Protecting business data from ransomware in 2025
Related Articles
- “challenges Of Securing Multi-cloud Environments”
- “impact Of AI On Insider Threat Detection”
- How To Manage Privileged Access In Business IT Systems
- How To Prevent Insider Threats In Your Organization
- How To Train Employees In Business Data Security Awareness 2025
Introduction
In this article, we dive into Protecting business data from ransomware in 2025, giving you a full overview of what’s to come
Phishing attacks, social engineering, and insider threats are the primary vectors for ransomware infiltration. While robust firewalls and intrusion detection systems are essential, they are useless against a well-crafted phishing email that tricks an employee into clicking a malicious link or downloading an infected attachment.
-
Advanced Security Awareness Training: Forget generic training videos. Invest in immersive, simulated phishing campaigns that realistically replicate real-world threats. Regular, ongoing training should be mandatory for all employees, tailored to their specific roles and responsibilities. This should include training on recognizing sophisticated phishing techniques, understanding social engineering tactics, and reporting suspicious activity immediately.
-
Principle of Least Privilege: Implement the principle of least privilege rigorously. This means granting employees only the access rights absolutely necessary to perform their jobs. Restricting access to sensitive data minimizes the impact of a compromised account.
-
Zero Trust Security Model: Embrace a zero-trust architecture. Assume no user or device is inherently trustworthy, regardless of location or network access. Verify every access request, employing multi-factor authentication (MFA) for all accounts, including administrative accounts.
-
Regular Security Audits and Penetration Testing: Don’t rely solely on internal assessments. Engage external cybersecurity experts to conduct regular penetration testing and vulnerability assessments. These simulated attacks identify weaknesses in your security posture before attackers do.
2. Data Segmentation and Microsegmentation: Limiting the Blast Radius
Ransomware aims for widespread disruption. Limiting the impact of a successful attack is crucial. Data segmentation and microsegmentation are key strategies here.
-
Logical Segmentation: Divide your network into distinct segments, isolating sensitive data from less critical systems. If one segment is compromised, the ransomware’s spread is limited.
-
Microsegmentation: Take segmentation a step further by isolating individual servers and applications within a segment. This granular control significantly reduces the attack surface.
-
Data Classification and Access Control: Implement a robust data classification scheme. Categorize data based on sensitivity (e.g., confidential, sensitive, public). Apply appropriate access controls based on this classification, restricting access to sensitive data to authorized personnel only.
3. Advanced Endpoint Detection and Response (EDR): Proactive Threat Hunting
Traditional antivirus software is no longer sufficient. Ransomware often employs evasion techniques to bypass signature-based detection. Advanced EDR solutions provide proactive threat hunting capabilities.
-
Behavioral Analysis: EDR solutions monitor system behavior for anomalies indicative of malicious activity. This allows for early detection of ransomware even before it encrypts data.
-
Threat Intelligence Integration: Integrate your EDR solution with threat intelligence feeds to stay ahead of emerging threats. This provides real-time awareness of the latest ransomware variants and their tactics.
-
Automated Response Capabilities: Many EDR solutions offer automated response capabilities, allowing for automated containment and remediation of threats.
4. Immutable Backups: The Ultimate Defense
Regular backups are essential, but traditional backups are vulnerable to ransomware. Ransomware can encrypt backups as easily as it encrypts live data. Immutable backups are the solution.
-
Air-Gapped Backups: Store backups offline, completely disconnected from the network. This prevents ransomware from reaching them.
-
Cloud-Based Immutable Backups: Utilize cloud-based backup solutions with immutability features. These solutions prevent the modification or deletion of backups, even by an administrator.
-
Versioning and Retention Policies: Implement robust versioning and retention policies to ensure you can restore data from a point before the attack.
5. Extended Detection and Response (XDR): A Holistic Approach
XDR expands on EDR by integrating data from various security sources, such as endpoints, networks, clouds, and email. This provides a more comprehensive view of the security landscape.
-
Unified Security Monitoring: XDR provides a single pane of glass for monitoring security events across your entire infrastructure.
-
Improved Threat Detection: By correlating data from multiple sources, XDR can identify threats that might be missed by individual security tools.
-
Faster Incident Response: XDR facilitates faster incident response by providing a clear picture of the attack and its impact.
6. Regular Security Awareness Training and Phishing Simulations
We’ve already touched on this, but it warrants reiteration. Employees are the weakest link. Regular and engaging security awareness training, coupled with realistic phishing simulations, is crucial. The goal is to build a security-conscious culture.
