Key strategies for securing business data in hybrid cloud environments
Related Articles
- “challenges Of Securing Multi-cloud Environments”
- “how To Train Employees To Recognize Phishing Attacks”
- “cloud Security Trends For Business Owners 2025”
- “benefits Of Using Multi-factor Authentication For Businesses”
- “emerging Cybersecurity Threats For Supply Chain Operations In 2025”
Introduction
In this article, we dive into Key strategies for securing business data in hybrid cloud environments, giving you a full overview of what’s to come
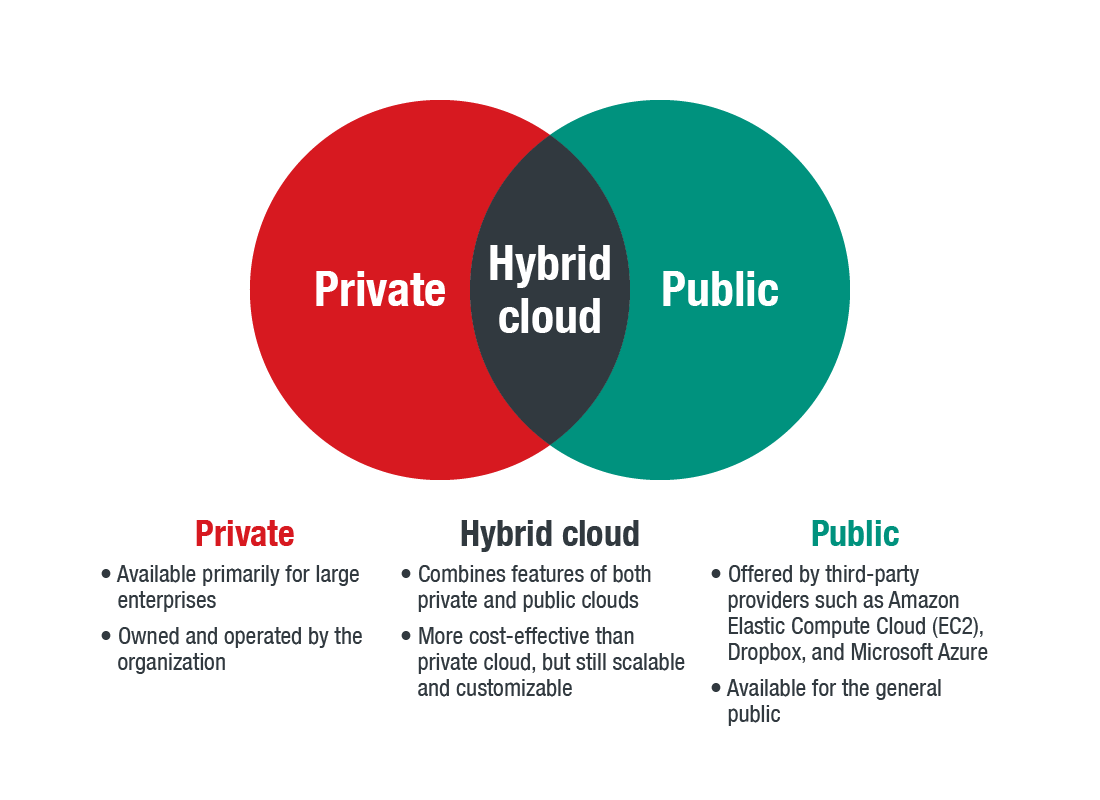
This flexibility offers significant advantages, but it also introduces a complex web of security challenges. Securing data in a hybrid cloud environment requires a multi-layered, proactive strategy that goes beyond basic security measures. This article delves into the often-overlooked strategies and "big secret" tips that can significantly enhance your data protection.

1. Visibility and Control: The Foundation of Hybrid Cloud Security
The first, and arguably most crucial, step is achieving comprehensive visibility and control across your entire IT landscape. This means having a unified view of all your data, regardless of its location – on-premises, in a private cloud, or in a public cloud. Many organizations struggle with this, relying on disparate security tools that lack integration. The "secret" here lies in implementing a Security Information and Event Management (SIEM) system capable of aggregating logs and alerts from all your environments. This provides a single pane of glass for monitoring security events, identifying anomalies, and responding to threats effectively. Beyond SIEM, consider Security Orchestration, Automation, and Response (SOAR) tools to automate incident response and streamline security operations. Don’t underestimate the power of centralized logging – it’s the cornerstone of effective threat detection and response in a hybrid environment.
Pro Tip: Invest in a SIEM solution that supports advanced analytics and machine learning capabilities. These can help identify subtle threats that might be missed by traditional rule-based systems.
2. Microsegmentation: Isolating Your Valuable Assets
Network segmentation has long been a security best practice, but in a hybrid cloud, it requires a more sophisticated approach. Microsegmentation divides your network into smaller, isolated segments, limiting the impact of a security breach. If a malicious actor compromises a system in one segment, they won’t automatically have access to other sensitive data. This is particularly crucial in hybrid environments where different workloads reside in different locations. Implementing microsegmentation requires careful planning and the use of advanced networking technologies like software-defined networking (SDN) and network virtualization.
