“top data encryption tools for enterprises in 2025”
Related Articles
- “cloud Security Trends For Business Owners 2025”
- “how To Protect Sensitive Business Data From Ransomware”
- “role Of Data Loss Prevention (DLP) Tools In Business Security”
- “cybersecurity Measures For Protecting Business APIs”
- “cost Of A Data Breach In 2025 And How To Avoid It”
Introduction
Welcome to our in-depth look at “top data encryption tools for enterprises in 2025”
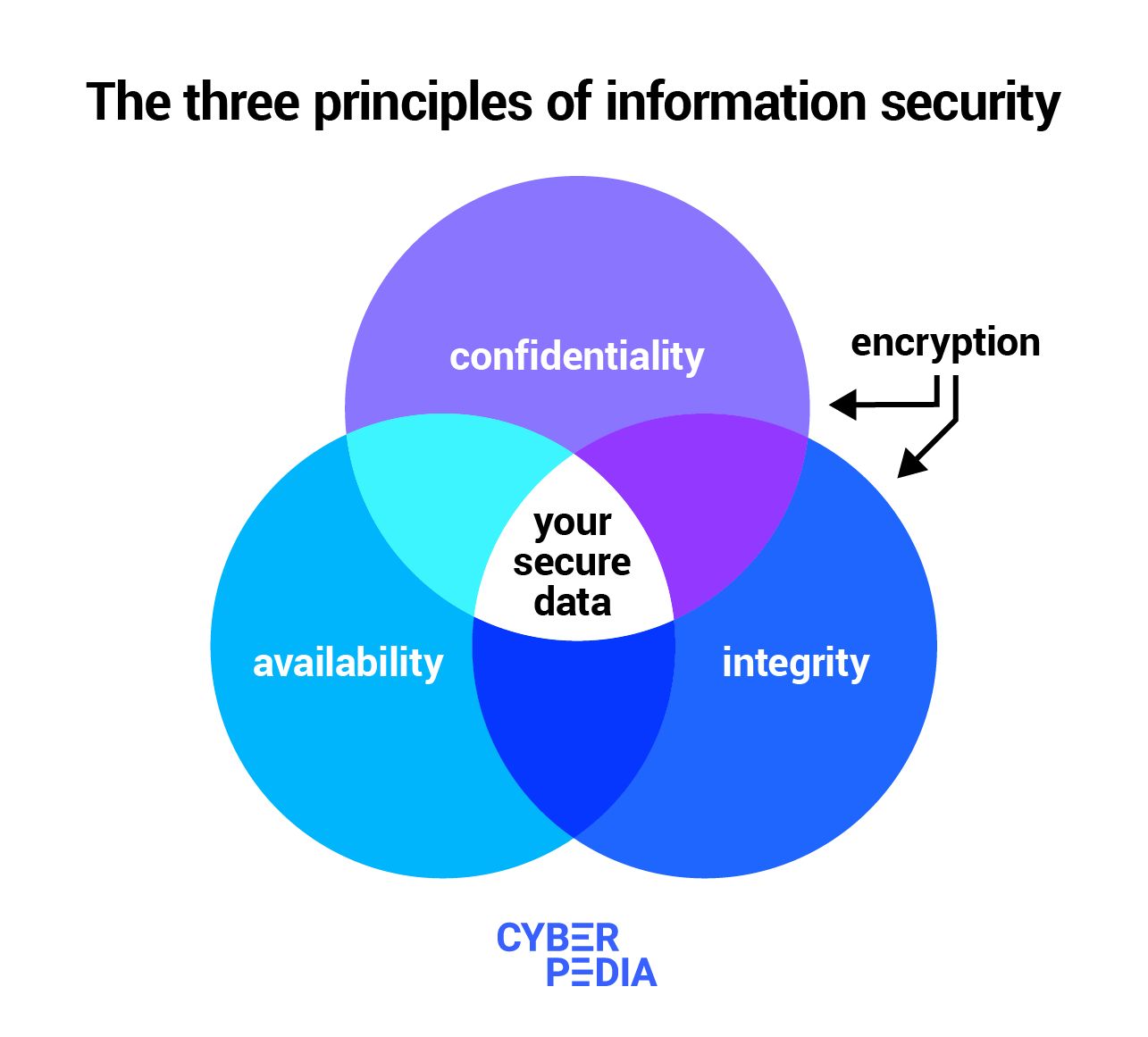
Cyber threats are becoming more sophisticated, persistent, and devastating, making robust data encryption a non-negotiable necessity. This article delves into the top data encryption tools expected to dominate the enterprise market in 2025, revealing not just their features but also the often-overlooked tips and tricks that unlock their full potential. We’ll explore the nuances of different encryption methods, deployment strategies, and key management best practices, ultimately empowering you to make informed decisions to safeguard your valuable data.
