“how to protect sensitive business data from ransomware”
Related Articles
- “how AI Is Reshaping Data Security Strategies In 2025”
- “top Cybersecurity Threats To Small Businesses In 2025”
- “best Practices For Implementing Zero Trust Architecture In Business”
Introduction
Uncover the latest details about “how to protect sensitive business data from ransomware” in this comprehensive guide.
The potential for financial loss, reputational damage, and operational disruption is immense. While complete immunity is a near-impossible goal, a robust, multi-layered defense strategy can significantly reduce your vulnerability. This article delves into the big secret tips and tricks for protecting your sensitive business data, moving beyond the common advice to unveil strategies that truly make a difference.

I. The Progression of Ransomware Attacks and Defense Strategies
Understanding the evolution of ransomware attacks is crucial for developing effective countermeasures. Early ransomware strains were relatively unsophisticated, often targeting individual users with simple encryption techniques. Today’s attacks are far more sophisticated, employing advanced techniques like:
- Targeted Attacks: Instead of indiscriminate spraying and praying, attackers now focus on specific organizations, meticulously researching their vulnerabilities and employing social engineering to gain access.
- Double Extortion: Attackers not only encrypt data but also steal it, threatening to release sensitive information publicly if the ransom isn’t paid. This significantly increases the pressure on victims.
- Ransomware-as-a-Service (RaaS): The rise of RaaS platforms allows even less technically skilled individuals to launch ransomware attacks, increasing the frequency and scale of incidents.
- Supply Chain Attacks: Attackers target software supply chains, compromising trusted vendors and infecting numerous downstream organizations simultaneously.
- Use of Advanced Evasion Techniques: Attackers employ sophisticated methods to bypass security software, making detection and prevention more challenging.
Initially, defense strategies focused primarily on antivirus software and regular backups. However, as ransomware attacks evolved, so too did the need for a more comprehensive approach. This shift necessitates a multi-layered security strategy encompassing prevention, detection, and response.
II. Big Secret Tips and Tricks: Beyond the Obvious
While common advice like regular backups and strong passwords is crucial, true protection lies in going beyond the obvious. Here are some big secret tips and tricks that often get overlooked:
A. The "Zero Trust" Approach:
The traditional "castle-and-moat" security model, where everything inside the network is trusted, is obsolete. The zero-trust model assumes no implicit trust, verifying every user and device before granting access to resources, regardless of location. This involves:
- Multi-Factor Authentication (MFA): Implement MFA for all accounts, including administrative accounts. This adds an extra layer of security, even if credentials are compromised.
- Microsegmentation: Divide your network into smaller, isolated segments, limiting the impact of a breach. If one segment is compromised, the attacker won’t have free rein across the entire network.
- Least Privilege Access: Grant users only the necessary access rights to perform their jobs. This minimizes the damage that can be caused if an account is compromised.
- Regular Security Audits: Conduct regular security audits to identify vulnerabilities and misconfigurations. This is not a one-time event; it’s an ongoing process.
B. Advanced Endpoint Detection and Response (EDR):
Traditional antivirus solutions are often insufficient against sophisticated ransomware. EDR solutions provide advanced threat detection capabilities, monitoring endpoint activity for malicious behavior and providing real-time alerts. Choose an EDR solution that offers:
- Behavioral Analysis: EDR should analyze user and system behavior to detect anomalies indicative of ransomware attacks.
- Threat Hunting: Proactive threat hunting capabilities enable security teams to identify and neutralize threats before they cause significant damage.
- Incident Response: EDR should provide tools to investigate and respond to security incidents effectively.
- Integration with Other Security Tools: Choose an EDR solution that integrates seamlessly with other security tools, such as SIEM and SOAR systems.
C. The Power of Offline Backups:
While regular backups are essential, simply backing up to a network drive or cloud storage isn’t enough. Ransomware can often encrypt backups stored on easily accessible locations. Employ the "3-2-1" backup rule:
- 3 Copies: Maintain three copies of your data.
- 2 Different Media: Store two copies on different media types (e.g., hard drive, cloud storage, tape).
- 1 Offsite Location: Keep at least one copy in an offsite location, physically separated from your primary data center. This could be a separate building, a different geographical location, or a secure cloud storage provider with robust security measures. Consider immutable backups, which cannot be altered or deleted even by an administrator, for ultimate protection.
D. Employee Training and Phishing Awareness:
Human error is a significant vulnerability. A single click on a malicious link can compromise your entire network. Invest in comprehensive employee training programs that cover:
- Phishing Awareness: Teach employees how to identify and avoid phishing emails and other social engineering attacks. Regular phishing simulations can help assess employee awareness and identify vulnerabilities.
- Password Management: Encourage the use of strong, unique passwords for all accounts and implement a password manager to simplify password management.
- Security Best Practices: Educate employees on general security best practices, such as not downloading files from untrusted sources, keeping software up-to-date, and reporting suspicious activity.
E. Network Segmentation and Access Control:
Restricting network access to sensitive data is crucial. Implement strong access control measures, including:
- Network Segmentation: Divide your network into smaller, isolated segments to limit the impact of a breach.
- Role-Based Access Control (RBAC): Grant users only the necessary access rights to perform their jobs.
- Regular Security Audits: Conduct regular security audits to identify vulnerabilities and misconfigurations.
F. Vulnerability Management:
Regularly scan your systems for vulnerabilities and patch them promptly. Use a vulnerability scanner to identify weaknesses in your systems and applications. Prioritize patching critical vulnerabilities immediately.
