How to protect IoT devices in business networks in 2025
Related Articles
- “managing Third-party Risk In Data Security Strategies”
- “how To Secure APIs For Business Applications In 2025”
- “securing Financial Transactions With Post-quantum Cryptography”
- “securing Business Networks Against AI-based Attacks”
- Best VPN Solutions For Protecting Sensitive Business Data
Introduction
Welcome to our in-depth look at How to protect IoT devices in business networks in 2025
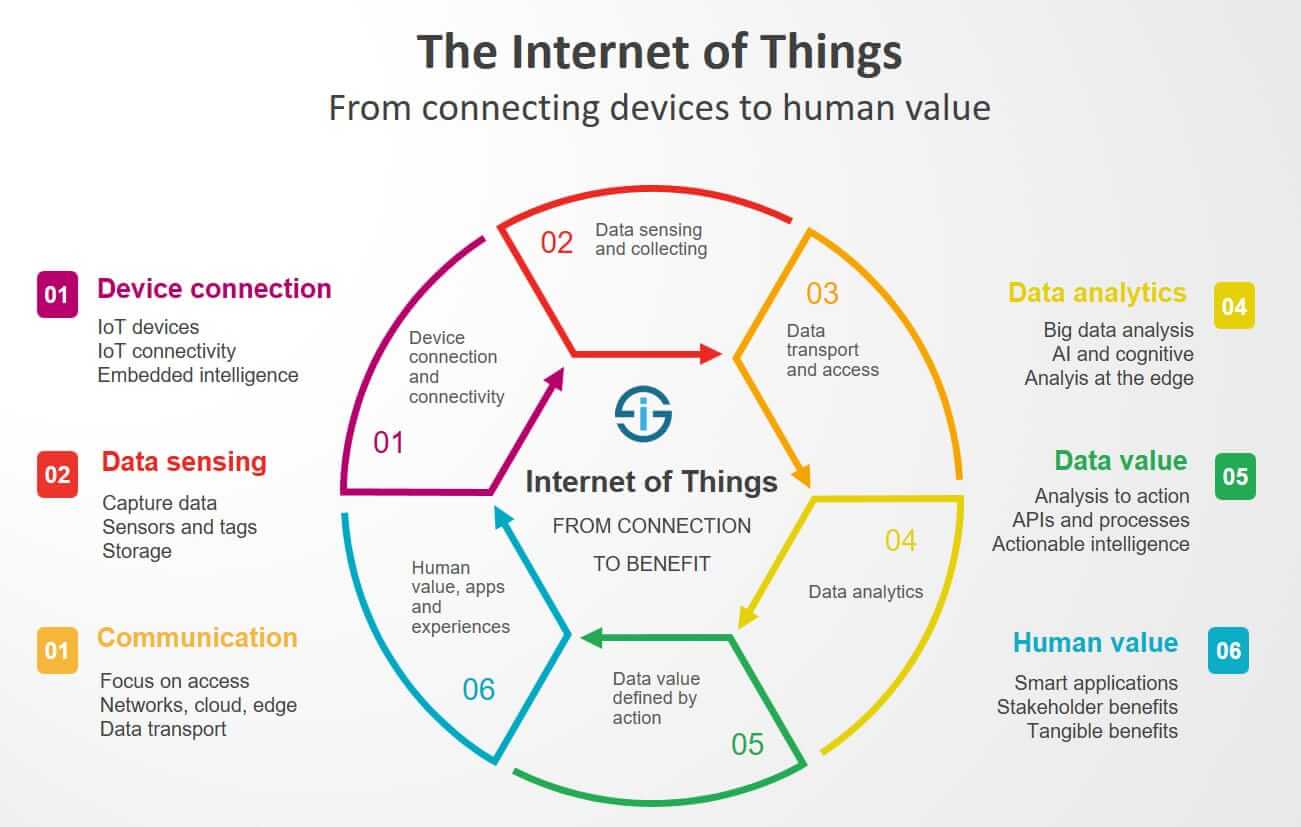
However, this interconnected web of devices also presents a significantly expanded attack surface, making robust security paramount. By 2025, the sophistication of IoT threats will have undoubtedly increased, requiring proactive and multi-layered security strategies that go beyond conventional IT security practices. This article delves into the "big secret" tips and tricks—often overlooked or underemphasized—to effectively protect your business’s IoT devices in 2025.