Pro Tip: Prioritize microsegmentation for critical systems and sensitive data. Map your network thoroughly to identify dependencies and potential vulnerabilities before implementing segmentation.
3. Data Loss Prevention (DLP): Protecting Data in Transit and at Rest
Data loss prevention is paramount in any environment, but it’s especially critical in a hybrid cloud where data moves between various locations. A robust DLP strategy involves implementing technologies that monitor and control data movement, both within your network and across the internet. This includes encrypting data at rest and in transit, using strong access controls, and employing data loss prevention tools that can identify and prevent sensitive data from leaving your control. Remember that DLP is not just about preventing accidental data loss; it’s also about preventing malicious data exfiltration.
Pro Tip: Don’t just rely on default security settings. Configure your DLP tools to specifically identify and protect your most sensitive data based on its classification and context.
4. Identity and Access Management (IAM): The Gatekeeper of Your Data
IAM is the foundation of secure access control. In a hybrid cloud, you need a centralized IAM system that manages user identities and access rights across all your environments. This prevents the creation of security silos and ensures consistent access policies. Implement strong authentication mechanisms, such as multi-factor authentication (MFA), and leverage role-based access control (RBAC) to grant users only the necessary privileges. Regularly review and audit access rights to ensure they remain appropriate.
Pro Tip: Implement a "least privilege" access model, granting users only the minimum access rights required to perform their jobs. This significantly reduces the potential impact of compromised accounts.
5. Cloud Security Posture Management (CSPM): Continuous Monitoring and Assessment
CSPM tools provide continuous monitoring and assessment of your cloud security posture. They can automatically identify misconfigurations, vulnerabilities, and compliance issues across your various cloud environments. This is crucial in a hybrid cloud, where the complexity of managing multiple environments increases the risk of security gaps. CSPM tools help you proactively identify and address these issues before they can be exploited.
Pro Tip: Integrate your CSPM tools with your SIEM and SOAR systems to create a fully automated security monitoring and response system.
6. Regular Security Audits and Penetration Testing: Proactive Threat Hunting
Regular security audits and penetration testing are essential for identifying vulnerabilities and weaknesses in your hybrid cloud security posture. These should be performed regularly, ideally by an independent third party, to ensure objectivity and thoroughness. Penetration testing simulates real-world attacks to identify vulnerabilities that might be missed by other security measures. The findings from these assessments should be used to continuously improve your security posture.
Pro Tip: Don’t limit your penetration testing to just your network infrastructure. Include your applications and data stores to identify vulnerabilities across your entire environment.
7. Disaster Recovery and Business Continuity: Planning for the Inevitable
Disasters can strike at any time, and having a robust disaster recovery and business continuity plan is crucial for minimizing the impact of any disruption. Your plan should include procedures for recovering data and applications from all your environments, including on-premises, private cloud, and public cloud. Regularly test your disaster recovery plan to ensure its effectiveness.
Pro Tip: Consider using cloud-based disaster recovery solutions to ensure your ability to recover quickly and efficiently, regardless of the location of the disaster.
8. Employee Training and Awareness: The Human Element
The human element is often the weakest link in any security chain. Regular employee training and awareness programs are crucial for educating employees about security best practices and the importance of reporting suspicious activity. This includes training on phishing scams, social engineering attacks, and secure password management.
Pro Tip: Use engaging training methods, such as simulations and gamification, to make security training more effective and memorable.
Frequently Asked Questions (FAQs)
Q: What are the biggest challenges in securing a hybrid cloud environment?
A: The biggest challenges include managing the complexity of multiple environments, ensuring consistent security policies across all locations, maintaining visibility and control over data, and addressing the skills gap in cloud security expertise.
Q: How can I ensure compliance with regulations in a hybrid cloud environment?
A: Implement a robust compliance program that includes regular audits, monitoring, and reporting. Utilize tools that help automate compliance checks and integrate with your security tools.
Q: What is the cost of securing a hybrid cloud environment?
A: The cost varies depending on the size and complexity of your environment, the security tools you choose, and the level of expertise you have in-house. However, the cost of a security breach can far outweigh the cost of implementing robust security measures.
Q: How can I choose the right security tools for my hybrid cloud environment?
A: Consider your specific needs and requirements, including the size and complexity of your environment, your compliance obligations, and your budget. Look for tools that integrate seamlessly with your existing infrastructure and provide comprehensive visibility and control.
This in-depth exploration of key strategies for securing business data in hybrid cloud environments provides a strong foundation for building a robust and resilient security posture. By implementing these strategies and employing the "secret" tips outlined above, organizations can significantly reduce their risk of data breaches and maintain the integrity of their valuable business information. Remember that security is an ongoing process, not a one-time project. Continuous monitoring, assessment, and adaptation are essential for staying ahead of evolving threats.
[Source URL: (Insert a relevant URL from a reputable cybersecurity source here, e.g., a NIST publication or a major cybersecurity vendor’s website)]
Closure
We hope this article has helped you understand everything about Key strategies for securing business data in hybrid cloud environments. Stay tuned for more updates!
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about Key strategies for securing business data in hybrid cloud environments—leave your comments below!
Stay informed with our next updates on Key strategies for securing business data in hybrid cloud environments and other exciting topics.
