“how to secure IoT devices in corporate networks”
Related Articles
- “impact Of Quantum Computing On Business Data Encryption”
- “best Practices For Implementing Zero Trust Architecture In Business”
- “ransomware Recovery Strategies For Enterprises In 2025”
- “how AI Is Reshaping Data Security Strategies In 2025”
- “data Security Trends For Financial Institutions In 2025”
Introduction
Join us as we explore “how to secure IoT devices in corporate networks”, packed with exciting updates
However, this connectivity comes at a cost: a significantly expanded attack surface vulnerable to cyber threats. Securing IoT devices within corporate networks is no longer a luxury; it’s a critical necessity for maintaining business continuity, protecting sensitive data, and complying with regulatory requirements. This article delves into the often-overlooked strategies and "big secret" techniques for effectively securing your organization’s IoT ecosystem.
I. The Progression of IoT Security Best Practices
The journey of securing IoT devices hasn’t been linear. Early deployments often prioritized functionality over security, leading to a landscape riddled with vulnerabilities. The progression can be broadly categorized into three phases:
Phase 1: Reactive Security (Early 2010s): This era was characterized by a reactive approach. Security measures were implemented after vulnerabilities were discovered and exploited, often in response to high-profile breaches. The focus was primarily on patching known vulnerabilities and implementing basic firewall rules. This approach proved insufficient as the complexity and scale of IoT deployments grew.
Phase 2: Proactive Security (Mid-2010s – Present): Organizations began adopting a more proactive stance. This involved implementing robust security protocols during the device selection process, focusing on secure-by-design principles. Network segmentation, access control lists (ACLs), and intrusion detection systems (IDS) became standard security practices. However, the lack of standardization and interoperability between IoT devices remained a significant challenge.
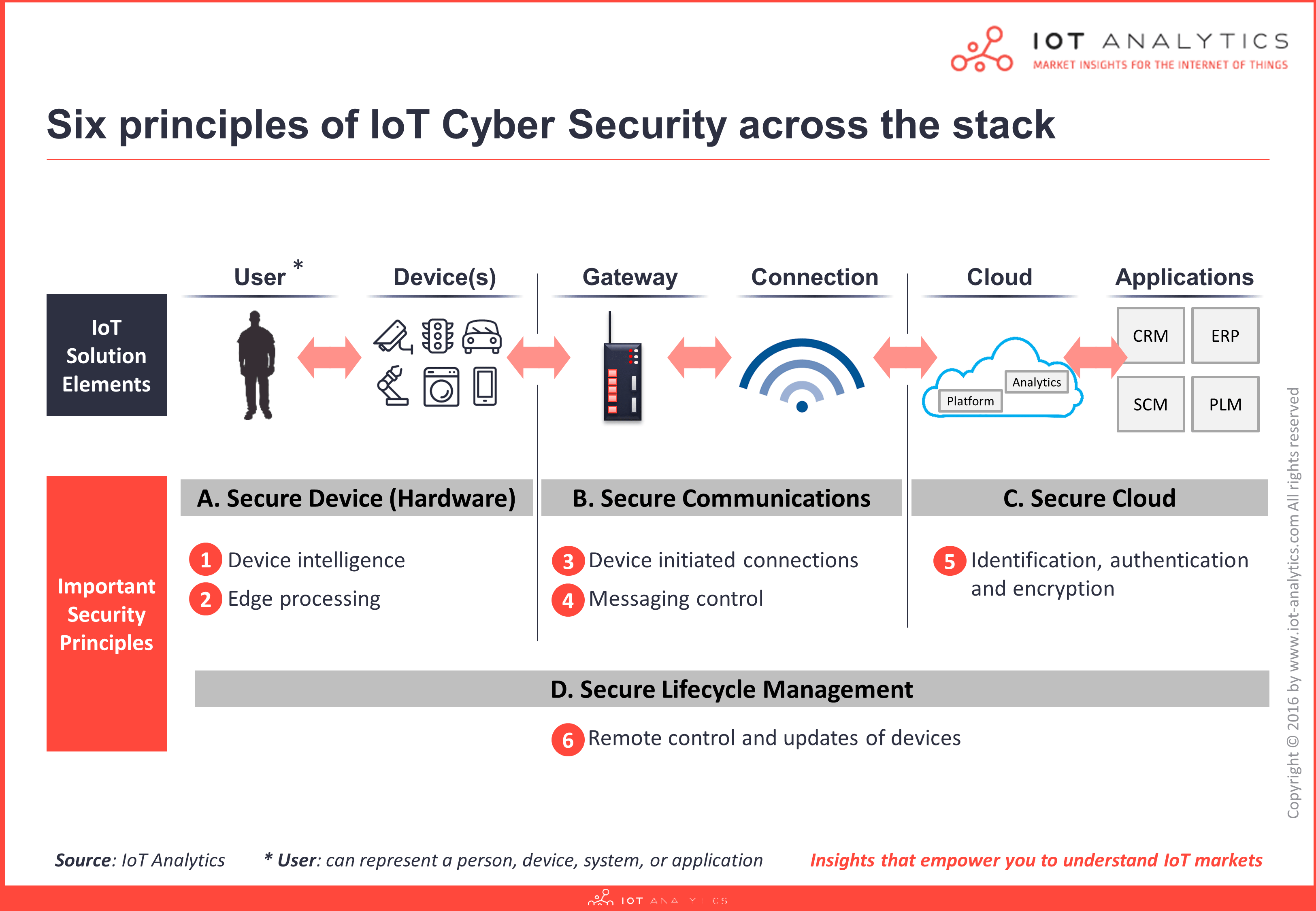
Phase 3: Intelligent and Predictive Security (Present and Future): The current phase emphasizes leveraging advanced technologies like AI and machine learning for threat detection and response. This involves implementing security information and event management (SIEM) systems, employing behavioral analytics to identify anomalies, and utilizing automated incident response mechanisms. The focus is shifting towards a holistic approach that encompasses the entire lifecycle of an IoT device, from procurement to decommissioning.
