“role of data loss prevention (DLP) tools in business security”
Related Articles
- “managing Third-party Risk In Data Security Strategies”
- “impact Of AI On Insider Threat Detection”
- “how 5G Technology Affects Business Data Security”
- “importance Of Supply Chain Security In Preventing Data Breaches”
- “ransomware Recovery Strategies For Enterprises In 2025”
Introduction
In this article, we dive into “role of data loss prevention (DLP) tools in business security”, giving you a full overview of what’s to come
From customer information to intellectual property, sensitive data fuels operations and drives growth. However, this valuable asset is constantly under threat from internal and external actors. Data breaches, accidental leaks, and malicious insider threats can cripple a company, leading to financial losses, reputational damage, and legal repercussions. This is where Data Loss Prevention (DLP) tools step in, acting as unsung heroes in the fight to protect sensitive information. While many understand the basic function of DLP, a deeper understanding of its capabilities and strategic implementation can significantly enhance a business’s security posture. This article delves into the big secret tips and tricks behind maximizing the effectiveness of DLP tools, transforming them from simple security measures into powerful, proactive defenses.
1. Beyond the Basics: Understanding the Nuances of DLP Functionality
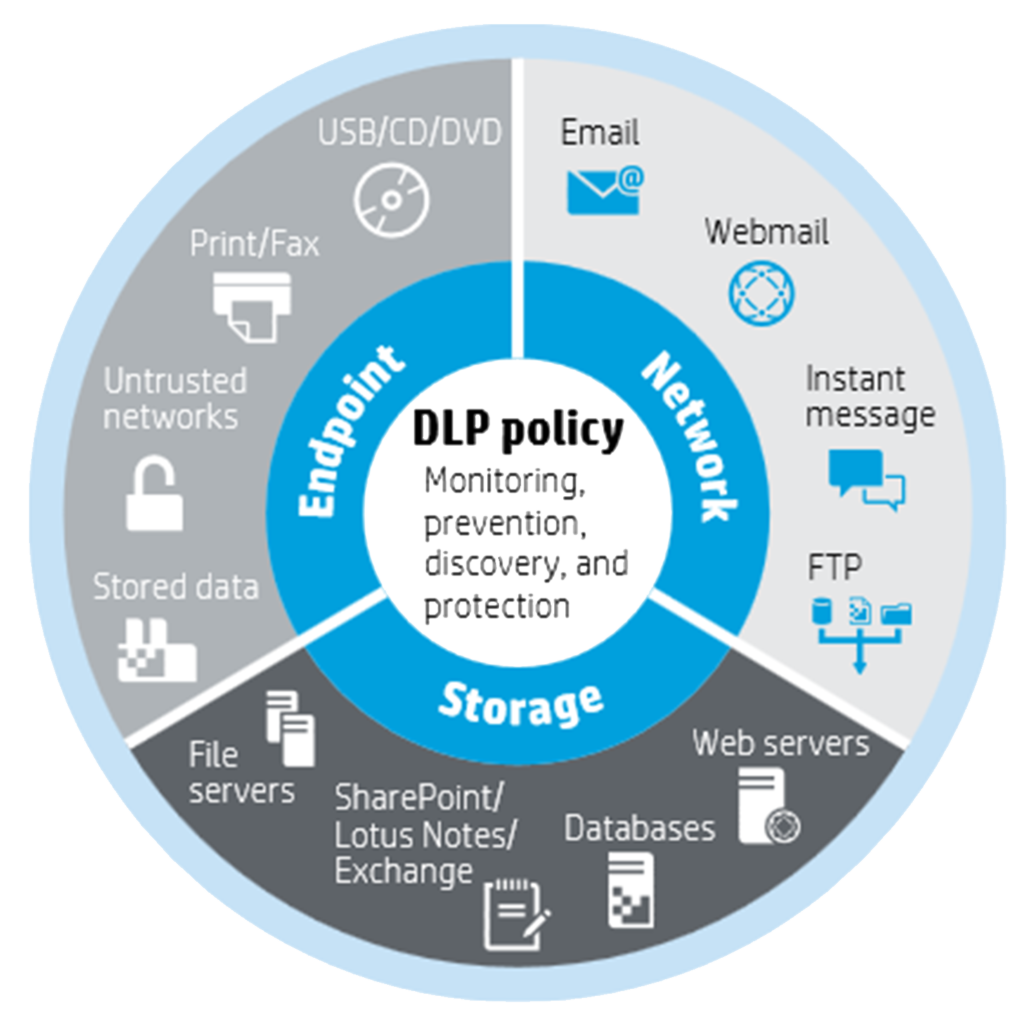
Most businesses understand DLP as a system that prevents sensitive data from leaving the organization’s network. While this is a core function, modern DLP solutions offer a much broader range of capabilities. These include:
-
Data Discovery and Classification: This crucial first step involves identifying where sensitive data resides within the organization. DLP tools utilize advanced techniques like machine learning and natural language processing to automatically classify data based on predefined policies and regular expressions. This goes beyond simple keyword searches, identifying sensitive information even if it’s obfuscated or embedded within larger documents. The "secret" here lies in regularly reviewing and refining these classification rules to keep pace with evolving data types and potential threats.