1. Beyond the Hype: Understanding Encryption Types and Their Suitability
Before diving into specific tools, understanding the core encryption types is crucial. In 2025, enterprises will continue to rely on a blend of:
-
Symmetric Encryption: This method uses the same key for both encryption and decryption. While fast and efficient, key exchange presents a significant security challenge. Advanced symmetric algorithms like AES-256 (and potentially even stronger successors) will remain prevalent, particularly for encrypting large datasets at rest. Secret Tip: Implement robust key management systems, including regular key rotation and secure storage, to mitigate the risks associated with symmetric encryption. Consider hardware security modules (HSMs) for enhanced security.
-
Asymmetric Encryption (Public Key Cryptography): This uses a pair of keys – a public key for encryption and a private key for decryption. This solves the key exchange problem of symmetric encryption. RSA and ECC (Elliptic Curve Cryptography) algorithms will continue to be dominant, particularly for securing communication channels (TLS/SSL) and digital signatures. Secret Trick: Leverage digital signature capabilities to ensure data integrity and authenticity. Combine asymmetric encryption with symmetric encryption for optimal efficiency – use asymmetric encryption to exchange the symmetric key, then use symmetric encryption for the bulk data.
Homomorphic Encryption: This allows computations to be performed on encrypted data without decryption. While still in its relatively early stages of adoption in 2025, its potential for secure cloud computing and data analysis will see increased interest. Secret Tip: Explore homomorphic encryption solutions for specific use cases where data privacy is paramount even during processing. This requires careful evaluation of performance trade-offs.
2. Top Contenders: Data Encryption Tools for 2025
The market is dynamic, but several tools are likely to maintain their leadership positions in 2025:
-
Microsoft Azure Information Protection (AIP): Microsoft’s integrated solution offers a comprehensive approach to data protection, including encryption, access control, and data loss prevention (DLP). Secret Tip: Utilize AIP’s granular control features to apply different encryption levels based on sensitivity and user roles. Integrate AIP with Microsoft 365 for seamless protection across various applications.
-
Google Cloud Platform (GCP) Cloud Key Management Service (KMS): GCP’s KMS provides robust key management capabilities, integrating seamlessly with other GCP services. Secret Trick: Implement hierarchical key management to delegate responsibilities and improve control. Leverage GCP’s audit logging to track all key access and management activities.
-
AWS Key Management Service (KMS): Similar to GCP KMS, AWS KMS offers a secure and scalable solution for managing encryption keys within the AWS ecosystem. Secret Tip: Utilize AWS KMS’s integration with other AWS services (e.g., S3, EBS) to automate encryption and decryption processes. Explore AWS’s Hardware Security Modules (HSMs) for enhanced key protection.
-
Sophisticated Third-Party Solutions: Specialized vendors like Thales, Entrust, and others will offer advanced encryption solutions tailored to specific enterprise needs, often incorporating hardware security modules (HSMs) for enhanced security. Secret Trick: Carefully evaluate vendor capabilities, certifications (e.g., FIPS 140-2), and support offerings before making a decision.
3. Data Encryption at Rest vs. in Transit: A Strategic Approach
Effective data protection requires a layered approach that addresses both data at rest and data in transit:
-
Data at Rest: This focuses on encrypting data stored on servers, databases, and storage devices. Tools like disk encryption, database encryption, and file-level encryption are crucial. Secret Tip: Employ full-disk encryption (FDE) on all servers and laptops to protect data even if the device is stolen or compromised. Implement transparent data encryption (TDE) for databases to encrypt data without application modifications.
-
Data in Transit: This involves protecting data as it travels across networks. TLS/SSL encryption is essential for securing communication channels. Secret Trick: Implement Transport Layer Security (TLS) 1.3 or later for enhanced security and performance. Utilize VPNs to create secure tunnels for sensitive data transmission.
