy policy easily accessible, understandable, and regularly updated. Clearly articulate what data you collect, how you use it, and who you share it with. Provide simple and effective mechanisms for consumers to exercise their rights (access, deletion, opt-out).
Secret Tip 3: Robust Data Security Measures: The CPRA doesn’t explicitly define specific security measures, but it implies a reasonable level of protection commensurate with the sensitivity of the data. Implement robust security controls, including encryption, access controls, regular security assessments, and incident response plans. Document these measures thoroughly.
2. The State-by-State Data Privacy Mosaic: Navigating a Patchwork of Laws
Beyond California, numerous other states have enacted or are considering their own comprehensive data privacy laws. This creates a complex patchwork of regulations that organizations must navigate. The "secret" here is understanding the nuances of each law and developing a centralized approach to compliance.
-
Secret Tip 4: Centralized Compliance Program: Develop a centralized data privacy program that can adapt to the unique requirements of each state’s law. This avoids the chaos of managing compliance on a state-by-state basis. Use a common framework and adapt it to specific requirements.
-
Secret Tip 5: Stay Updated: The landscape is constantly shifting. Establish a system for monitoring legislative changes at the state level. Subscribe to relevant newsletters, engage with legal experts, and attend industry conferences to stay informed about emerging regulations.
-
Secret Tip 6: Prioritize High-Risk States: Focus your resources on states with the most stringent regulations and the highest penalties for non-compliance. This allows for a prioritized approach to compliance efforts.
3. The Health Insurance Portability and Accountability Act (HIPAA): Protecting Sensitive Health Information
HIPAA remains a critical regulation for organizations handling Protected Health Information (PHI). While not new, HIPAA’s enforcement continues to strengthen, and the penalties for non-compliance are substantial.
-
Secret Tip 7: Business Associate Agreements (BAAs): Ensure that all your business associates who handle PHI have signed BAAs that meet HIPAA requirements. This clarifies responsibilities and accountability for data protection.
-
Secret Tip 8: Regular Security Risk Assessments: Conduct regular risk assessments to identify vulnerabilities in your systems and processes. Document these assessments and implement corrective actions to address identified risks.
-
Secret Tip 9: Employee Training: Invest in comprehensive employee training programs on HIPAA compliance. This ensures that employees understand their responsibilities and can identify and report potential security breaches.
4. The Gramm-Leach-Bliley Act (GLBA): Safeguarding Financial Data
GLBA protects the privacy of consumers’ nonpublic personal information held by financial institutions. Compliance requires robust security measures and transparent privacy practices.
-
Secret Tip 10: Data Encryption: Employ strong encryption methods to protect sensitive financial data both in transit and at rest. This minimizes the risk of data breaches and protects against unauthorized access.
-
Secret Tip 11: Access Controls: Implement strict access controls to limit access to sensitive financial data to authorized personnel only. Use role-based access control (RBAC) to manage permissions effectively.
-
Secret Tip 12: Regular Audits: Conduct regular audits to ensure compliance with GLBA requirements. These audits should assess your security controls, data handling practices, and employee training programs.
5. The Children’s Online Privacy Protection Act (COPPA): Protecting Children’s Data
COPPA regulates the collection, use, and disclosure of personal information from children under 13. Compliance requires strict adherence to parental consent requirements and robust data security measures.
-
Secret Tip 13: Parental Consent Mechanisms: Implement clear and effective mechanisms for obtaining verifiable parental consent before collecting personal information from children. This ensures that you comply with COPPA’s requirements.
-
Secret Tip 14: Data Minimization for Children: Collect only the minimum amount of personal information necessary from children. Avoid collecting unnecessary data points to reduce your risk of non-compliance.
-
Secret Tip 15: Age Verification Procedures: Implement robust age verification procedures to accurately determine the age of users. This is crucial for ensuring compliance with COPPA’s requirements.
6. NIST Cybersecurity Framework: A Voluntary but Influential Guide
While not a regulation itself, the NIST Cybersecurity Framework (CSF) provides a voluntary framework for improving cybersecurity practices. Increasingly, regulators are referencing the CSF, making its adoption a practical strategy for demonstrating compliance.
-
Secret Tip 16: Align with the CSF: Align your cybersecurity program with the NIST CSF. This provides a structured approach to risk management and demonstrates a proactive commitment to cybersecurity.
-
Secret Tip 17: Continuous Improvement: The CSF emphasizes continuous improvement. Regularly assess your cybersecurity posture, identify areas for improvement, and implement corrective actions to enhance your security.
-
Secret Tip 18: Documentation is Crucial: Thoroughly document your cybersecurity practices, including risk assessments, security controls, and incident response plans. This demonstrates compliance and facilitates audits.
7. Emerging Regulations and the Future of Data Security
The regulatory landscape is dynamic. New regulations are likely to emerge in the coming years, further shaping the data security landscape. Staying informed and adaptable is key.
-
Secret Tip 19: Proactive Monitoring: Actively monitor legislative developments at the federal and state levels. Stay updated on proposed regulations and their potential impact on your organization.
-
Secret Tip 20: Engage with Industry Experts: Engage with legal experts, cybersecurity professionals, and industry associations to stay informed about emerging trends and best practices.
8. The Importance of a Holistic Approach
Effective data security in 2025 and beyond requires a holistic approach. This means integrating data security into every aspect of your business operations, from data collection and processing to storage and disposal.
