“securing financial transactions with post-quantum cryptography”
Related Articles
- “how To Protect Sensitive Business Data From Ransomware”
- “how To Choose The Best Cybersecurity Consultant For Your Business”
- “top Cybersecurity Threats To Small Businesses In 2025”
- “securing Business Networks Against AI-based Attacks”
- “best Practices For Implementing Zero Trust Architecture In Business”
Introduction
Welcome to our in-depth look at “securing financial transactions with post-quantum cryptography”
These systems, which underpin the vast majority of online financial transactions, rely on mathematical problems that are computationally infeasible for classical computers to solve. However, quantum computers, once sufficiently powerful, will be able to break these problems relatively easily, rendering our current security measures obsolete. This necessitates a transition to post-quantum cryptography (PQC), algorithms designed to withstand attacks from both classical and quantum computers. This article delves into the crucial aspects of securing financial transactions using PQC, revealing some "big secret" tips and tricks for enhanced security.

1. Understanding the Quantum Threat: Why We Need PQC
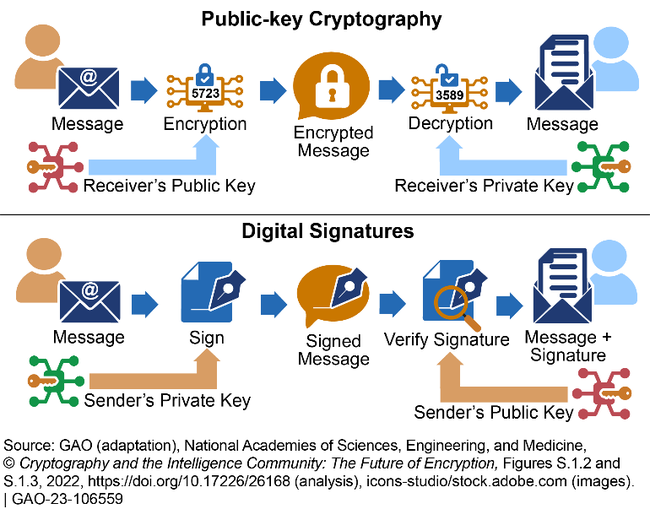
Before diving into the specifics of PQC, it’s crucial to understand the threat quantum computing poses. Currently, widely used algorithms like RSA and ECC (Elliptic Curve Cryptography) rely on the difficulty of factoring large numbers or solving the discrete logarithm problem. These are computationally intensive tasks for classical computers, making them suitable for securing sensitive data. However, Shor’s algorithm, a quantum algorithm, can solve these problems exponentially faster than the best known classical algorithms. This means that a sufficiently powerful quantum computer could crack widely used encryption schemes in a matter of hours, potentially exposing vast amounts of sensitive financial data.
This isn’t a hypothetical threat; research into quantum computing is progressing rapidly. While a fully functional, large-scale quantum computer capable of breaking current encryption is not yet available, the potential for future attacks necessitates proactive measures. The transition to PQC is not just a matter of "when" but "how quickly" we can implement robust and reliable solutions.
2. Key Algorithm Families: Choosing the Right PQC Solution
Several promising PQC algorithm families are currently under consideration for standardization. The National Institute of Standards and Technology (NIST) has recently finalized its selection of PQC algorithms, offering diverse options based on different mathematical problems. These include:
-
Lattice-based cryptography: This family relies on the hardness of problems related to lattices, high-dimensional geometric structures. Algorithms like CRYSTALS-Kyber (for key encapsulation) and CRYSTALS-Dilithium (for digital signatures) are considered strong contenders due to their efficiency and security. They offer a good balance between performance and security, making them suitable for a wide range of applications.
Code-based cryptography: These algorithms are based on the difficulty of decoding random linear codes. Classic McEliece is a notable example, offering strong security but with higher computational overhead compared to lattice-based schemes. Its main advantage lies in its long history and well-understood security properties.
-
Multivariate cryptography: This family relies on the difficulty of solving systems of multivariate polynomial equations. While offering strong security, these algorithms often suffer from larger key sizes and slower performance. Rainbow is a notable example, but its suitability for widespread adoption remains under scrutiny.
-
Hash-based cryptography: These algorithms are based on cryptographic hash functions and offer strong security guarantees. However, they are typically less efficient than other approaches, particularly for key exchange. They are more suitable for specific applications where forward secrecy is paramount.
The choice of the "right" algorithm depends heavily on the specific application and the desired balance between security, performance, and key size. Financial transactions may benefit from a hybrid approach, combining different PQC algorithms for optimal security and efficiency.
3. Hybrid Approaches: Combining PQC and Classical Cryptography
A purely PQC-based system might be premature, especially considering the ongoing research and potential vulnerabilities that might be discovered in the future. A hybrid approach, combining PQC with existing classical cryptography, offers a more pragmatic and secure solution. This approach leverages the strengths of both worlds, providing immediate security while gradually transitioning to fully PQC-based systems.
