“importance of supply chain security in preventing data breaches”
Related Articles
- “top Cybersecurity Threats To Small Businesses In 2025”
- “best Practices For Implementing Zero Trust Architecture In Business”
- “best Tools For Monitoring Business Data Access”
- “data Security Trends For Financial Institutions In 2025”
- “impact Of Quantum Computing On Business Data Encryption”
Introduction
Discover everything you need to know about “importance of supply chain security in preventing data breaches”
While many focus on internal security measures, a critical, often overlooked, vulnerability lies within the sprawling network of the supply chain. Strengthening supply chain security is no longer a nice-to-have; it’s a fundamental necessity for preventing devastating data breaches. This article delves into the often-hidden aspects of supply chain security and reveals big secret tips and tricks to mitigate the risk.
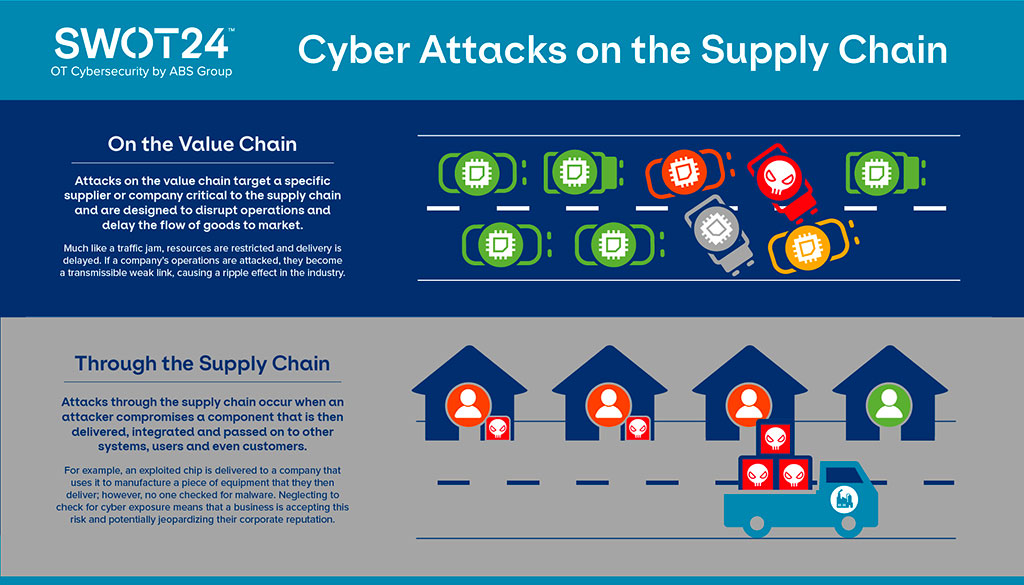
1. Beyond the Firewall: Understanding the Expanded Attack Surface
The traditional view of security often centers around the perimeter of a company’s network, focusing on firewalls and intrusion detection systems. However, the modern supply chain significantly expands this attack surface. It encompasses a vast network of vendors, suppliers, distributors, logistics providers, and third-party service providers, each with its own security posture (or lack thereof). A single weak link in this chain can provide a backdoor for malicious actors to infiltrate your systems and access sensitive data. This isn’t just about physical goods; it includes the flow of data throughout the entire process, from design and manufacturing to delivery and beyond. Think of software updates, cloud services used by suppliers, and even the email communications exchanged with partners – all potential entry points for breaches.
2. The Insider Threat: Employees and the Supply Chain
Internal threats are a significant concern, and this extends to the employees of your supply chain partners. A disgruntled employee, a compromised account, or even unintentional negligence can provide attackers with access to your systems. Therefore, background checks, employee training programs on security best practices, and robust access control measures should extend beyond your internal workforce to encompass your supply chain partners. Regular audits and assessments of your partners’ security protocols are essential to identify and mitigate these risks. This includes understanding their own employee security practices and their ability to detect and respond to insider threats.
3. Third-Party Risk Management: A Proactive Approach
Third-party risk management (TPRM) is not just a compliance exercise; it’s a critical component of effective supply chain security. A robust TPRM program involves identifying all third-party vendors, assessing their security risks, implementing appropriate controls, and continuously monitoring their performance. This requires a structured approach, often involving questionnaires, security audits, and penetration testing. The goal is to establish a baseline level of security across your supply chain, ensuring that your partners are committed to protecting your data as diligently as you are. This isn’t a one-time process; continuous monitoring and reassessment are crucial, especially in dynamic environments where vendors and partnerships change frequently.
