How to safeguard financial data from phishing attacks
Related Articles
- “how To Choose The Best Cybersecurity Consultant For Your Business”
- “why Your Business Needs Endpoint Detection Tools In 2025”
- “impact Of Remote Work On Data Security Risks In 2025”
- “how To Train Employees To Prevent Phishing Attacks”
- “challenges Of Securing Multi-cloud Environments”
Introduction
Join us as we explore How to safeguard financial data from phishing attacks, packed with exciting updates
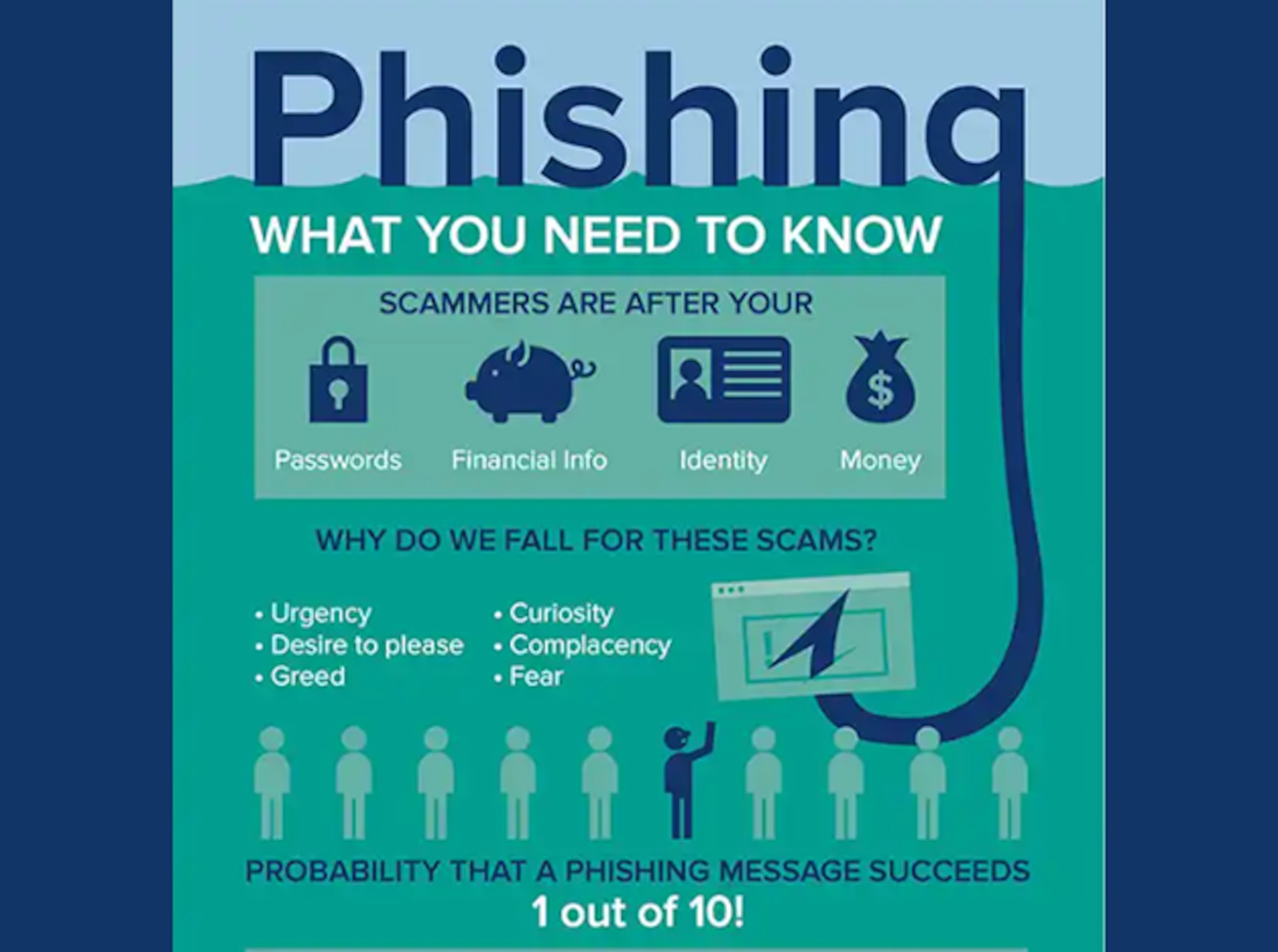
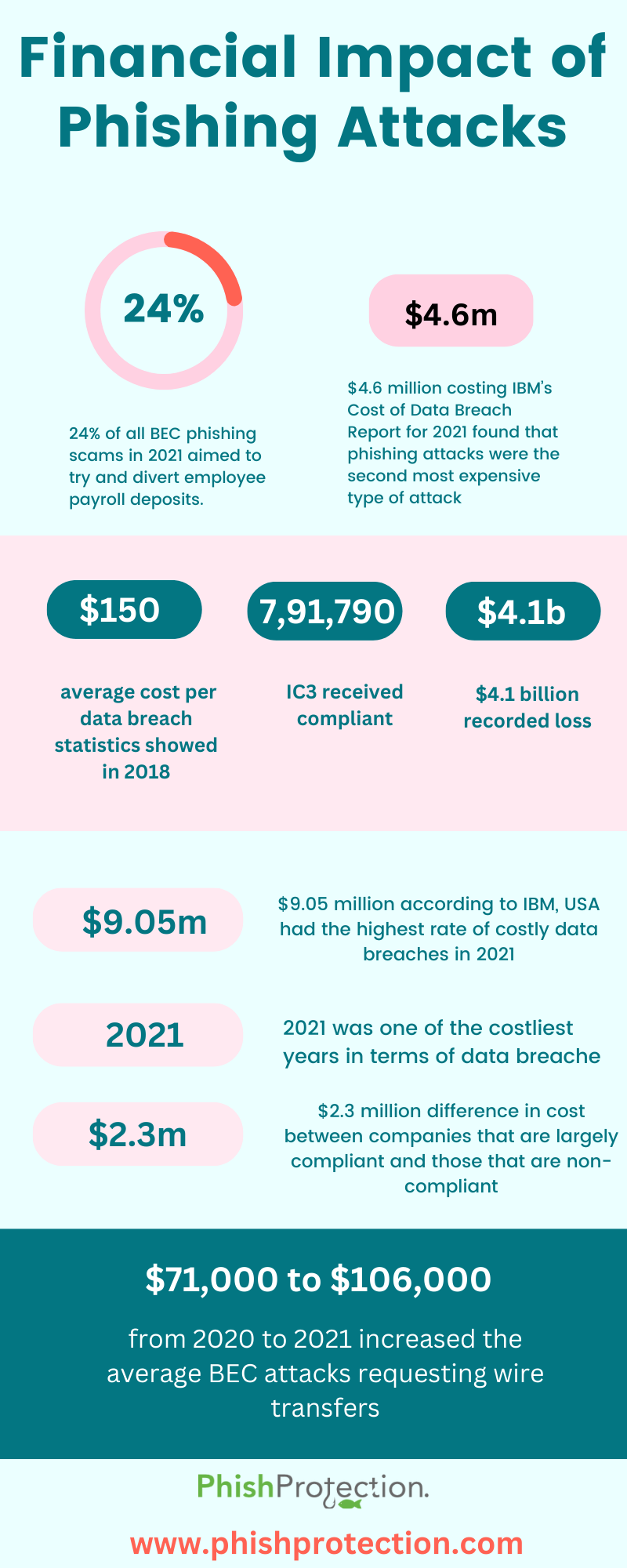
These sophisticated scams, often disguised as legitimate communications, can lead to devastating consequences, including identity theft, financial losses, and reputational damage. While awareness is crucial, simply knowing about phishing isn’t enough. This in-depth guide unveils big secret tips and tricks to significantly bolster your defenses against these insidious attacks, empowering you to safeguard your financial data effectively.
