“role of data loss prevention tools in enterprise security”
Related Articles
- “best Practices For Implementing Zero Trust Architecture In Business”
- “how To Train Employees To Prevent Phishing Attacks”
- “how To Integrate AI With Business Cybersecurity Software”
- “data Breach Insurance Requirements For Businesses”
- “2025 Best Practices For Securing Business Data”
Introduction
Join us as we explore “role of data loss prevention tools in enterprise security”, packed with exciting updates
The financial, reputational, and legal ramifications of a data leak can be catastrophic, crippling even the most established organizations. This is where Data Loss Prevention (DLP) tools step in, playing a crucial, often unsung, role in bolstering enterprise security. While many understand the basic function of DLP, the true power and nuanced applications remain largely unexplored. This article delves into the big secrets and hidden tricks behind effective DLP implementation, offering a comprehensive exploration of its role in modern enterprise security.
1. Beyond the Obvious: Understanding the Multifaceted Nature of DLP
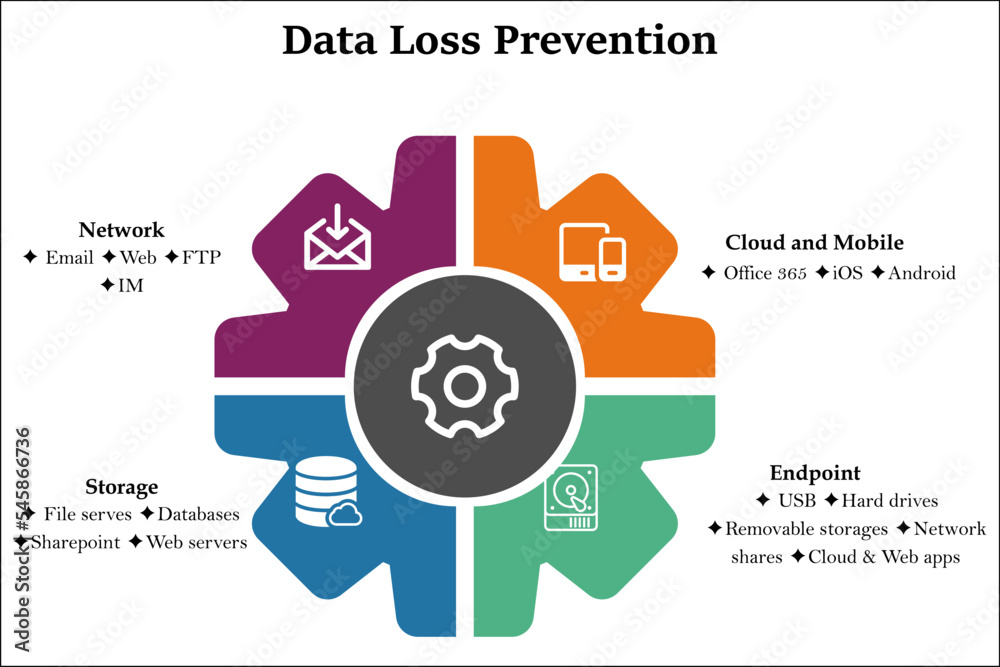
Many perceive DLP as simply a tool that prevents sensitive data from leaving the network perimeter. While this is a core function, it’s only the tip of the iceberg. Modern DLP solutions are far more sophisticated, encompassing a multi-layered approach that addresses various data loss vectors. These include:
-
Network-based DLP: This monitors network traffic for sensitive data being transmitted, whether through email, file transfers, or cloud applications. It can detect and block suspicious activity in real-time, preventing data exfiltration before it occurs. The "secret" here lies in the advanced pattern matching and anomaly detection capabilities, which go beyond simple keyword searches to identify sophisticated obfuscation techniques.
-
Endpoint DLP: This focuses on securing data residing on individual devices like laptops, desktops, and mobile phones. It monitors file access, clipboard activity, and application usage, preventing sensitive information from being copied, printed, or transferred to unauthorized locations. The "trick" here involves integrating with endpoint detection and response (EDR) solutions for a holistic view of endpoint security and more effective threat hunting.

Cloud DLP: With the increasing reliance on cloud services, cloud-based DLP is essential. It monitors data stored in cloud storage services, cloud applications, and SaaS platforms, ensuring compliance with data protection regulations and preventing unauthorized access or sharing. The "secret sauce" is its ability to adapt to various cloud environments and integrate seamlessly with existing cloud security infrastructure.
-
Storage DLP: This focuses on securing data at rest, identifying and protecting sensitive information stored on servers, databases, and other storage repositories. The "trick" here is the use of data classification and encryption techniques to ensure that even if a breach occurs, the data remains inaccessible to unauthorized individuals.
