“how to protect intellectual property from cyberattacks”
Related Articles
- “how To Integrate AI With Business Cybersecurity Software”
- “how To Choose The Best Cybersecurity Consultant For Your Business”
- “2025 Best Practices For Securing Business Data”
- “impact Of AI On Insider Threat Detection”
- “top US Regulations Affecting Data Security In 2025”
Introduction
Uncover the latest details about “how to protect intellectual property from cyberattacks” in this comprehensive guide.
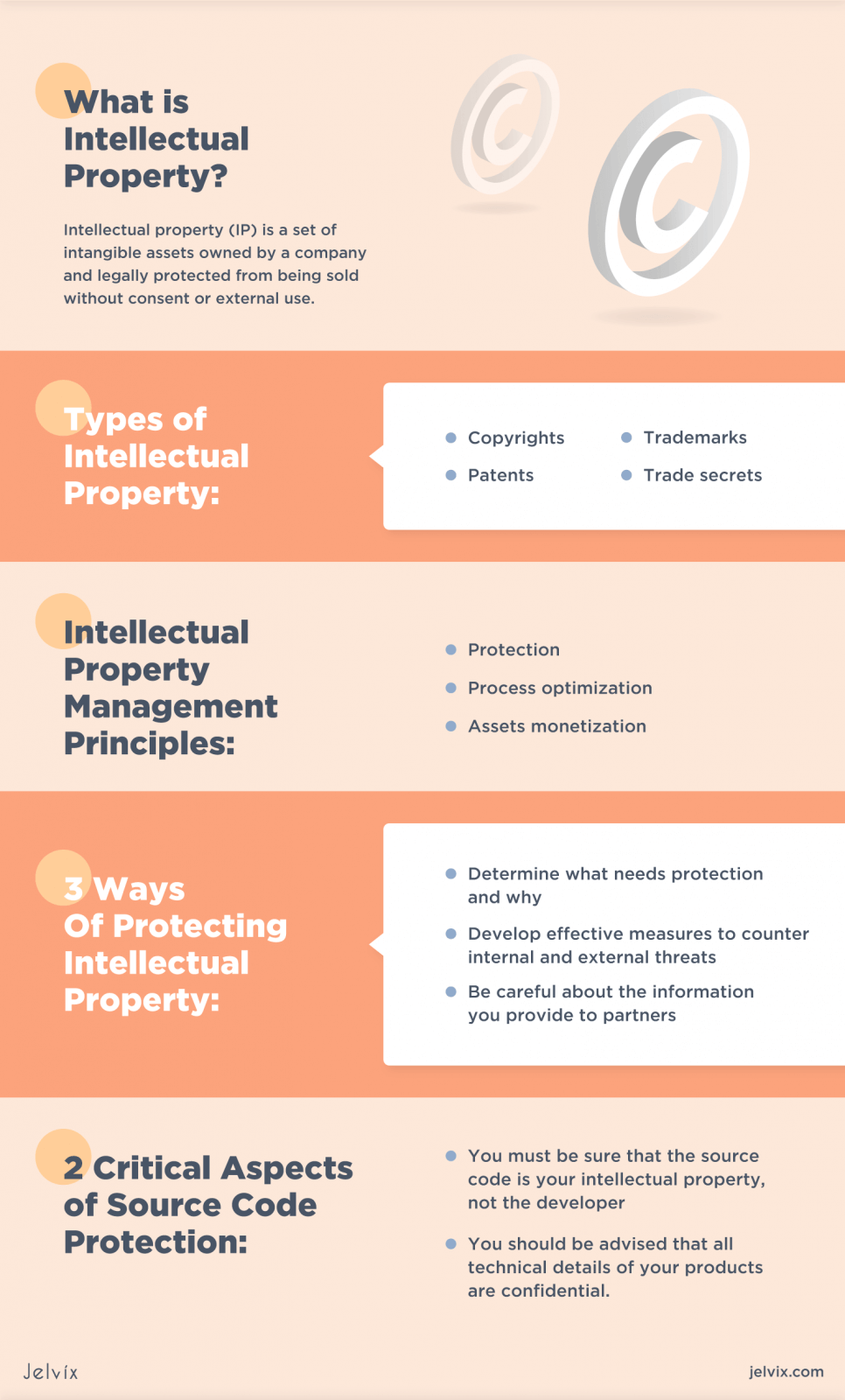
This intangible asset – encompassing inventions, designs, trademarks, copyrights, and trade secrets – represents the culmination of years of research, development, and innovation. However, the digital landscape presents a constant threat, with cyberattacks posing a significant risk to the confidentiality, integrity, and availability of this crucial IP. While many organizations implement basic security measures, true protection requires a multi-layered, proactive approach that goes beyond the surface level. This article delves into the often-overlooked strategies and "big secret" tips to fortify your IP against the ever-evolving threat of cyberattacks.