4. Key Management: The Unsung Hero of Data Encryption
Key management is arguably the most critical aspect of data encryption. Compromised keys render even the strongest encryption algorithms useless. Big Secret Tip: Implement a robust key management system that includes:
- Key Generation: Use strong random number generators to create unpredictable keys.
- Key Storage: Store keys securely, ideally using hardware security modules (HSMs).
- Key Rotation: Regularly rotate keys to mitigate the risk of long-term key compromise.
- Access Control: Implement strict access control measures to limit access to keys.
- Key Lifecycle Management: Establish clear procedures for key creation, usage, rotation, and destruction.
5. Integrating Encryption into Your Workflow: Practical Implementation Strategies
Successfully integrating encryption into your existing workflows requires careful planning and execution. Big Secret Trick:
- Start with a comprehensive risk assessment: Identify your most sensitive data and prioritize encryption accordingly.
- Choose the right tools: Select tools that are compatible with your existing infrastructure and applications.
- Develop a clear implementation plan: Define timelines, responsibilities, and testing procedures.
- Provide adequate training: Ensure your employees understand the importance of data encryption and how to use the chosen tools effectively.
- Monitor and audit your security posture: Regularly monitor your encryption systems and conduct security audits to identify and address vulnerabilities.
6. The Human Element: Combating Social Engineering Attacks
Even the strongest encryption can be bypassed by social engineering attacks. Secret Tip: Invest in comprehensive security awareness training for your employees. Educate them about phishing scams, malware, and other social engineering tactics. Implement multi-factor authentication (MFA) to add an extra layer of security.
7. Future Trends in Enterprise Data Encryption
In 2025 and beyond, we can expect to see:
- Increased adoption of homomorphic encryption: As the technology matures, its use cases will expand.
- Greater integration with AI and machine learning: AI can assist in key management and anomaly detection.
- Enhanced focus on quantum-resistant cryptography: Preparing for the potential threat of quantum computers.
- More emphasis on privacy-enhancing technologies (PETs): These technologies allow data analysis without compromising privacy.
8. Staying Ahead of the Curve: Continuous Monitoring and Adaptation
The threat landscape is constantly evolving. Big Secret Trick: Establish a continuous monitoring and improvement process for your data encryption strategy. Regularly review your security posture, update your tools and processes, and stay informed about the latest threats and vulnerabilities. Participate in industry events and engage with security experts to stay ahead of the curve.
Frequently Asked Questions (FAQs)
Q: What is the best encryption algorithm for my enterprise?
A: There’s no single "best" algorithm. The optimal choice depends on your specific needs and risk tolerance. AES-256 is a strong and widely used symmetric algorithm, while RSA and ECC are popular choices for asymmetric encryption. Consider consulting with a security expert to determine the most appropriate algorithms for your environment.
Q: How much will implementing data encryption cost?
A: The cost varies significantly depending on the chosen tools, the scale of your deployment, and the level of expertise required. Factor in the costs of software licenses, hardware (e.g., HSMs), implementation services, and ongoing maintenance.
Q: How can I ensure my data is truly secure?
A: Data security is a multi-layered approach. Strong encryption is crucial, but it’s only one part of the puzzle. Combine encryption with other security measures, such as access control, data loss prevention (DLP), intrusion detection systems (IDS), and regular security audits.
Q: What should I do if I suspect a data breach?
A: Immediately initiate your incident response plan. Isolate affected systems, investigate the breach, and notify relevant authorities and affected parties.
This comprehensive guide provides a strong foundation for building a robust enterprise data encryption strategy in 2025. Remember that continuous learning and adaptation are crucial in the ever-evolving world of cybersecurity.
Source URL: [Insert a relevant URL from a reputable cybersecurity resource here, e.g., NIST website or a cybersecurity vendor’s whitepaper.]
Closure
We hope this article has helped you understand everything about “top data encryption tools for enterprises in 2025”. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on “top data encryption tools for enterprises in 2025”!
We’d love to hear your thoughts about “top data encryption tools for enterprises in 2025″—leave your comments below!
Stay informed with our next updates on “top data encryption tools for enterprises in 2025” and other exciting topics.