II. Big Secret Tips and Tricks for Securing IoT Devices
While many standard security practices are widely known, certain "big secret" techniques often remain underutilized or misunderstood. These strategies, when implemented effectively, can significantly bolster your IoT security posture:
1. Device Hardening Beyond the Basics: Most organizations focus on software updates. However, physical security is equally crucial. This includes:
- Secure Boot and Firmware Updates: Implement secure boot mechanisms to prevent unauthorized firmware modifications. Regularly update firmware to patch known vulnerabilities. Consider using a centralized update management system for efficient and consistent patching.
- Physical Tamper Detection: Utilize tamper-evident seals and sensors to detect unauthorized access or modifications to the device.
- Inventory Management: Maintain a comprehensive inventory of all IoT devices, including their location, model, firmware version, and security configuration. This is vital for tracking devices, identifying vulnerabilities, and managing updates.
2. Network Segmentation and Micro-segmentation: Don’t treat your IoT devices as part of your general corporate network. Segment your network into smaller, isolated zones based on device functionality and criticality. Micro-segmentation allows for even finer-grained control, isolating individual devices or groups of devices. This limits the impact of a compromise, preventing attackers from easily moving laterally across your network.
3. Zero Trust Architecture: Embrace a Zero Trust model, where no device or user is implicitly trusted. This involves verifying every access request, regardless of its origin. Implement strong authentication mechanisms, such as multi-factor authentication (MFA), and use granular access control lists to restrict access to specific resources.
4. Leveraging Anomaly Detection and Behavioral Analytics: Traditional signature-based intrusion detection systems are often ineffective against sophisticated IoT attacks. Employ anomaly detection techniques that analyze device behavior and identify deviations from established baselines. Behavioral analytics can pinpoint malicious activity even before known signatures are available.
5. Secure Communication Protocols: Prioritize the use of secure communication protocols like TLS/SSL and DTLS for all IoT device communications. Avoid using insecure protocols like Telnet or FTP. Implement encryption at both the network and application layers to protect data in transit and at rest.