-
Real-time Monitoring and Prevention: DLP tools don’t just passively scan data; they actively monitor data flows in real-time. This allows for immediate intervention when sensitive data attempts to leave the network through unauthorized channels, such as email, cloud storage, or removable media. The "trick" is configuring alerts and responses appropriately. Immediate blocking might be necessary for high-risk data, while less sensitive data might trigger a warning or require additional authentication.

Incident Response and Forensics: When a data loss incident occurs, DLP tools provide valuable forensic data, enabling rapid investigation and response. They can track the data’s journey, identify the source of the breach, and assist in remediation efforts. The "tip" here is to integrate DLP with other security tools, such as Security Information and Event Management (SIEM) systems, to create a holistic view of security incidents.
-
Endpoint Protection: Many modern DLP solutions extend their protection to endpoints (laptops, desktops, mobile devices). This allows for the monitoring and control of sensitive data on individual devices, even when they are offline or outside the corporate network. The "secret" is ensuring consistent policy enforcement across all endpoints, regardless of their location or operating system.
2. Tailoring DLP Policies: A Personalized Approach to Data Security
A "one-size-fits-all" approach to DLP is ineffective. Different departments and data types require varying levels of protection. The key lies in creating granular, context-aware policies that reflect the specific risks and regulatory requirements of the organization.
-
Contextual Awareness: Effective DLP policies consider the context of data transmission. For example, a policy might allow the sending of a customer’s address via email to a legitimate shipping company but block the same data being sent to a personal email address. This requires careful consideration of legitimate data flows and the implementation of robust exception handling.
-
Data Sensitivity Levels: Categorize data based on its sensitivity (e.g., highly confidential, confidential, internal). This allows for differentiated protection levels, ensuring that the most sensitive data receives the strictest controls. The "trick" is to regularly review and update these sensitivity levels as business needs evolve.
-
User-Based Policies: Policies can be tailored based on user roles and responsibilities. Executives might have more relaxed policies for certain data types, while employees in sensitive roles might face stricter controls. The "secret" is to strike a balance between security and productivity, avoiding overly restrictive policies that hinder legitimate business operations.
-
Regular Policy Reviews and Updates: DLP policies are not static. They need regular review and updates to reflect changes in regulations, business processes, and emerging threats. The "tip" is to schedule regular policy reviews as part of the organization’s overall security management program.
3. Integrating DLP with Other Security Tools: The Power of Synergy
DLP doesn’t operate in isolation. Its effectiveness is significantly amplified when integrated with other security tools, creating a layered defense strategy.
-
SIEM Integration: Integrating DLP with SIEM systems provides a unified view of security events, enabling correlation of DLP alerts with other security incidents. This allows for a more comprehensive understanding of threats and facilitates faster incident response.
-
Endpoint Detection and Response (EDR) Integration: Combining DLP with EDR tools enhances endpoint protection by providing visibility into data access and manipulation on individual devices. This allows for the detection and prevention of malicious activity, even if it doesn’t involve data exfiltration.
-
Cloud Access Security Broker (CASB) Integration: For organizations utilizing cloud services, integrating DLP with CASB solutions extends protection to cloud-based data storage and applications. This ensures consistent data protection regardless of where the data resides.
-
Vulnerability Management Integration: Identifying and addressing vulnerabilities in systems and applications can prevent data breaches before they occur. Integrating DLP with vulnerability management tools provides a more proactive approach to data security.
4. User Training and Awareness: The Human Element of Data Protection
Even the most sophisticated DLP tools are ineffective without user awareness and cooperation. Training employees on data security best practices is crucial to minimizing the risk of accidental data loss.
-
Data Security Policies: Develop clear and concise data security policies that employees understand and can easily follow. These policies should outline acceptable use of company resources and the consequences of violating security policies.
-
Regular Training Programs: Conduct regular training sessions to educate employees on data security threats, best practices, and the role of DLP tools. The "secret" is to make training engaging and relevant to employees’ daily tasks.
