“how to monitor employee devices for potential data breaches”
Related Articles
- “how To Train Employees To Recognize Phishing Attacks”
- “best Practices For Implementing Zero Trust Architecture In Business”
- “cloud Security Trends For Business Owners 2025”
- Businesses Can Face Numerous Other Legal Challenges, Including:
- “AI-driven Threat Detection Tools For Businesses”
Introduction
In this article, we dive into “how to monitor employee devices for potential data breaches”, giving you a full overview of what’s to come
However, relying solely on EDR is insufficient. Sophisticated attackers can bypass signature-based detection, requiring a more proactive approach. This involves "threat hunting," a proactive search for malicious activity, even in the absence of alerts.
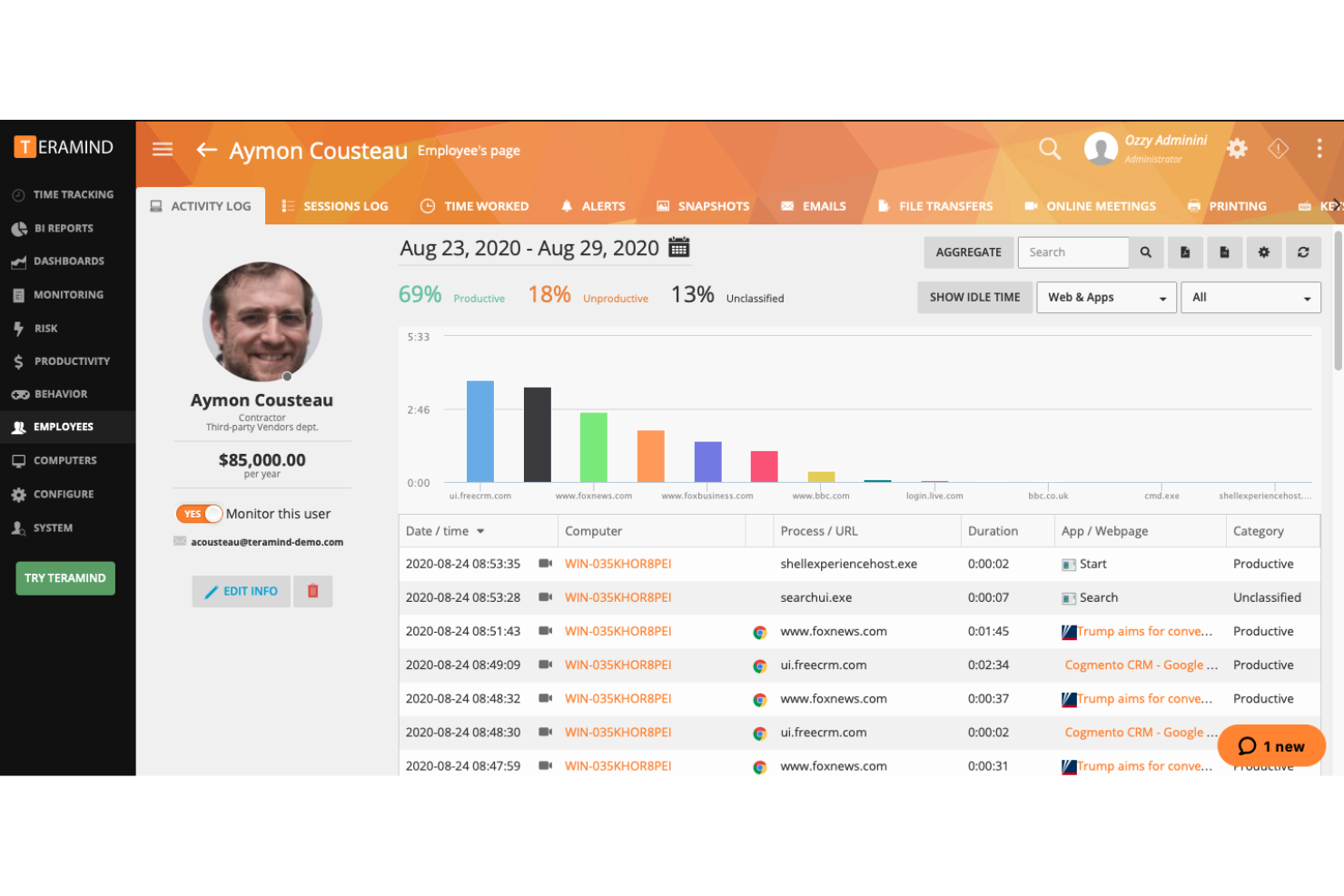
Big Secret Tip #1: Employ behavioral analytics. Instead of solely relying on known malware signatures, analyze user and device behavior for anomalies. This includes unusual login attempts, unexpected data transfers, access to sensitive files outside regular working hours, or unusually high CPU or network usage. Advanced EDR solutions offer this capability, but manual analysis of logs and security information and event management (SIEM) data can also reveal hidden threats.
