“how to implement post-quantum encryption technologies”
Related Articles
- “importance Of Supply Chain Security In Preventing Data Breaches”
- “impact Of Quantum Computing On Business Data Encryption”
- “how To Secure IoT Devices In Corporate Networks”
- “top Cybersecurity Threats To Small Businesses In 2025”
- “best Tools For Monitoring Business Data Access”
Introduction
Uncover the latest details about “how to implement post-quantum encryption technologies” in this comprehensive guide.
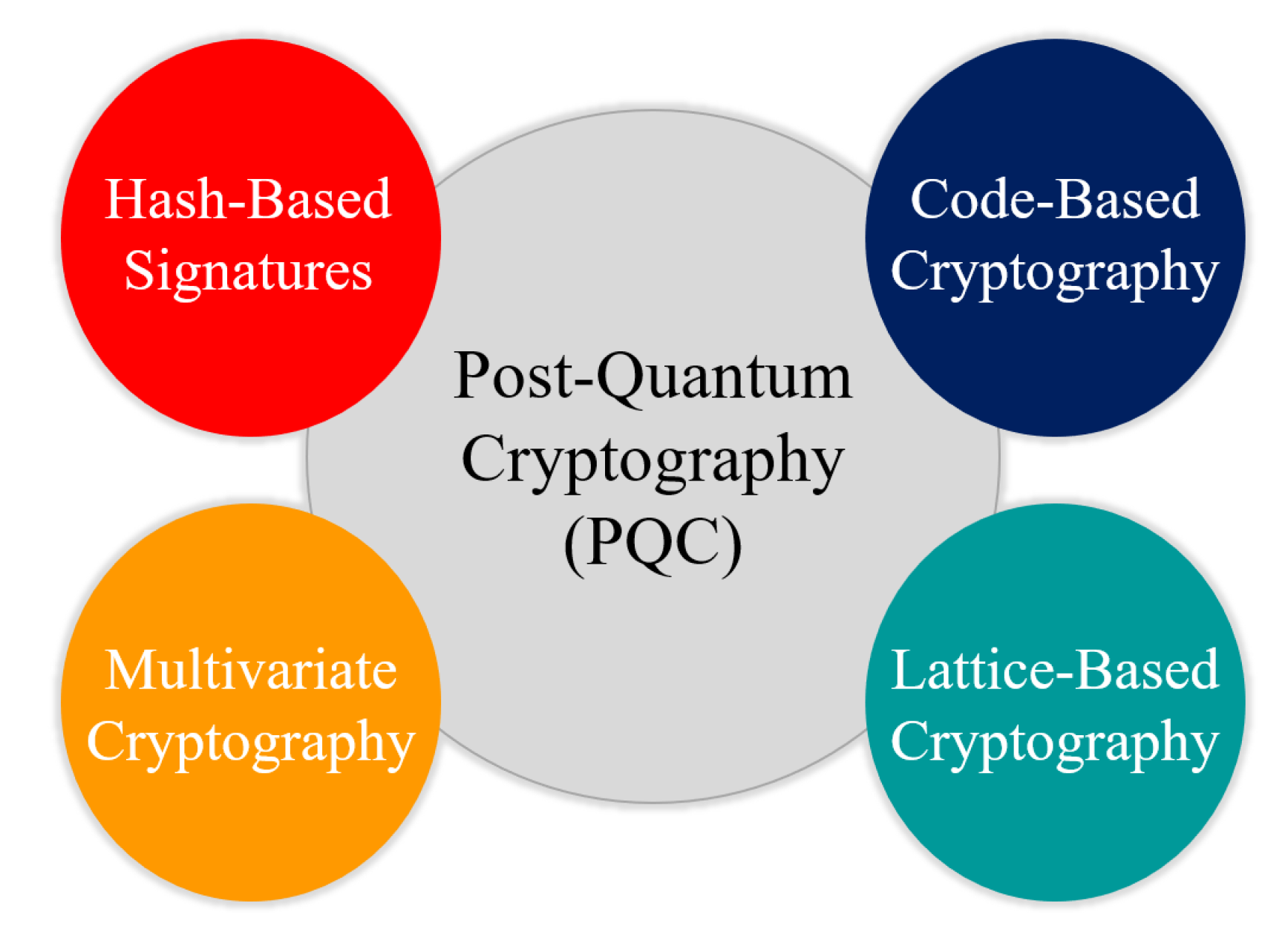
Algorithms that are currently considered computationally secure are vulnerable to being broken by sufficiently powerful quantum computers. This looming threat necessitates a proactive approach to securing our digital infrastructure, demanding a transition to post-quantum cryptography (PQC). While the transition is complex, understanding the intricacies of implementing PQC is crucial for safeguarding our data in the quantum era. This article offers a comprehensive exploration of the process, revealing some "big secret" tips and tricks that can streamline and secure your implementation.