-
Phishing and Social Engineering Awareness: A significant portion of data breaches are caused by phishing and social engineering attacks. Training employees to recognize and avoid these attacks is crucial to preventing data loss.
-
Reporting Mechanisms: Establish clear reporting mechanisms for employees to report suspicious activity or potential security incidents. The "tip" is to encourage reporting without fear of reprisal.
5. Choosing the Right DLP Solution: A Strategic Decision
Selecting the right DLP solution is a critical decision that requires careful consideration of several factors.
-
Scalability: Choose a solution that can scale to meet the organization’s growing data volume and user base. The "secret" is to look beyond immediate needs and consider future growth.
-
Integration Capabilities: Ensure the solution integrates seamlessly with existing security infrastructure. This maximizes the effectiveness of the DLP solution and avoids creating security silos.
-
Deployment Options: Consider whether an on-premise, cloud-based, or hybrid deployment model best suits the organization’s needs. The "tip" is to carefully evaluate the pros and cons of each option.
-
Cost: DLP solutions can range in cost from affordable to very expensive. The "secret" is to find a solution that offers the necessary functionality and scalability without breaking the budget.
6. Monitoring and Optimization: Continuous Improvement
Implementing a DLP solution is just the first step. Continuous monitoring and optimization are crucial to ensuring its long-term effectiveness.
-
Regular Reporting and Analysis: Generate regular reports on DLP activity to identify trends and potential areas for improvement. The "trick" is to analyze these reports to identify patterns and refine policies accordingly.
-
False Positive Reduction: DLP tools can generate false positives, which can lead to alert fatigue and reduced effectiveness. Regularly review and refine policies to minimize false positives.
-
Performance Monitoring: Monitor the performance of the DLP solution to ensure it doesn’t impact business operations. The "tip" is to optimize the solution to minimize its impact on system performance.
-
Adaptive Security: The threat landscape is constantly evolving. Regularly update the DLP solution and its policies to address new threats and vulnerabilities.
7. Addressing the Challenges: Overcoming DLP Implementation Hurdles
Implementing DLP can present challenges, including:
-
Complexity: DLP solutions can be complex to configure and manage, requiring specialized expertise.
-
Cost: The cost of implementing and maintaining a DLP solution can be significant.
-
Performance Impact: Poorly configured DLP solutions can negatively impact system performance.
-
User Adoption: Resistance to change from employees can hinder the effectiveness of DLP.
Overcoming these challenges requires careful planning, thorough training, and a phased implementation approach.
8. Frequently Asked Questions (FAQs)
-
Q: What is the difference between DLP and encryption?
-
A: DLP focuses on preventing data loss before it leaves the organization’s control, while encryption protects data after it has left the organization’s control. They are complementary technologies, not mutually exclusive.
-
Q: Can DLP tools detect data exfiltration via physical media?
-
A: Yes, many DLP solutions can monitor and control data transfer via USB drives, external hard drives, and other removable media.
-
Q: How can I measure the effectiveness of my DLP solution?
-
A: Measure the number of prevented data loss incidents, the reduction in security breaches, and the improvement in overall data security posture. Regular reporting and analysis are crucial.
-
Q: What are the legal and regulatory implications of DLP?
-
A: DLP can help organizations comply with various data privacy regulations, such as GDPR and CCPA. However, it’s crucial to understand the specific requirements of the applicable regulations.
-
Q: What is the role of DLP in cloud security?
-
A: DLP plays a vital role in securing cloud-based data by monitoring and controlling data access, transfer, and storage in the cloud. Integration with CASB solutions is crucial in this context.
In conclusion, DLP tools are far more than simple security measures. By understanding their nuances, implementing tailored policies, integrating them with other security tools, and fostering a culture of data security awareness, businesses can unlock the true potential of DLP and significantly enhance their overall security posture. The "secret tips and tricks" discussed here empower organizations to transform their DLP solutions from passive security tools into proactive defenses, safeguarding their most valuable asset – their data.
Source URL: [Insert a relevant URL to a reputable cybersecurity resource, such as a blog post from a security vendor or a cybersecurity news site. For example, a relevant article from the SANS Institute or NIST website would be appropriate.]
Closure
We hope this article has helped you understand everything about “role of data loss prevention (DLP) tools in business security”. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on “role of data loss prevention (DLP) tools in business security”!
We’d love to hear your thoughts about “role of data loss prevention (DLP) tools in business security”—leave your comments below!
Keep visiting our website for the latest trends and reviews.