Big Secret Tip #2: Focus on insider threats. Not all breaches are external. Disgruntled employees or those with malicious intent can pose a significant risk. Monitor access patterns, data modification history, and unusual file downloads or uploads. Implement data loss prevention (DLP) tools to detect and block sensitive data leaving the network, regardless of the method.
2. Leveraging Mobile Device Management (MDM) and Mobile Application Management (MAM)
The proliferation of mobile devices in the workplace necessitates robust mobile device management. MDM solutions allow for remote wiping of devices, application control, and security policy enforcement. However, many organizations fail to fully leverage their capabilities.
Big Secret Tip #3: Implement granular control over applications. Don’t just restrict app installations; actively monitor app usage. Identify apps accessing sensitive data and enforce strong authentication for such apps. MAM solutions allow for separating work and personal data on employee devices, minimizing the risk of data leakage.
Big Secret Tip #4: Geo-fencing and device location tracking. For employees who frequently work remotely or travel, consider using geo-fencing to trigger alerts if devices access sensitive data outside designated locations. Device location tracking can be invaluable in case of theft or loss. Remember to clearly communicate this policy to employees and obtain their consent where legally required.
3. Data Encryption and Access Control: The Foundation of Security
Encryption and access control are fundamental security practices. However, their effectiveness depends on proper implementation and ongoing monitoring.
Big Secret Tip #5: Implement full-disk encryption on all employee devices. This ensures that even if a device is stolen or lost, the data remains inaccessible to unauthorized individuals. Use strong encryption algorithms and enforce strong password policies.
Big Secret Tip #6: Implement least privilege access control. Employees should only have access to the data and applications necessary for their roles. Regularly review and update access rights to ensure they remain appropriate. Utilize role-based access control (RBAC) to streamline this process.
4. Network Monitoring and Anomaly Detection: Beyond the Firewall
While firewalls are crucial, they are not a silver bullet. Network monitoring tools can detect suspicious network traffic patterns indicative of data breaches.
Big Secret Tip #7: Analyze network traffic for unusual outbound connections. Look for connections to known malicious IP addresses or domains, unusually large data transfers, or connections to unexpected locations. Network traffic analysis can reveal covert data exfiltration attempts that bypass traditional security measures.
Big Secret Tip #8: Implement intrusion detection and prevention systems (IDPS). These systems analyze network traffic for malicious patterns and can block or alert on suspicious activity. Ensure that your IDPS is up-to-date with the latest threat signatures and regularly review its logs for anomalies.
5. Security Awareness Training and Phishing Simulations: The Human Element
Even the most sophisticated security measures can be rendered ineffective by human error. Regular security awareness training is crucial.
Big Secret Tip #9: Conduct regular phishing simulations. These simulations help identify employees vulnerable to phishing attacks and provide an opportunity to reinforce security awareness training. Analyze the results to identify areas for improvement in your training program.
Big Secret Tip #10: Encourage employees to report suspicious emails or websites. Create a safe and non-punitive environment for reporting security incidents. This allows for early detection and response to potential threats.
6. Regular Security Audits and Vulnerability Scanning: Proactive Defense
Regular security assessments are essential to identify vulnerabilities before they can be exploited.