1. Segmentation: Creating Fortress Islands in Your Network
One of the most crucial—and often neglected—aspects of IoT security is network segmentation. Think of your network not as a single, vast expanse, but as a collection of smaller, isolated networks. Each segment should house devices with similar security profiles and risk levels. This limits the impact of a breach. If a malicious actor compromises a device in one segment, they won’t automatically gain access to the entire network, including sensitive data or critical infrastructure.
The Secret Sauce: Implement strict access control lists (ACLs) at the network level, using firewalls and VLANs (Virtual Local Area Networks) to isolate IoT devices from critical business systems. Consider using micro-segmentation techniques, which further compartmentalize devices within a segment, minimizing the blast radius of a potential attack. Don’t just segment by device type; consider factors like trust level, data sensitivity, and operational criticality. For example, a network segment for low-risk devices like smart lighting can be isolated from a segment containing sensitive industrial control systems.
2. Zero Trust Architecture: Never Trust, Always Verify
The traditional "castle-and-moat" approach to security, where everything inside the network is trusted, is obsolete in the IoT landscape. A zero-trust architecture assumes no implicit trust and verifies every user, device, and application before granting access to resources. This approach is especially critical for IoT, where many devices have limited processing power and may lack robust security features.
The Secret Sauce: Implement strong authentication mechanisms for all IoT devices, even seemingly innocuous ones. This goes beyond simple passwords; consider using certificate-based authentication, multi-factor authentication (MFA), and device-specific digital identities. Continuously monitor device behavior and enforce least privilege access, granting only the necessary permissions to each device. Use micro-segmentation to enforce zero trust even within segments. Consider using a Security Information and Event Management (SIEM) system to aggregate logs from various sources and detect anomalous behavior.
3. Firmware Management: The Unsung Hero of IoT Security
IoT devices often run on embedded firmware that is rarely updated, creating a significant vulnerability. Outdated firmware can contain known security flaws that malicious actors can exploit. A robust firmware management strategy is essential to mitigate this risk.
The Secret Sauce: Develop a comprehensive firmware update policy, including regular checks for updates, automated deployment mechanisms, and rollback capabilities in case of issues. Prioritize updates that address critical vulnerabilities. Use a centralized firmware management system to streamline the process and ensure consistency across all devices. Consider using techniques like image signing and verification to ensure the integrity of firmware updates and prevent tampering. Remember that some IoT devices may have limited update capabilities; plan accordingly and prioritize critical devices.
4. Data Encryption: Protecting Sensitive Information at Rest and in Transit
Data encryption is fundamental to IoT security. Data transmitted between IoT devices and the network, as well as data stored on the devices themselves, must be protected using strong encryption algorithms.
The Secret Sauce: Employ end-to-end encryption for all communication channels between IoT devices and the network. Use strong encryption protocols like TLS 1.3 or its successor. Encrypt data at rest using robust encryption algorithms like AES-256. Implement data loss prevention (DLP) mechanisms to prevent sensitive data from leaving the network unauthorized. Regularly review and update encryption keys and certificates. Consider using hardware security modules (HSMs) to enhance the security of encryption keys.
5. Anomaly Detection and Behavioral Analytics: The Silent Guardians
Traditional signature-based security solutions often fail to detect novel IoT attacks. Behavioral analytics and anomaly detection techniques can provide a powerful supplementary layer of security. These techniques monitor device behavior and identify deviations from established baselines, flagging potential threats in real-time.
The Secret Sauce: Implement machine learning (ML) and artificial intelligence (AI)-powered security solutions that can analyze large volumes of data from various IoT devices and identify anomalies indicative of malicious activity. Establish baselines for normal device behavior and set thresholds for alerts. Use a SIEM system to correlate data from different sources and gain a holistic view of security events. Regularly review and refine the anomaly detection models to adapt to evolving threat landscapes.