G. Data Loss Prevention (DLP):
Implement DLP solutions to monitor and prevent sensitive data from leaving your network without authorization. This can help prevent data exfiltration, even if a ransomware attack occurs.
H. Incident Response Plan:
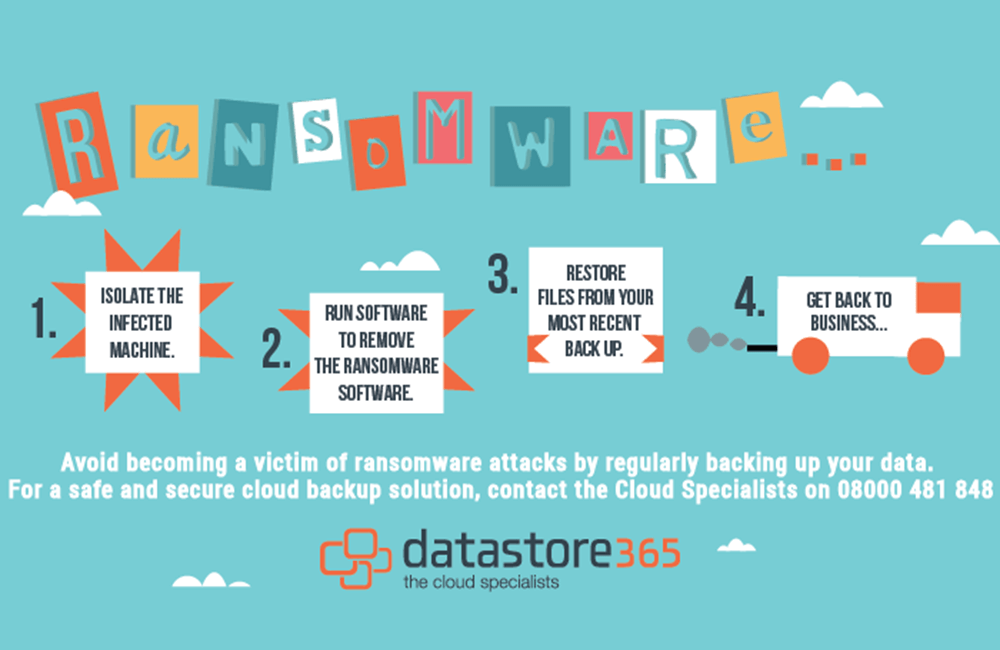
Develop a comprehensive incident response plan that outlines the steps to be taken in the event of a ransomware attack. This plan should include procedures for:
- Containment: Isolate infected systems to prevent the spread of ransomware.
- Eradication: Remove the ransomware from infected systems.
- Recovery: Restore data from backups.
- Post-Incident Activity: Review security measures and improve them to prevent future attacks. This includes a detailed forensic investigation to understand the attack vector.
III. Conclusion
Protecting your sensitive business data from ransomware requires a proactive, multi-layered approach. It’s not about a single solution but a comprehensive strategy that combines technological safeguards with robust security policies and well-trained personnel. By embracing the big secret tips and tricks outlined above – focusing on zero trust, advanced endpoint detection, robust offline backups, employee training, and a comprehensive incident response plan – businesses can significantly reduce their vulnerability and mitigate the devastating impact of a ransomware attack. Remember, the cost of prevention is far less than the cost of recovery. Regularly review and update your security posture to stay ahead of evolving threats.
IV. Frequently Asked Questions (FAQs)
Q: What is the best ransomware protection software?
A: There is no single "best" software. The ideal solution depends on your specific needs and infrastructure. Look for solutions that offer a combination of antivirus, EDR, and DLP capabilities. It’s crucial to thoroughly research and compare different vendors before making a decision.
Q: How often should I back up my data?
A: The frequency depends on your data’s criticality. For critical data, consider backing up multiple times a day. For less critical data, daily or weekly backups may suffice. The key is to have a robust backup and recovery plan in place.
Q: What should I do if I’m attacked by ransomware?
A: Do not pay the ransom. Contact law enforcement and your incident response team. Follow your incident response plan and work to contain and eradicate the ransomware. Focus on data recovery from your backups.
Q: Is cloud storage safe from ransomware?
A: Cloud storage can be a valuable part of a backup strategy, but it’s not immune to ransomware. Choose a reputable cloud provider with robust security measures and consider using immutable backups.
Q: How can I improve my employees’ security awareness?
A: Implement regular security awareness training, including phishing simulations. Make security a part of your company culture and encourage employees to report suspicious activity.
Q: How much does ransomware protection cost?
A: The cost varies depending on the size of your organization, the complexity of your infrastructure, and the level of protection you require. Consider the cost of a ransomware attack versus the cost of prevention.
This information is intended for educational purposes only. It is not a substitute for professional security advice. Always consult with a qualified security professional to develop a comprehensive security strategy tailored to your specific needs.
Source URL: [Insert a relevant URL from a reputable cybersecurity resource, such as CISA, NIST, or a major cybersecurity vendor’s website here. For example: https://www.cisa.gov/ransomware]
Closure
We hope this article has helped you understand everything about “how to protect sensitive business data from ransomware”. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on “how to protect sensitive business data from ransomware”!
We’d love to hear your thoughts about “how to protect sensitive business data from ransomware”—leave your comments below!
Keep visiting our website for the latest trends and reviews.