1. Beyond the Obvious: Deep Dive into Phishing Email Detection
Most advice on avoiding phishing focuses on identifying obvious red flags like poor grammar, misspellings, and suspicious sender addresses. While these are important, sophisticated phishing campaigns employ increasingly subtle techniques. To truly master phishing detection, you need to delve deeper:
- Analyze the Email Header: Don’t just look at the "From" field. Examine the email header using your email client’s options (often accessible by viewing the email source or properties). This reveals the email’s true origin, including the sending server’s IP address and routing information. Discrepancies between the displayed sender and the actual sender are major red flags.
- URL Inspection: Hover your mouse over any links before clicking. The URL displayed in the tooltip should match the intended destination. Phishing emails often mask malicious URLs behind legitimate-looking text. Manually type the URL into your browser instead of clicking the link directly.
- Attachment Scrutiny: Never open attachments from unknown senders or those that seem unexpected. Even if the sender appears legitimate, a malicious attachment can compromise your system. If you’re unsure, contact the sender directly through a verified channel (e.g., their official website) to confirm the attachment’s authenticity.
- Unexpected Urgency: Phishing emails often create a sense of urgency, pressuring you to act quickly without thinking. Legitimate organizations rarely use such tactics. Take your time, verify information, and avoid impulsive actions.
- Personalized Phishing: Modern phishing attacks are highly personalized, using information gleaned from data breaches or social media to create convincing messages. Be wary of emails that seem to know too much about you.
2. Strengthening Your Digital Fortress: Password Management and Multi-Factor Authentication (MFA)
Strong passwords and MFA are the cornerstones of online security, acting as crucial barriers against phishing attacks. However, simply having these isn’t enough. You must implement them effectively:
- Password Managers: Using a reputable password manager is paramount. These tools generate strong, unique passwords for each account, eliminating the need to remember complex combinations. They also provide features to detect compromised passwords.
- MFA Implementation: Enable MFA wherever possible, especially for financial accounts. MFA adds an extra layer of security, requiring a second verification factor (e.g., a code from your phone) beyond your password. This significantly reduces the risk of unauthorized access even if your password is compromised.
- Password Hygiene: Regularly update your passwords, especially for critical accounts. Consider using a password rotation schedule to ensure consistent password strength. Avoid reusing passwords across different accounts. A breach in one account could compromise others.
3. Device Security: The Unsung Hero of Phishing Defense
Your devices are the front line of defense against phishing attacks. Neglecting their security weakens your overall protection:
- Software Updates: Keep your operating system, antivirus software, and all other applications updated. Updates often include security patches that address vulnerabilities exploited by phishing attacks.
- Antivirus and Anti-malware Software: Use reputable antivirus and anti-malware software and keep it active. These tools can detect and block malicious attachments and websites associated with phishing campaigns.
- Firewall Protection: A firewall acts as a barrier between your device and the internet, blocking unauthorized access attempts. Ensure your firewall is enabled and configured correctly.
- Regular Security Scans: Perform regular security scans to detect and remove malware. Consider using both on-demand and scheduled scans for comprehensive protection.
4. Suspicious Website Detection: Beyond the "https"
While the "https" prefix indicates a secure connection, it’s not a foolproof indicator of legitimacy. Phishing websites can also use "https," making visual inspection insufficient. Here’s how to go beyond the basics:
- Website Verification: Before entering any sensitive information, verify the website’s authenticity. Look for official contact information, a physical address, and other details confirming its legitimacy.
- Certificate Inspection: Examine the website’s security certificate. Click the padlock icon in your browser’s address bar and check the certificate details. Ensure the certificate is valid and issued by a trusted authority.
