“role of blockchain in enhancing business cybersecurity”
Related Articles
- “how To Protect Sensitive Business Data From Ransomware”
- “future-proofing Your Business Against Quantum Hacking”
- “cloud Security Trends For Business Owners 2025”
- “cybersecurity Compliance Standards For Healthcare In 2025”
- “protecting Sensitive Business Information In Hybrid Environments”
Introduction
In this article, we dive into “role of blockchain in enhancing business cybersecurity”, giving you a full overview of what’s to come
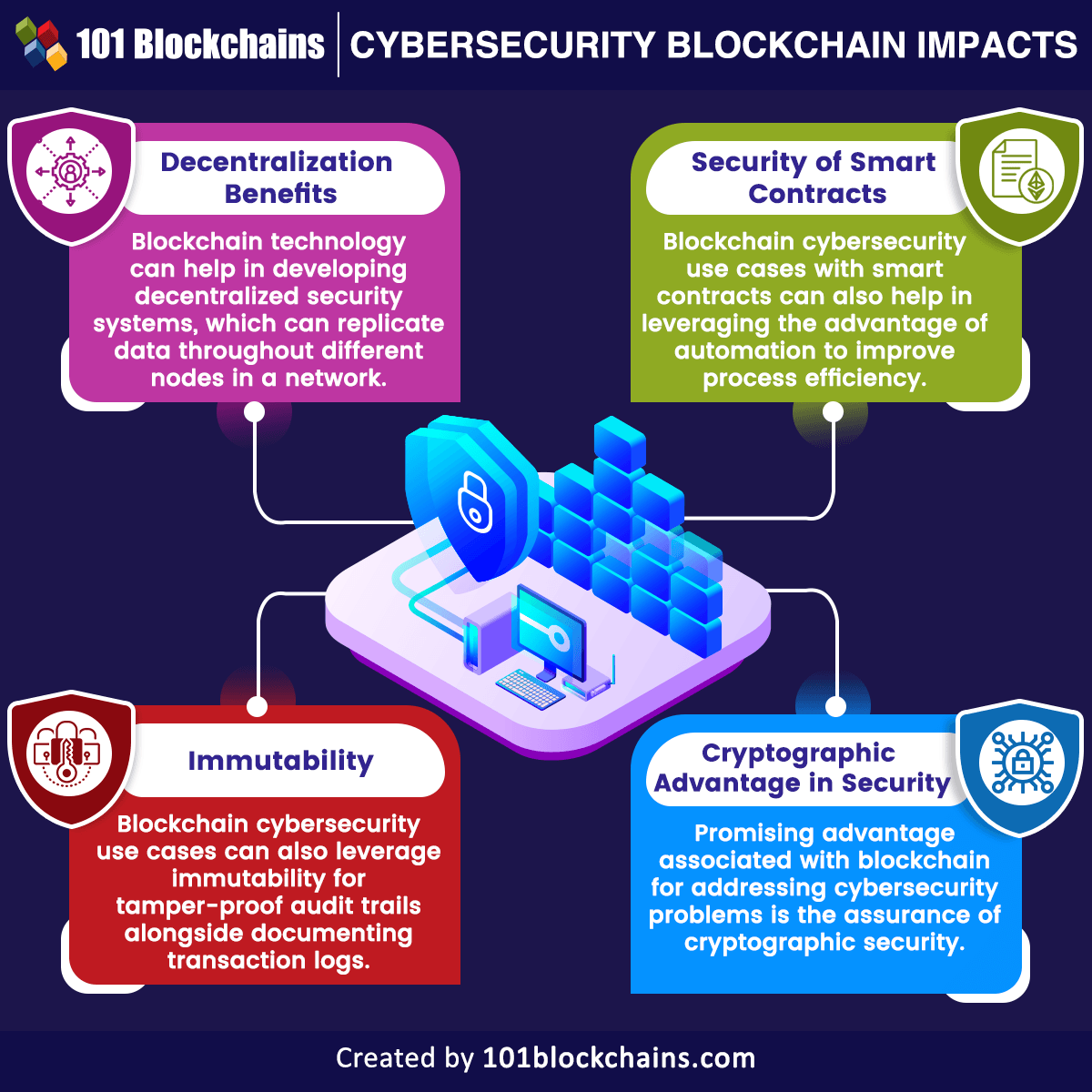
Traditional cybersecurity measures, while crucial, are often reactive, struggling to keep pace with the ever-evolving tactics of malicious actors. Blockchain technology, however, offers a proactive, revolutionary approach to bolstering business cybersecurity, promising a more secure and resilient future. This article delves into the often-overlooked aspects and "secret tips and tricks" of leveraging blockchain for enhanced business security, revealing its potential to transform how businesses protect their valuable data and assets.