2. Data Classification: The Foundation of Effective DLP
Effective DLP hinges on accurate data classification. This involves identifying and tagging sensitive data based on its confidentiality level, regulatory requirements, and business criticality. The "secret" here lies in implementing a robust data classification strategy that goes beyond simple keyword searches. This includes using contextual analysis, machine learning, and regular expression matching to identify sensitive data even when it’s obfuscated or embedded within larger files. A well-defined data classification scheme allows for tailored DLP policies, ensuring that different levels of protection are applied to different types of data.
3. Policy Management: Fine-Tuning Your DLP Arsenal
DLP policies are the engine that drives the system. They define what data needs protection, where it’s allowed to go, and what actions should be taken when a policy violation occurs. The "big secret" is understanding the nuances of policy creation. Overly restrictive policies can hinder productivity, while overly permissive policies leave your organization vulnerable. The key is to strike a balance, creating granular policies that address specific risks and business needs. This often involves A/B testing different policy configurations to optimize effectiveness and minimize disruption.
4. Integration and Orchestration: The Power of Synergy
DLP doesn’t operate in a vacuum. Its effectiveness is significantly enhanced when integrated with other security tools, creating a synergistic effect. The "secret trick" is seamless integration with SIEM (Security Information and Event Management) systems, threat intelligence platforms, and incident response tools. This allows for comprehensive threat detection, faster incident response, and improved security posture. Integrating DLP with other security layers provides a holistic view of security events, enabling better threat detection and response.
5. User Awareness and Training: The Human Element
Technology alone is insufficient. Successful DLP implementation requires a strong emphasis on user awareness and training. Employees need to understand the importance of data security and the implications of violating DLP policies. The "secret weapon" is engaging training programs that go beyond simple compliance lectures. Interactive simulations, gamification, and regular refresher courses can significantly improve user understanding and compliance.
6. Monitoring and Reporting: Measuring Success and Identifying Gaps
Continuous monitoring and reporting are crucial for evaluating the effectiveness of your DLP program. The "hidden gem" is using the detailed reports generated by DLP tools to identify trends, assess risks, and fine-tune policies. Regular review of these reports allows for proactive adjustments to the DLP strategy, ensuring it remains effective against evolving threats. This data-driven approach is key to optimizing the performance of your DLP solution.
7. Staying Ahead of the Curve: Adapting to Evolving Threats
The threat landscape is constantly evolving. New techniques for data exfiltration are constantly emerging. The "secret to success" is staying ahead of the curve by regularly updating your DLP software, staying informed about emerging threats, and adapting your policies accordingly. This requires continuous monitoring of the threat landscape and proactive adjustments to your DLP strategy.
8. Compliance and Legal Considerations: Navigating the Regulatory Maze
DLP plays a critical role in ensuring compliance with various data protection regulations, such as GDPR, CCPA, and HIPAA. Understanding the specific requirements of these regulations and configuring your DLP tools to meet them is paramount. The "hidden trick" is proactively addressing legal and compliance considerations during the implementation phase, ensuring that your DLP strategy aligns with all relevant regulations and internal policies.
Frequently Asked Questions (FAQs)
Q: How much does DLP software cost?
A: The cost of DLP software varies widely depending on factors such as the number of users, the features included, and the level of support required. Pricing models can range from subscription-based to perpetual licenses. It’s best to contact vendors directly for specific pricing information.
Q: Is DLP suitable for small businesses?
A: While traditionally associated with large enterprises, DLP solutions are increasingly available for small businesses. There are cloud-based DLP options that offer scalable and cost-effective solutions for organizations of all sizes.
Q: How can I ensure my employees comply with DLP policies?
A: A combination of robust training, clear communication, and consistent enforcement is key. Regular reminders, interactive training modules, and consequences for policy violations can encourage compliance.
Q: Can DLP prevent all data loss?
A: While DLP significantly reduces the risk of data loss, it’s not foolproof. Sophisticated attackers may find ways to circumvent DLP measures. A multi-layered security approach, including employee training and other security controls, is essential.
Q: How do I choose the right DLP solution for my organization?
A: Consider factors such as the types of data you need to protect, your budget, your IT infrastructure, and your compliance requirements. Evaluate different vendors and solutions based on their features, ease of use, and integration capabilities.
This article provides a comprehensive overview of the critical role of DLP tools in enterprise security. By understanding the nuances and implementing the strategies outlined above, organizations can significantly enhance their data protection posture and mitigate the risks associated with data breaches. Remember, the true power of DLP lies not just in the technology itself, but in its strategic implementation and integration with a broader security framework.
Source URL: [Insert a relevant URL from a reputable cybersecurity resource here, e.g., a NIST publication or a reputable vendor’s website.]
Closure
We hope this article has helped you understand everything about “role of data loss prevention tools in enterprise security”. Stay tuned for more updates!
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “role of data loss prevention tools in enterprise security”—leave your comments below!
Keep visiting our website for the latest trends and reviews.