- URL Examination: Carefully examine the website’s URL. Look for typos, unusual characters, or inconsistencies. Phishing websites often mimic legitimate URLs with subtle variations.
- Browser Warnings: Pay close attention to browser warnings. If your browser flags a website as potentially unsafe, heed the warning and avoid accessing it.
5. Financial Institution Awareness: Knowing Your Bank’s Practices
Your financial institution plays a crucial role in protecting your data. Understanding their security practices and communication methods is essential:
- Communication Channels: Familiarize yourself with your bank’s official communication channels. Be wary of emails, texts, or calls from unfamiliar numbers or addresses claiming to be from your bank.
- Security Features: Understand the security features your bank offers, such as MFA, transaction alerts, and fraud monitoring. Utilize these features to enhance your protection.
- Reporting Procedures: Know how to report suspicious activity or suspected phishing attempts to your bank. Prompt reporting is critical in mitigating potential losses.
6. Education and Training: The Ongoing Battle
Phishing attacks are constantly evolving. Continuous learning and training are crucial to staying ahead of these threats:
- Phishing Simulations: Participate in phishing simulations offered by your employer or other organizations. These exercises help you recognize phishing attempts and improve your awareness.
- Security Awareness Training: Regularly engage in security awareness training to stay updated on the latest phishing techniques and best practices.
- Information Sharing: Share information about suspicious emails or websites with your family, friends, and colleagues. Collective awareness strengthens overall security.
7. The Human Element: Your Most Valuable Defense
Ultimately, the human element is the weakest link in the security chain. Developing a healthy dose of skepticism and caution is paramount:
- Verify Information: Always verify information received through email, text, or phone calls before taking any action. Contact the organization directly through a verified channel to confirm the communication’s authenticity.
- Think Before You Click: Pause and reflect before clicking on links or opening attachments. Consider the source, the context, and the potential risks involved.
- Trust Your Instincts: If something feels wrong or suspicious, it probably is. Don’t hesitate to err on the side of caution.
Frequently Asked Questions (FAQs)
-
Q: What should I do if I think I’ve fallen victim to a phishing attack?
A: Immediately change your passwords for all affected accounts. Contact your bank and other relevant organizations to report the incident. Monitor your accounts for unauthorized activity and consider placing a fraud alert on your credit reports.
-
Q: How can I report a phishing email?
A: Most email providers have mechanisms to report suspicious emails. Look for a "Report Phishing" or similar option in your email client’s settings. You can also report phishing attempts to the Anti-Phishing Working Group (APWG).
-
Q: Are all emails from unknown senders phishing attempts?
A: Not necessarily. However, exercise caution with emails from unknown senders, especially those requesting personal or financial information.
-
Q: Is using public Wi-Fi safe for accessing financial accounts?
A: No, it’s highly discouraged. Public Wi-Fi networks are often unsecured, making your data vulnerable to interception. Use a VPN for added security if you must access financial accounts on public Wi-Fi.
-
Q: How often should I update my passwords?
A: It’s best practice to update your passwords regularly, at least every three months, and more frequently for critical accounts. A password manager can help automate this process.
This comprehensive guide provides a robust framework for safeguarding your financial data from phishing attacks. By diligently implementing these tips and tricks, you can significantly reduce your risk and protect your financial well-being in the ever-evolving digital landscape. Remember, vigilance and proactive security measures are your strongest allies in this ongoing battle against cybercrime. Stay informed, stay vigilant, and stay safe.
Source URL: [Insert a relevant source URL from a reputable cybersecurity website, such as the FTC website or a similar resource.] For example: https://www.ftc.gov/
Closure
Thank you for reading! Stay with us for more insights on How to safeguard financial data from phishing attacks.
Make sure to follow us for more exciting news and reviews.
Feel free to share your experience with How to safeguard financial data from phishing attacks in the comment section.
Stay informed with our next updates on How to safeguard financial data from phishing attacks and other exciting topics.