1. Beyond the Firewall: A Multi-Layered Defense Strategy
The traditional approach to cybersecurity often focuses on perimeter security, relying heavily on firewalls and intrusion detection systems. While these are essential components, they are insufficient on their own. A robust IP protection strategy necessitates a multi-layered defense, extending beyond the network perimeter to encompass every facet of your organization’s digital infrastructure. This includes:
-
Endpoint Security: Securing individual devices (computers, laptops, mobile phones) is paramount. This involves deploying robust endpoint detection and response (EDR) solutions, regularly updating software and operating systems, employing strong password policies (including multi-factor authentication), and implementing data loss prevention (DLP) tools. Regular security audits of individual devices are critical.
-
Network Security: Beyond firewalls, consider implementing advanced threat protection, such as intrusion prevention systems (IPS), next-generation firewalls (NGFWs), and secure web gateways (SWG). Regular penetration testing and vulnerability assessments are crucial to identify and address weaknesses in your network infrastructure. Segmenting your network into isolated zones can limit the impact of a breach.
Data Encryption: Encrypting sensitive data both in transit and at rest is non-negotiable. This involves employing strong encryption algorithms and key management systems. Consider using full-disk encryption for laptops and other mobile devices. Encryption protects data even if a breach occurs.
-
Access Control and Privileged Access Management (PAM): Implementing a robust access control system, based on the principle of least privilege, restricts access to sensitive IP to only authorized personnel. PAM solutions provide additional security for privileged accounts, which often have broad access to critical systems and data.
2. The Human Element: Training and Awareness
Cybersecurity is not solely a technological problem; it’s a human problem. Phishing attacks, social engineering, and insider threats remain significant vulnerabilities. Investing in comprehensive employee training programs is vital. This includes:
-
Security Awareness Training: Regular training sessions should educate employees about common cyber threats, such as phishing emails, malware, and social engineering tactics. Simulations and phishing exercises can effectively test employee awareness and reinforce training.
-
Data Handling Policies: Clear and concise data handling policies should be implemented and regularly communicated to employees. These policies should outline acceptable use of company devices, data storage procedures, and protocols for handling sensitive information.
-
Incident Response Training: Employees should know how to respond to suspected security incidents, including reporting procedures and escalation paths. Regular drills and simulations can prepare employees for real-world scenarios.
-
Background Checks and Vetting: Thorough background checks for employees who will have access to sensitive IP are essential to mitigate the risk of insider threats.
3. The Cloud Conundrum: Securing Your Intellectual Property in the Cloud
Many organizations store their IP in the cloud, leveraging the scalability and cost-effectiveness of cloud services. However, this also introduces new security challenges. To mitigate these risks:
-
Choose Reputable Cloud Providers: Select cloud providers with a strong security track record and robust compliance certifications (e.g., ISO 27001, SOC 2).
-
Implement Strong Access Controls: Utilize cloud-based access control mechanisms to restrict access to sensitive data based on the principle of least privilege.
-
Data Encryption at Rest and in Transit: Ensure that your data is encrypted both when stored in the cloud and when being transmitted.
-
Regular Security Audits: Conduct regular security audits of your cloud infrastructure to identify and address vulnerabilities.
-
Cloud Security Posture Management (CSPM): Employ CSPM tools to monitor your cloud environment for security misconfigurations and vulnerabilities.
4. The Power of Data Loss Prevention (DLP): Protecting Your IP from Exfiltration
Data loss prevention (DLP) solutions are critical for preventing sensitive IP from leaving your organization’s control. These tools monitor data movement and identify attempts to exfiltrate sensitive information. Effective DLP strategies include:
-
Implementing DLP Tools: Deploy DLP tools that monitor network traffic, email, and endpoints for sensitive data.
-
Defining Sensitive Data: Clearly define what constitutes sensitive IP within your organization. This should include specific file types, keywords, and data patterns.
-
Configuring DLP Rules: Configure DLP rules to monitor for unauthorized access, copying, or transfer of sensitive data.
-
Regular Monitoring and Reporting: Regularly monitor DLP alerts and reports to identify potential security incidents.
5. Regular Security Audits and Penetration Testing: Proactive Vulnerability Management
Proactive vulnerability management is crucial. Regular security audits and penetration testing can identify weaknesses in your security posture before attackers can exploit them.
