“securing remote work setups against cyber threats”
Related Articles
- “how To Protect Sensitive Business Data From Ransomware”
- “AI-driven Threat Detection Tools For Businesses”
- “cost Analysis Of Cybersecurity Solutions For SMEs In 2025”
- “top Cybersecurity Threats To Small Businesses In 2025”
- “how AI Is Reshaping Data Security Strategies In 2025”
Introduction
Join us as we explore “securing remote work setups against cyber threats”, packed with exciting updates
However, this shift has also expanded the attack surface for cybercriminals. Securing remote work setups against cyber threats is no longer a luxury; it’s a necessity. This article delves into the often-overlooked strategies and "big secret" tips that can significantly bolster your security posture, moving beyond the basic advice readily available online.
1. Beyond the VPN: Layering Your Network Security
While a Virtual Private Network (VPN) is a cornerstone of remote work security, relying solely on it is a dangerous oversimplification. Think of network security like building a fortress: a VPN is a strong outer wall, but you need multiple layers of defense within.
Secret Tip #1: Implement a Zero Trust Network Access (ZTNA) strategy. ZTNA operates on the principle of "never trust, always verify." Instead of granting broad network access based on IP address or location, ZTNA verifies the user’s identity and device posture before granting access to specific applications and resources. This limits the impact of a compromised device, preventing lateral movement within your network.
Secret Tip #2: Utilize micro-segmentation. This technique divides your network into smaller, isolated segments. Even if one segment is compromised, the attacker’s access is limited to that specific area, preventing widespread damage. This is particularly crucial for organizations with diverse departments and sensitive data.
Secret Tip #3: Employ robust firewalls on both your network and individual devices. Go beyond basic firewall configurations. Implement advanced features like intrusion detection/prevention systems (IDS/IPS) to actively monitor and block malicious traffic. Consider next-generation firewalls (NGFWs) that leverage deep packet inspection for enhanced threat detection.
2. Device Security: Hardening Your Hardware and Software
Your employees’ devices are the first line of defense (and often the weakest link). Securing these endpoints requires a multi-pronged approach that goes beyond basic antivirus software.
Secret Tip #4: Implement Device Posture Assessment (DPA). DPA tools continuously monitor the security posture of your employees’ devices, checking for vulnerabilities, outdated software, and missing security patches. This allows you to proactively identify and address potential risks before they can be exploited.