1. Immutable Data Logging: The Foundation of Trust
One of blockchain’s most potent features is its immutability. Once data is recorded on a blockchain, it cannot be altered or deleted without detection. This characteristic is a game-changer for cybersecurity. Instead of relying on centralized logs that are vulnerable to manipulation, businesses can leverage blockchain to create an immutable audit trail of all critical security events. This includes access attempts, system changes, data modifications, and even security breaches themselves.
Secret Tip: Implement a blockchain-based system to log not just high-level security events, but also granular details like individual user actions within applications. This level of detail allows for precise forensic analysis in the event of a breach, significantly improving incident response time and effectiveness. Furthermore, consider integrating blockchain logging with existing SIEM (Security Information and Event Management) systems for a comprehensive security posture.
2. Secure Identity and Access Management (IAM): Beyond Passwords
Traditional IAM systems often rely on centralized databases vulnerable to breaches. Blockchain offers a decentralized alternative, enabling secure and verifiable digital identities. Instead of passwords, users can employ cryptographic keys managed through blockchain-based wallets. This eliminates the risk of password theft and significantly strengthens authentication processes.
Secret Trick: Explore the use of Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs). DIDs allow users to control their digital identities, while VCs provide verifiable attributes and permissions, enabling granular access control based on roles and authorization levels. This approach minimizes the attack surface and ensures only authorized individuals can access sensitive data and systems.
3. Enhanced Data Encryption and Protection: A Multi-Layered Defense
Blockchain’s cryptographic nature inherently enhances data encryption. By distributing data across multiple nodes, blockchain makes it significantly more difficult for attackers to access and decrypt sensitive information. Even if one node is compromised, the data remains secure on the other nodes.
Secret Tip: Combine blockchain with homomorphic encryption techniques. Homomorphic encryption allows computations to be performed on encrypted data without decryption, enabling secure data analysis and processing without compromising confidentiality. This is particularly useful for sensitive data analysis in regulated industries like healthcare and finance.
4. Supply Chain Security: Tracking Provenance and Authenticity

Blockchain’s ability to track the movement and provenance of goods and materials is invaluable for securing supply chains. By recording every step of the supply chain on a blockchain, businesses can verify the authenticity of products, detect counterfeits, and identify potential vulnerabilities.
Secret Trick: Utilize blockchain to create a "digital twin" of physical assets. This digital representation tracks the asset’s entire lifecycle, including its origin, movement, and maintenance history. This provides a transparent and verifiable record, enhancing security and accountability throughout the supply chain. Furthermore, integrate IoT sensors into the process for real-time tracking and monitoring.
5. Smart Contracts: Automating Security Protocols
Smart contracts are self-executing contracts with the terms of the agreement directly written into code. They can automate various security protocols, such as access control, data sharing, and incident response. This eliminates the need for manual intervention, reducing the risk of human error and improving efficiency.
Secret Tip: Develop smart contracts that automatically trigger security protocols based on predefined conditions. For instance, a smart contract could automatically revoke access privileges for a compromised user or initiate an investigation upon detection of suspicious activity. This proactive approach significantly enhances security response times.