-
Regular Security Audits: Conduct regular security audits of your IT infrastructure, applications, and processes.
-
Penetration Testing: Employ penetration testing to simulate real-world attacks and identify vulnerabilities in your systems.
-
Vulnerability Scanning: Regularly scan your systems for known vulnerabilities using automated vulnerability scanners.
-
Address Identified Vulnerabilities: Promptly address any identified vulnerabilities, prioritizing those with the highest risk.
6. Legal and Contractual Safeguards: Protecting Your IP through Legal Means
Legal and contractual measures are essential complements to technological safeguards.
-
Strong Intellectual Property Rights: Ensure that your IP is properly protected through patents, trademarks, copyrights, and trade secrets.
-
Non-Disclosure Agreements (NDAs): Use NDAs to protect confidential information shared with employees, contractors, and partners.
-
Data Processing Agreements (DPAs): If processing personal data, ensure compliance with relevant data protection regulations (e.g., GDPR) through DPAs.
-
Legal Counsel: Consult with legal counsel to ensure your IP protection strategies are legally sound and compliant with relevant regulations.
7. Incident Response Planning: Minimizing the Impact of a Breach
Even with robust security measures, a breach is always a possibility. A well-defined incident response plan is crucial for minimizing the damage.
-
Incident Response Team: Establish an incident response team with clearly defined roles and responsibilities.
-
Incident Response Plan: Develop a comprehensive incident response plan that outlines procedures for identifying, containing, eradicating, recovering from, and learning from security incidents.
-
Regular Drills and Simulations: Conduct regular drills and simulations to test the effectiveness of your incident response plan.
-
Post-Incident Review: After an incident, conduct a thorough post-incident review to identify lessons learned and improve your security posture.
8. Continuous Monitoring and Improvement: The Evolving Landscape of Cyber Threats
The cybersecurity landscape is constantly evolving, with new threats emerging regularly. Continuous monitoring and improvement are essential.
-
Security Information and Event Management (SIEM): Implement SIEM tools to collect and analyze security logs from various sources, providing real-time visibility into your security posture.
-
Threat Intelligence: Stay informed about emerging threats through threat intelligence feeds and security advisories.
-
Regular Security Assessments: Conduct regular security assessments to evaluate the effectiveness of your security controls and identify areas for improvement.
-
Adaptive Security: Adopt an adaptive security approach, constantly adjusting your security posture to address emerging threats and vulnerabilities.
Frequently Asked Questions (FAQs)
Q: What is the most important step in protecting intellectual property from cyberattacks?
A: While all the steps outlined above are crucial, the most important is a holistic approach that combines strong technical security measures with comprehensive employee training and awareness, robust legal safeguards, and a proactive approach to vulnerability management. No single element is sufficient on its own.
Q: How often should I conduct security audits and penetration testing?
A: The frequency of security audits and penetration testing depends on your organization’s risk profile and industry regulations. However, a general guideline is to conduct penetration testing at least annually, and security audits at least semi-annually. More frequent testing may be necessary for organizations handling highly sensitive IP.
Q: What should I do if I suspect a data breach?
A: Immediately activate your incident response plan. Isolate affected systems, contain the breach, and notify relevant authorities and affected parties as required by law. Conduct a thorough investigation to determine the extent of the breach and implement corrective measures.
Q: How can I protect my trade secrets from cyberattacks?
A: Protecting trade secrets requires a multi-faceted approach, including strong access controls, data encryption, regular employee training, and robust NDAs with employees, contractors, and partners. Consider implementing specialized tools for trade secret management.
Q: What is the role of insurance in protecting my intellectual property?
A: Cyber insurance can help mitigate the financial impact of a data breach, covering costs associated with incident response, legal fees, and regulatory fines. However, insurance should be considered a supplementary measure, not a replacement for robust security practices.
This comprehensive guide provides a strong foundation for protecting your intellectual property from cyberattacks. Remember, security is an ongoing process, requiring constant vigilance and adaptation. By implementing these strategies and staying informed about emerging threats, you can significantly reduce your risk and safeguard your valuable IP.
Source URL: [Insert a relevant URL from a reputable cybersecurity source here, e.g., a NIST publication or a reputable cybersecurity firm’s website]
Closure
Thank you for reading! Stay with us for more insights on “how to protect intellectual property from cyberattacks”.
Don’t forget to check back for the latest news and updates on “how to protect intellectual property from cyberattacks”!
Feel free to share your experience with “how to protect intellectual property from cyberattacks” in the comment section.
Stay informed with our next updates on “how to protect intellectual property from cyberattacks” and other exciting topics.