-
Secret Tip 21: Data Security by Design: Implement data security principles from the outset of any new project or system. This ensures that security is built-in, rather than bolted-on as an afterthought.
-
Secret Tip 22: Data Loss Prevention (DLP): Implement robust DLP measures to prevent sensitive data from leaving your organization’s control. This includes measures such as data encryption, access controls, and monitoring.
-
Secret Tip 23: Incident Response Planning: Develop a comprehensive incident response plan to address potential data breaches effectively. This plan should include procedures for detection, containment, eradication, recovery, and post-incident activity.
Frequently Asked Questions (FAQs)
Q1: What happens if my organization doesn’t comply with these regulations?
A1: Non-compliance can result in significant penalties, including hefty fines, legal action, reputational damage, and loss of customer trust. The specific penalties vary depending on the regulation and the severity of the violation.
Q2: How can I stay updated on changes to these regulations?
A2: Subscribe to legal and industry newsletters, attend conferences, engage with legal experts, and monitor relevant government websites for updates.
Q3: Is it necessary to hire a specialized data security consultant?
A3: For many organizations, especially those handling large volumes of sensitive data, engaging a specialized consultant can be invaluable. They can provide expertise in navigating the complex regulatory landscape and implementing effective security measures.
Q4: Can I rely solely on technology to ensure compliance?
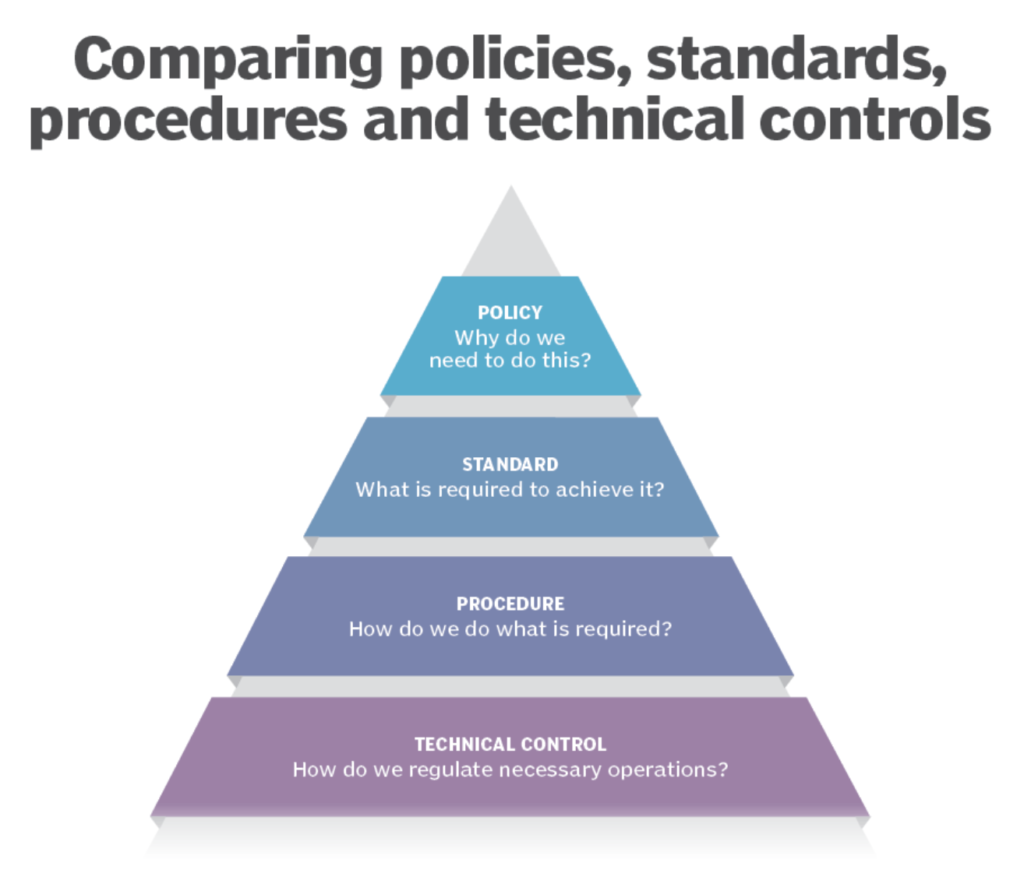
A4: Technology plays a crucial role, but it’s not a silver bullet. Compliance requires a combination of technology, policies, procedures, employee training, and a strong security culture.
Q5: What is the best way to balance data security with business operations?
A5: Data security shouldn’t hinder business operations. A well-designed security program integrates security into business processes, enabling efficient operations while protecting sensitive information.
This comprehensive overview provides a starting point for understanding the top US regulations affecting data security in 2025. Remember that proactive compliance is not just about avoiding penalties; it’s about building trust with customers, protecting your valuable assets, and maintaining a strong competitive advantage in the ever-evolving digital landscape. Regularly revisiting and updating your strategies based on evolving regulations and best practices is essential for long-term success.
[Source URL: Insert relevant URL here, for example, a link to a reputable law firm specializing in data security or a government website outlining data privacy regulations.]
Closure
Thank you for reading! Stay with us for more insights on “top US regulations affecting data security in 2025”.
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “top US regulations affecting data security in 2025″—leave your comments below!
Keep visiting our website for the latest trends and reviews.