6. Decentralized Storage: Resilience Against Single Points of Failure
Centralized storage systems are vulnerable to single points of failure. If the server is compromised, all the data is at risk. Blockchain-based decentralized storage solutions, like IPFS (InterPlanetary File System), offer greater resilience. Data is distributed across multiple nodes, making it significantly more difficult for attackers to access or destroy.
Secret Trick: Implement a hybrid approach, combining blockchain’s decentralized storage capabilities with traditional cloud storage for optimal performance and security. This allows for efficient data retrieval while maintaining the resilience and security offered by decentralization.
7. Enhanced Threat Detection and Response: Proactive Security Measures
Blockchain’s distributed nature and immutable ledger facilitate faster and more accurate threat detection. By analyzing blockchain data, businesses can identify patterns and anomalies indicative of malicious activity, enabling proactive mitigation strategies.
Secret Tip: Develop machine learning algorithms that analyze blockchain data to identify and predict potential threats. This proactive approach allows businesses to address security vulnerabilities before they can be exploited by attackers. Consider integrating blockchain-based threat intelligence platforms to stay ahead of emerging threats.
8. Regulatory Compliance and Auditability: Streamlining Compliance Processes
Blockchain’s transparency and immutability make it an ideal solution for meeting regulatory compliance requirements. The immutable record of transactions and events simplifies audits, reducing the time and cost associated with compliance.
Secret Trick: Implement a blockchain-based system to track and manage compliance-related data, such as KYC/AML (Know Your Customer/Anti-Money Laundering) information. This ensures regulatory compliance while enhancing data security and reducing the risk of fines and penalties.
Frequently Asked Questions (FAQs)
Q: Is blockchain a silver bullet for all cybersecurity problems?
A: No, blockchain is not a panacea. While it offers significant advantages, it’s not a standalone solution. It’s most effective when integrated with other cybersecurity measures as part of a layered security approach.
Q: What are the challenges of implementing blockchain for cybersecurity?
A: Implementing blockchain can be complex and costly, requiring specialized expertise. Scalability can also be a challenge, especially for large-scale deployments. Furthermore, the regulatory landscape surrounding blockchain is still evolving.
Q: How can I choose the right blockchain platform for my business?
A: The choice of blockchain platform depends on your specific needs and requirements. Consider factors such as scalability, security, privacy, and regulatory compliance when making your decision. Consult with blockchain experts to determine the most suitable platform for your organization.
Q: Is blockchain technology secure against all types of attacks?
A: While blockchain is highly secure, it’s not invulnerable. 51% attacks, where a majority of the network’s computing power is controlled by a malicious actor, remain a theoretical threat. However, well-designed and implemented blockchain systems are extremely resistant to most common cyberattacks.
Q: What is the future of blockchain in cybersecurity?
A: The future of blockchain in cybersecurity is bright. As the technology matures and becomes more widely adopted, we can expect to see even more innovative applications, further strengthening business cybersecurity and enhancing trust in the digital world.
This in-depth exploration of blockchain’s role in enhancing business cybersecurity reveals its transformative potential. By leveraging its unique characteristics, businesses can significantly improve their security posture, building a more resilient and trustworthy digital infrastructure. The "secret tips and tricks" outlined above highlight the often-overlooked nuances of implementing blockchain for enhanced security, offering a roadmap for businesses looking to embrace this revolutionary technology. Remember, a proactive and multi-layered approach, integrating blockchain with other security measures, is key to achieving optimal protection in today’s increasingly complex threat landscape.
[Source URL: (Insert a relevant URL here, for example, a reputable cybersecurity firm’s article on blockchain)]
Closure
Thank you for reading! Stay with us for more insights on “role of blockchain in enhancing business cybersecurity”.
Don’t forget to check back for the latest news and updates on “role of blockchain in enhancing business cybersecurity”!
We’d love to hear your thoughts about “role of blockchain in enhancing business cybersecurity”—leave your comments below!
Stay informed with our next updates on “role of blockchain in enhancing business cybersecurity” and other exciting topics.