6. Vulnerability Management: Proactive Patching and Threat Hunting
Regular vulnerability scanning and penetration testing are critical for identifying and mitigating security weaknesses in IoT devices and the network infrastructure. Proactive threat hunting can uncover hidden vulnerabilities before attackers exploit them.
The Secret Sauce: Employ automated vulnerability scanning tools to regularly assess the security posture of IoT devices and the network. Prioritize patching critical vulnerabilities promptly. Conduct regular penetration testing to simulate real-world attacks and identify weaknesses in security controls. Implement a vulnerability management process that includes vulnerability discovery, risk assessment, remediation, and verification. Engage in proactive threat hunting, using advanced techniques to identify and mitigate potential threats before they can cause damage.
7. Security Awareness Training: The Human Firewall
Even the most robust technical security measures can be undermined by human error. Security awareness training for employees is essential to educate them about IoT security risks and best practices.
The Secret Sauce: Develop a comprehensive security awareness training program that covers topics such as phishing attacks, social engineering, and secure password management. Educate employees about the risks associated with connecting personal devices to the business network and using unsecured Wi-Fi. Conduct regular training sessions and phishing simulations to reinforce security awareness. Establish clear security policies and procedures, and ensure employees understand their responsibilities.
8. Incident Response Planning: Preparing for the Inevitable
Despite the best security measures, security incidents can still occur. A well-defined incident response plan is crucial for minimizing the impact of a breach.
The Secret Sauce: Develop a comprehensive incident response plan that outlines procedures for detecting, containing, eradicating, recovering from, and learning from security incidents. Establish clear roles and responsibilities for incident response team members. Regularly test and update the incident response plan to ensure its effectiveness. Conduct post-incident reviews to identify areas for improvement. Establish communication protocols for informing stakeholders about security incidents.
Frequently Asked Questions (FAQs)
Q: What are the biggest security challenges specific to IoT devices in 2025?
A: The biggest challenges include the sheer volume and diversity of devices, the inherent limitations of many IoT devices (limited processing power, memory, and security features), the difficulty of managing firmware updates across a large number of devices, and the potential for sophisticated attacks exploiting vulnerabilities in both the devices and the network infrastructure. The increasing reliance on cloud services and data analytics also introduces new attack vectors.
Q: How can I secure IoT devices that lack robust security features?
A: Focus on network segmentation, implementing strong access controls, and using encryption to protect data in transit and at rest. Consider using security gateways or proxies to enhance the security of these devices. Prioritize critical devices for updates and consider replacing older, insecure devices with more modern, secure alternatives when feasible.
Q: What role does AI and ML play in IoT security?
A: AI and ML are crucial for anomaly detection, behavioral analytics, and threat hunting. They can analyze vast amounts of data to identify patterns indicative of malicious activity that traditional security solutions might miss. They can also assist in automating security tasks such as vulnerability scanning and incident response.
Q: How can I ensure the security of data collected by IoT devices?
A: Implement end-to-end encryption, data loss prevention (DLP) measures, and access control mechanisms to protect data throughout its lifecycle. Ensure compliance with relevant data privacy regulations (e.g., GDPR, CCPA). Regularly audit data security practices to identify and address vulnerabilities.
Q: What is the importance of regular security audits and penetration testing?
A: Regular security audits and penetration testing are crucial for identifying vulnerabilities and weaknesses in your IoT security posture before malicious actors can exploit them. These assessments provide valuable insights into the effectiveness of your security controls and allow for proactive remediation of identified risks.
This comprehensive overview provides a solid foundation for securing your business’s IoT infrastructure in 2025. Remember that a layered approach, combining technical controls with robust security policies and employee training, is essential for effective protection. The landscape is dynamic; continuous monitoring, adaptation, and staying informed about emerging threats are vital for maintaining a strong security posture.
Source URL: [Insert a relevant URL here, e.g., a NIST publication on IoT security, or a reputable cybersecurity firm’s website discussing IoT security best practices.] For example: [https://www.nist.gov/](Replace with a relevant and active URL)
Closure
Thank you for reading! Stay with us for more insights on How to protect IoT devices in business networks in 2025.
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about How to protect IoT devices in business networks in 2025—leave your comments below!
Stay informed with our next updates on How to protect IoT devices in business networks in 2025 and other exciting topics.