One common strategy is to use PQC for key exchange or digital signatures, while relying on established classical algorithms for data encryption. This allows for a smoother transition, minimizing disruption to existing infrastructure while enhancing long-term security. For instance, using CRYSTALS-Kyber for key exchange and AES-GCM for data encryption provides a robust hybrid solution.
4. Implementation Challenges and Considerations
Implementing PQC in financial systems presents several challenges:
-
Performance overhead: PQC algorithms generally require more computational resources than their classical counterparts. This necessitates careful optimization and potentially hardware acceleration to minimize performance impacts on transaction processing speeds.
-
Key management: PQC often involves larger key sizes compared to classical algorithms, increasing the complexity of key management and storage. Secure key generation, distribution, and storage are critical for maintaining security.
-
Interoperability: Ensuring interoperability between different PQC implementations across various systems and platforms is essential for widespread adoption. Standardization efforts play a crucial role in achieving this.
-
Integration with existing infrastructure: Integrating PQC into existing financial systems requires careful planning and testing to avoid disruptions and maintain compatibility with existing protocols and security measures.
5. Secret Tip #1: Proactive Migration Strategy
The "big secret" to successfully securing financial transactions with PQC is not a single algorithm but a proactive migration strategy. This involves a phased approach:
- Assessment: Thoroughly assess existing cryptographic infrastructure and identify vulnerabilities to quantum attacks.
- Pilot projects: Implement PQC in smaller-scale pilot projects to evaluate performance, interoperability, and integration challenges.
- Phased rollout: Gradually deploy PQC in production systems, starting with less critical applications and gradually expanding to more sensitive transactions.
- Continuous monitoring: Continuously monitor the performance and security of the PQC implementation, adapting the strategy as needed.
6. Secret Tip #2: Focus on Key Management
Robust key management is paramount for PQC security. Larger key sizes require more secure storage and handling procedures. Consider implementing:
- Hardware security modules (HSMs): These dedicated hardware devices provide a secure environment for generating, storing, and managing cryptographic keys.
- Key rotation: Regularly rotate keys to minimize the impact of potential compromises.
- Key escrow protocols: Implement secure key escrow protocols to facilitate key recovery in case of loss or compromise.
7. Secret Tip #3: Hybrid Approach Optimization
Optimizing the hybrid approach is crucial. Careful selection of algorithms and their integration is vital for maximizing security while minimizing performance overhead. Consider:
- Algorithm selection: Choose algorithms that are well-suited for the specific application and offer the best balance of security and performance.
- Parameter tuning: Optimize algorithm parameters to enhance performance without compromising security.
- Hardware acceleration: Utilize hardware acceleration techniques to improve the performance of PQC algorithms.
8. Secret Tip #4: Collaboration and Standardization
The transition to PQC requires collaboration across the financial industry. Participation in standardization efforts, sharing best practices, and fostering open communication are crucial for ensuring interoperability and accelerating the adoption of secure PQC solutions. Staying informed about the latest NIST recommendations and engaging with the broader cryptographic community is essential.
Frequently Asked Questions (FAQs)
Q: When will quantum computers be able to break current encryption?
A: The timeline is uncertain. While no large-scale quantum computer capable of breaking current encryption exists yet, significant progress is being made. Proactive migration to PQC is crucial to avoid future vulnerabilities.
Q: Is PQC a silver bullet solution?
A: No, PQC is not a perfect solution. Like any cryptographic system, it can be vulnerable to future attacks or implementation flaws. Continuous monitoring, updates, and adaptation are necessary.
Q: How much will the transition to PQC cost?
A: The cost will vary depending on the size and complexity of the financial institution’s infrastructure. It involves software updates, hardware upgrades, and staff training. The long-term cost of inaction, however, is significantly higher.
Q: How long will the transition to PQC take?
A: The transition will be a gradual process, likely spanning several years. A phased approach is recommended to minimize disruption and ensure a smooth migration.
Q: What are the potential risks of delaying the transition to PQC?
A: Delaying the transition increases the risk of future attacks that could compromise sensitive financial data, leading to significant financial losses and reputational damage.
Q: Where can I find more information on PQC?
A: The NIST website, academic research papers, and industry publications are excellent sources of information on PQC.
This comprehensive guide provides a starting point for understanding the complexities of securing financial transactions with post-quantum cryptography. The "big secret" lies not in a single magical solution, but in a proactive, multi-faceted approach that combines careful planning, strategic implementation, and continuous monitoring. Regularly revisiting this information and staying informed about the latest developments in the field is crucial for maintaining the security of financial systems in the quantum era.
Source URL: https://csrc.nist.gov/projects/post-quantum-cryptography
Closure
Thank you for reading! Stay with us for more insights on “securing financial transactions with post-quantum cryptography”.
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “securing financial transactions with post-quantum cryptography”—leave your comments below!
Stay informed with our next updates on “securing financial transactions with post-quantum cryptography” and other exciting topics.