Secret Tip #5: Employ Mobile Device Management (MDM) and Endpoint Detection and Response (EDR) solutions. MDM allows you to remotely manage and secure company-owned mobile devices, enforcing security policies and remotely wiping data if necessary. EDR provides advanced threat detection and response capabilities on endpoints, identifying and neutralizing sophisticated attacks.
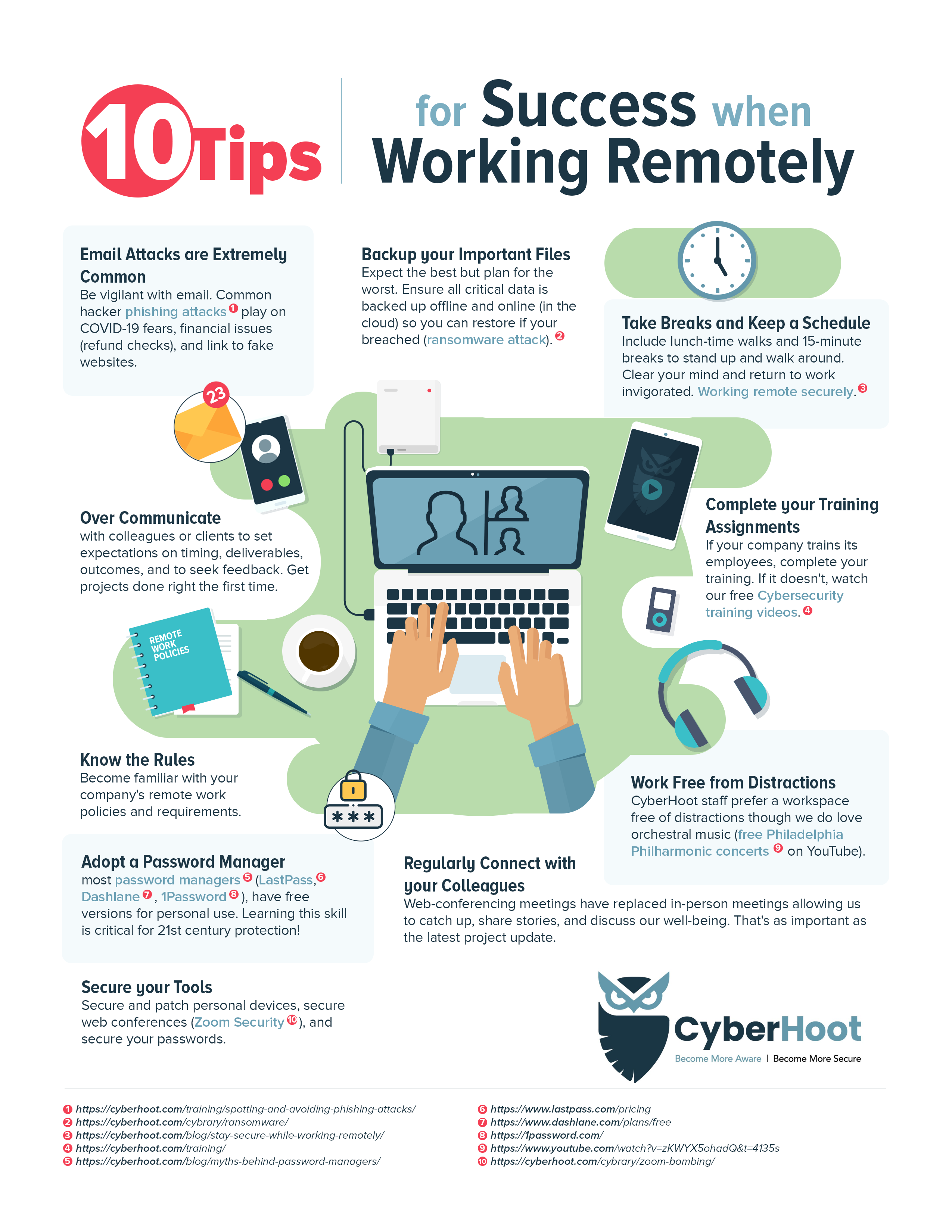
Secret Tip #6: Enforce strong password policies and multi-factor authentication (MFA) across all devices and accounts. This is not just about complex passwords; it’s about enforcing password rotation, using password managers, and implementing MFA wherever possible. Consider using passwordless authentication solutions for enhanced security.

3. Data Security: Protecting Your Most Valuable Asset
Data breaches can have devastating consequences. Protecting your sensitive data requires a layered approach combining technical and procedural safeguards.
Secret Tip #7: Implement Data Loss Prevention (DLP) tools. DLP solutions monitor data movement within and outside your network, identifying and preventing sensitive data from leaving your control. This includes email, cloud storage, and other data transfer methods.
Secret Tip #8: Employ robust encryption at rest and in transit. Encrypt all sensitive data stored on your devices and servers. Use strong encryption protocols for all data transmitted over the network, including VPNs and cloud storage.
Secret Tip #9: Regularly back up your data to a secure, offsite location. This ensures business continuity in case of a ransomware attack or other data loss event. Implement a robust disaster recovery plan to ensure you can quickly restore your data and systems.
4. User Education and Training: The Human Firewall
Even the most robust technical security measures are useless if your employees are unaware of the risks or fall victim to phishing scams.
Secret Tip #10: Conduct regular security awareness training. This training should go beyond basic awareness; it should simulate real-world phishing attacks and teach employees how to identify and report suspicious emails and websites.
Secret Tip #11: Implement a security awareness program that includes phishing simulations and regular testing. This allows you to identify vulnerabilities in your employees’ security awareness and address them proactively.
Secret Tip #12: Foster a security-conscious culture. Encourage employees to report suspicious activity and provide them with the resources and support they need to stay safe online.