7. Patch Management and Software Updates: Closing the Gaps
Software vulnerabilities are a prime target for ransomware. Maintain a rigorous patch management program, ensuring all software, including operating systems, applications, and firmware, is up-to-date. Automated patch management solutions can streamline this process.
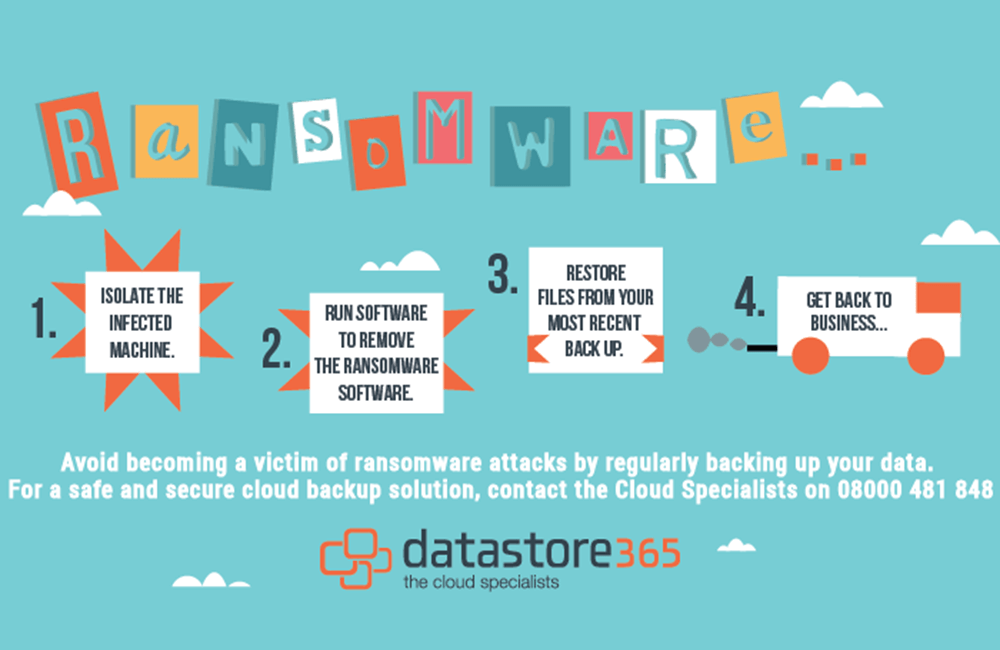
8. Incident Response Plan: Preparation is Key
Having a well-defined incident response plan is crucial. This plan should outline steps to take in the event of a ransomware attack, including communication protocols, data recovery procedures, and legal considerations. Regularly test and update this plan to ensure its effectiveness.
Frequently Asked Questions (FAQs)
-
Q: Is ransomware truly unavoidable?
- A: While completely eliminating the risk of ransomware is impossible, significantly reducing its impact is achievable through a multi-layered security approach. The strategies outlined above dramatically improve your chances of survival.
-
Q: How much should I invest in ransomware protection?
- A: The cost of a ransomware attack far outweighs the cost of prevention. Consider the potential financial losses, reputational damage, and legal liabilities. Invest strategically in a comprehensive security strategy that addresses all aspects of ransomware protection.
-
Q: What should I do if I’m attacked?
- A: Immediately disconnect affected systems from the network to prevent further spread. Contact your incident response team or a cybersecurity professional. Do not pay the ransom unless explicitly advised by law enforcement. Focus on data recovery from your immutable backups.
-
Q: Are cloud-based solutions immune to ransomware?
- A: No, cloud-based solutions are not immune, but they offer enhanced security features like immutability and robust access controls. Choose reputable cloud providers with strong security credentials.
-
Q: How can I stay updated on the latest ransomware threats?
- A: Subscribe to security news feeds, follow cybersecurity experts on social media, and attend industry conferences. Leverage threat intelligence feeds integrated into your security solutions.
In conclusion, protecting your business data from ransomware in 2025 and beyond requires a proactive, multi-layered approach. It’s not about a single solution but a holistic strategy that combines technological safeguards with a security-conscious culture. By implementing the strategies discussed above, you can significantly reduce your risk and protect your valuable data from the ever-evolving threat of ransomware. Remember, prevention is far cheaper and less disruptive than recovery.
[Source URL: https://www.cisa.gov/cybersecurity](This is a placeholder. Replace with a relevant and credible source URL from a government agency or reputable cybersecurity firm.)
Closure
We hope this article has helped you understand everything about Protecting business data from ransomware in 2025. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on Protecting business data from ransomware in 2025!
Feel free to share your experience with Protecting business data from ransomware in 2025 in the comment section.
Keep visiting our website for the latest trends and reviews.