Big Secret Tip #11: Conduct regular vulnerability scans on all employee devices. These scans identify software vulnerabilities that could be exploited by attackers. Prioritize patching critical vulnerabilities promptly.
Big Secret Tip #12: Perform periodic security audits. These audits assess the overall security posture of your organization, including employee device security. They identify weaknesses in your security controls and provide recommendations for improvement.
7. Data Loss Prevention (DLP) Tools: Preventing Data Exfiltration
DLP tools provide advanced capabilities for monitoring and preventing sensitive data from leaving the organization’s control.
Big Secret Tip #13: Implement DLP solutions that monitor both network traffic and endpoint devices. These tools can detect and block sensitive data from being copied, emailed, or transferred to unauthorized locations. Configure DLP rules based on specific data types and sensitivity levels.
Big Secret Tip #14: Use DLP tools to monitor for data exfiltration attempts using various methods, such as cloud storage services, USB drives, or email. These tools can provide alerts and logs to help investigate potential breaches.
8. The Ethical Considerations: Balancing Security and Privacy
While monitoring employee devices is crucial for security, it’s essential to respect employee privacy. Transparency and consent are paramount.
Big Secret Tip #15: Develop a clear and comprehensive employee device usage policy. This policy should outline the organization’s monitoring practices, the types of data that will be monitored, and the reasons for monitoring. Obtain employee consent for monitoring activities where legally required.
Big Secret Tip #16: Limit monitoring to work-related activities. Avoid monitoring personal communications or data unless there is a legitimate business need and appropriate legal authorization. Regularly review and update your monitoring policies to reflect changes in technology and legal requirements.
Frequently Asked Questions (FAQs)
Q1: What is the legal basis for monitoring employee devices?
A1: The legal basis for monitoring employee devices varies by jurisdiction. In many countries, employers can monitor employee devices if they have a legitimate business reason and have informed employees of the monitoring practices. However, there are strict limitations on the extent of monitoring and the types of data that can be collected. It is crucial to consult with legal counsel to ensure compliance with applicable laws and regulations.
Q2: How can I balance employee privacy with the need for security?
A2: Balancing employee privacy and security requires a careful approach. Transparency is key. Clearly communicate your monitoring policies to employees, outlining what will be monitored and why. Limit monitoring to work-related activities and obtain consent where legally required. Implement strong data protection measures to ensure the confidentiality and integrity of collected data. Regularly review and update your policies to reflect changes in technology and legal requirements.
Q3: What are the costs associated with implementing these monitoring solutions?
A3: The costs vary depending on the size of your organization, the complexity of your infrastructure, and the specific solutions you choose. You may need to invest in new software and hardware, as well as training for your IT staff. Consider the total cost of ownership, including implementation, maintenance, and ongoing support.
Q4: What happens if a data breach is detected?
A4: If a data breach is detected, you must have a well-defined incident response plan. This plan should outline the steps to be taken to contain the breach, investigate its cause, and mitigate its impact. You may need to notify affected individuals and regulatory authorities, depending on the nature and severity of the breach. Consult with legal counsel to ensure compliance with applicable laws and regulations.
Q5: How often should I update my security measures?
A5: Regular updates are crucial. Cyber threats are constantly evolving, so your security measures must keep pace. Regularly update your software, conduct vulnerability scans, and review your security policies. Consider subscribing to threat intelligence feeds to stay informed about the latest threats.
This article provides a comprehensive overview of advanced techniques for monitoring employee devices to prevent data breaches. Remember that a multi-layered approach combining technological solutions, security awareness training, and robust policies is the most effective strategy. Staying proactive and adapting to the ever-evolving threat landscape is critical to protecting your organization’s valuable data.
Source URL: [Insert a relevant URL from a reputable cybersecurity source, such as SANS Institute, NIST, or similar.] (e.g., https://www.sans.org/reading-room/)
Closure
We hope this article has helped you understand everything about “how to monitor employee devices for potential data breaches”. Stay tuned for more updates!
Make sure to follow us for more exciting news and reviews.
Feel free to share your experience with “how to monitor employee devices for potential data breaches” in the comment section.
Stay informed with our next updates on “how to monitor employee devices for potential data breaches” and other exciting topics.