5. Cloud Security: Navigating the Cloud Landscape Safely
Many remote work setups rely heavily on cloud services. Securing your cloud environment requires a different approach than securing on-premises infrastructure.
Secret Tip #13: Leverage cloud-native security tools. Cloud providers offer a range of security tools and services, including intrusion detection, data encryption, and access control. Utilize these tools to enhance your cloud security posture.
Secret Tip #14: Implement strong access control and least privilege principles. Grant users only the access they need to perform their jobs, minimizing the potential impact of a compromised account.
Secret Tip #15: Regularly monitor your cloud environment for suspicious activity. Cloud providers offer logging and monitoring tools that can help you identify and respond to security incidents.
6. Incident Response Planning: Preparing for the Inevitable
Despite your best efforts, security incidents can still occur. Having a well-defined incident response plan is crucial for minimizing the damage and ensuring a swift recovery.
Secret Tip #16: Develop a comprehensive incident response plan. This plan should outline the steps to be taken in the event of a security incident, including incident identification, containment, eradication, recovery, and post-incident activity.
Secret Tip #17: Conduct regular incident response drills. This will help your team practice their response procedures and identify any weaknesses in your plan.
Secret Tip #18: Establish clear communication channels. Ensure that all stakeholders know how to communicate during a security incident and who is responsible for what.
7. Regular Audits and Assessments: Continuous Improvement
Security is not a one-time event; it’s an ongoing process. Regular audits and assessments are crucial for identifying vulnerabilities and ensuring your security measures remain effective.
Secret Tip #19: Conduct regular vulnerability scans and penetration testing. This will help you identify weaknesses in your security posture and address them before they can be exploited.
Secret Tip #20: Regularly review and update your security policies and procedures. Your security environment is constantly evolving, so your policies and procedures must adapt to keep pace.
8. Staying Ahead of the Curve: Continuous Learning and Adaptation
The threat landscape is constantly evolving, so staying informed about the latest threats and vulnerabilities is crucial.
Secret Tip #21: Subscribe to security newsletters and blogs. Stay up-to-date on the latest security news and best practices.
Secret Tip #22: Participate in security conferences and training events. Network with other security professionals and learn from their experiences.
Secret Tip #23: Foster a culture of continuous learning within your organization. Encourage your team to stay informed about security threats and best practices.
Frequently Asked Questions (FAQs)
Q: What is the most important aspect of remote work security?
A: While all aspects are crucial, employee training and awareness are arguably the most important. Even the best technology is useless if employees fall for phishing scams or engage in risky online behavior.
Q: How can I protect my data from ransomware attacks?
A: Implement robust backups to an offline location, regularly update your software, and train employees to identify and avoid phishing emails that might deliver ransomware.
Q: What is the difference between a VPN and ZTNA?
A: A VPN creates a secure tunnel for all your network traffic. ZTNA grants access only to specific applications and resources, based on identity and device posture, offering more granular control.
Q: How often should I update my security software?
A: Security software should be updated automatically whenever updates are available. Check for updates regularly and ensure automatic updates are enabled.
Q: What should I do if I suspect a security breach?
A: Immediately follow your incident response plan. Isolate affected systems, investigate the breach, and notify relevant authorities if necessary.
Q: Are free VPNs secure enough for remote work?
A: Generally, no. Free VPNs often lack the robust security features and logging policies of paid services. They may even compromise your security by logging your activity or injecting malware.
By implementing these strategies and tips, organizations can significantly reduce their risk of cyberattacks and build a robust security posture for their remote workforce. Remember that security is an ongoing process, requiring continuous monitoring, adaptation, and improvement.
Source URL: [Insert a relevant source URL here, e.g., a reputable cybersecurity firm’s website or a government cybersecurity resource.] For example: https://www.cisa.gov/ (This is an example; replace with a more specific and relevant URL).
Closure
We hope this article has helped you understand everything about “securing remote work setups against cyber threats”. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on “securing remote work setups against cyber threats”!
Feel free to share your experience with “securing remote work setups against cyber threats” in the comment section.
Keep visiting our website for the latest trends and reviews.