6. Vulnerability Management as a Continuous Process: Regularly scan your IoT devices for vulnerabilities using automated vulnerability scanners. Prioritize patching critical vulnerabilities immediately. Implement a robust vulnerability management program that integrates with your incident response plan.
7. Secure Device Provisioning and Management: Employ secure device provisioning processes to prevent unauthorized devices from joining your network. Use a centralized device management platform to configure, monitor, and manage your IoT devices remotely. This allows for efficient updates, security configuration changes, and remote troubleshooting.
8. Data Minimization and Encryption: Collect only the necessary data from your IoT devices. Avoid storing sensitive data on the devices themselves. Encrypt all data at rest and in transit to protect it from unauthorized access.
9. Regular Security Audits and Penetration Testing: Conduct regular security audits and penetration testing to identify vulnerabilities and assess the effectiveness of your security controls. Simulate real-world attacks to identify weaknesses and improve your overall security posture.
10. Employee Training and Awareness: Educate your employees about IoT security risks and best practices. Train them to identify phishing attempts and other social engineering attacks that target IoT devices. Develop clear security policies and procedures that are easily understood and followed.
III. The "Big Secret" Unveiled: Context-Aware Security
The biggest secret to securing IoT devices lies in leveraging context-aware security. This involves understanding the environment in which your IoT devices operate and adapting your security measures accordingly. This means:
- Location Awareness: Security policies should be tailored to the location of the device. For example, a device deployed in a high-security area may require more stringent access controls than one in a less sensitive location.
- Device Context: Consider the device’s role and function within your network. A device with limited processing power and memory will have different security requirements than a more powerful device.
- Data Context: The sensitivity of the data handled by a device will dictate the level of security required. Devices handling critical financial data should have higher security measures than those handling less sensitive data.
- User Context: Identify the users who interact with the device and their level of authorization. Implement appropriate access controls to limit access to sensitive data and functions.
By integrating these contextual factors into your security strategy, you can create a more dynamic and effective security posture that adapts to the ever-changing landscape of IoT threats.
IV. Conclusion
Securing IoT devices in corporate networks is a multifaceted challenge requiring a comprehensive and proactive approach. While standard security practices are essential, the "big secret" lies in understanding the nuances of your specific IoT environment and adapting your security strategy accordingly. By embracing context-aware security, leveraging advanced technologies, and fostering a culture of security awareness, organizations can significantly reduce their risk and protect their valuable assets. The journey to secure IoT is ongoing, requiring continuous monitoring, adaptation, and a commitment to staying ahead of emerging threats.
V. Frequently Asked Questions (FAQs)
Q1: What are the most common vulnerabilities in IoT devices?
A1: Common vulnerabilities include weak or default passwords, insecure communication protocols, lack of firmware updates, insufficient authentication mechanisms, and lack of encryption.
Q2: How can I identify vulnerable IoT devices on my network?
A2: Use vulnerability scanners and network monitoring tools to identify devices with known vulnerabilities. Regularly update device firmware and software to patch known vulnerabilities.
Q3: What is the best way to manage IoT device updates?
A3: Utilize a centralized update management system to efficiently and consistently patch your IoT devices. Schedule regular updates and test them in a controlled environment before deploying them to production.
Q4: How can I ensure the security of data collected by IoT devices?
A4: Encrypt all data at rest and in transit. Implement access control mechanisms to restrict access to sensitive data. Minimize data collection to only what is necessary.
Q5: What role does employee training play in IoT security?
A5: Employee training is crucial for raising awareness about IoT security risks and best practices. Train employees to identify phishing attempts and other social engineering attacks.
Source URL: [Insert a relevant URL from a reputable cybersecurity source here, e.g., a NIST publication or a reputable security vendor’s website] For example: https://www.nist.gov/ (Replace with a more specific and relevant URL if possible)
Closure
We hope this article has helped you understand everything about “how to secure IoT devices in corporate networks”. Stay tuned for more updates!
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “how to secure IoT devices in corporate networks”—leave your comments below!
Keep visiting our website for the latest trends and reviews.