4. Secure Data Sharing and Collaboration: The Power of Encryption
The exchange of sensitive data with supply chain partners is unavoidable. However, the manner in which this data is shared significantly impacts your security posture. Encryption is paramount. Data should be encrypted both in transit and at rest, protecting it from unauthorized access even if a breach occurs. Furthermore, secure communication channels, such as VPNs, should be used to prevent eavesdropping. Implementing robust access controls, limiting access to only authorized personnel and devices, and regularly reviewing access permissions are crucial for maintaining data confidentiality. The use of secure file transfer protocols (SFTP) over insecure methods like email significantly reduces the risk of data exposure.
5. Visibility and Monitoring: Tracking the Flow of Data
Maintaining complete visibility into your supply chain’s data flow is essential for effective security. Implementing monitoring tools and technologies that track data movement, access attempts, and potential anomalies can provide early warning signs of a breach. This includes monitoring network traffic, log files, and security alerts from your partners. This proactive approach allows for quicker identification and response to potential threats, minimizing the impact of a breach. Centralized logging and security information and event management (SIEM) systems can help consolidate and analyze data from various sources, providing a holistic view of your supply chain’s security posture.

6. Vulnerability Management: Proactive Patching and Updates
Software vulnerabilities are a constant source of risk, and this extends to the software and systems used by your supply chain partners. Regular vulnerability assessments and penetration testing are essential to identify and remediate potential weaknesses. A robust patch management process ensures that all software and systems are kept up-to-date with the latest security patches, mitigating the risk of exploitation. This requires collaboration with your partners to ensure that they are also actively managing vulnerabilities within their own systems. Failing to address vulnerabilities creates a significant weakness that attackers can easily exploit.
7. Incident Response Planning: Preparation is Key
Even with the best security measures in place, breaches can still occur. Having a well-defined incident response plan is crucial for minimizing the impact of a breach. This plan should outline the steps to be taken in the event of a security incident, including communication protocols, data recovery procedures, and notification processes. Regularly testing and updating the incident response plan is essential to ensure its effectiveness. This plan should extend to your supply chain partners, ensuring coordinated response in the event of a breach affecting multiple organizations.
8. Building a Culture of Security: Collaboration and Communication
Supply chain security is not solely a technological challenge; it requires a cultural shift within your organization and across your supply chain. Promoting a culture of security involves educating employees and partners about the importance of security best practices, fostering open communication, and encouraging reporting of potential security incidents. Regular training programs, security awareness campaigns, and clear communication channels are essential for building a robust security culture. This collaborative approach fosters a shared responsibility for security, making your entire supply chain more resilient to attacks.
Frequently Asked Questions (FAQs)
Q: How can I assess the security posture of my supply chain partners?
A: You can use a combination of methods, including questionnaires, security audits (both internal and third-party), penetration testing, and reviewing their existing security certifications (e.g., ISO 27001). Regular communication and collaboration are also crucial to understand their security practices and commitment.
Q: What are the legal and regulatory implications of supply chain security failures?
A: Depending on your industry and location, there are numerous regulations (e.g., GDPR, CCPA, HIPAA) that mandate specific security measures. Failure to comply can result in significant fines, legal action, and reputational damage. Data breaches can also lead to class-action lawsuits.
Q: How can I balance security with the efficiency of my supply chain?
A: Effective supply chain security doesn’t have to be a hindrance to efficiency. By implementing a well-planned and integrated approach, you can minimize disruptions while maximizing security. Automation and streamlined processes can improve efficiency while enhancing security.
Q: What are some cost-effective measures to improve supply chain security?
A: Prioritizing risk assessment allows you to focus resources on the most critical areas. Employee training, implementing strong password policies, and using free or low-cost security tools can make a significant difference. Collaboration with partners to share best practices can also reduce overall costs.
Q: How often should I reassess my supply chain security?
A: Regular reassessment is crucial, ideally at least annually, or more frequently if there are significant changes in your supply chain or the threat landscape. Continuous monitoring and vulnerability scanning are also essential for proactive security management.
This in-depth exploration highlights the critical role of supply chain security in preventing data breaches. By implementing these strategies and fostering a culture of security, businesses can significantly reduce their vulnerability and protect their valuable data. Remember, a strong supply chain is the backbone of a resilient organization. Investing in supply chain security is not just an expense; it’s an investment in the long-term health and sustainability of your business.
[Source URL: (Insert a relevant URL from a reputable source on supply chain security, such as a government agency website, industry association, or reputable cybersecurity firm)]
Closure
Thank you for reading! Stay with us for more insights on “importance of supply chain security in preventing data breaches”.
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “importance of supply chain security in preventing data breaches”—leave your comments below!
Keep visiting our website for the latest trends and reviews.