1. Assessing Your Current Cryptographic Landscape: The Foundation of PQC Implementation
Before diving into the specifics of PQC, a thorough assessment of your existing cryptographic infrastructure is paramount. This involves identifying all systems, applications, and protocols that rely on currently used encryption algorithms like RSA, ECC, and DSA. This inventory should include:
- Hardware and Software Inventory: List all devices, servers, and applications using encryption. Note their operating systems, programming languages, and libraries.
- Algorithm Dependency Mapping: Trace the usage of specific algorithms within each system. This is crucial for identifying which algorithms need replacing and the scope of the upgrade.
- Key Management Systems (KMS): Understand your existing KMS and its capabilities. PQC often requires different key sizes and management strategies.
- Security Policies and Procedures: Review existing security policies to determine how PQC implementation will impact compliance and operational procedures.
This meticulous inventory allows for a realistic project plan, minimizing disruption and maximizing efficiency. The "secret" here lies in the detail. A superficial assessment can lead to overlooked vulnerabilities and costly rework later on.
2. Choosing the Right Post-Quantum Algorithm: A Balancing Act
The National Institute of Standards and Technology (NIST) has standardized several post-quantum cryptographic algorithms. The selection of the appropriate algorithm depends heavily on your specific needs and constraints. Factors to consider include:
- Security Level: Different algorithms offer different levels of security against both classical and quantum attacks. Choose an algorithm that meets your organization’s risk tolerance.
- Performance: PQC algorithms vary significantly in their performance characteristics. Consider the computational overhead and its impact on your applications. Some algorithms are better suited for resource-constrained environments than others.
- Key Size and Management: PQC algorithms often require larger keys than their classical counterparts. Assess the impact on key management, storage, and distribution.
- Algorithm Maturity and Standardization: Opt for algorithms that have undergone rigorous scrutiny and are standardized by NIST or other reputable organizations. This minimizes the risk of unforeseen vulnerabilities.
The "secret" here lies in understanding the trade-offs. There’s no single "best" algorithm; the optimal choice depends on your specific context. Thorough benchmarking and testing are essential.
3. Gradual Migration: A Phased Approach to Minimizing Disruption
Implementing PQC shouldn’t be a sudden, disruptive overhaul. A phased approach minimizes risk and allows for continuous monitoring and adaptation.
- Pilot Projects: Start with pilot projects in non-critical systems to gain practical experience and identify potential challenges.
- Incremental Rollouts: Gradually migrate systems to PQC, prioritizing those handling sensitive data or facing the highest risk.
- Hybrid Approaches: Initially, consider hybrid approaches where both classical and post-quantum algorithms are used in parallel. This provides a fallback mechanism while ensuring compatibility.
- Monitoring and Feedback Loops: Continuously monitor the performance and security of implemented PQC solutions. Establish feedback loops to address any issues promptly.
The "secret" lies in iterative development. A phased approach allows for course correction, minimizing the impact of unexpected issues.
4. Secure Key Management: The Heart of PQC Security
Secure key management is paramount in PQC, even more so than in classical cryptography due to the larger key sizes. Consider these aspects:
- Hardware Security Modules (HSMs): HSMs provide a secure environment for key generation, storage, and management. They are crucial for protecting against both physical and digital attacks.
- Key Lifecycle Management: Establish clear procedures for key generation, distribution, rotation, and revocation. Automate these processes where possible to minimize human error.
- Key Backup and Recovery: Implement robust mechanisms for backing up and recovering keys in case of loss or damage.
- Access Control: Strictly control access to keys and key management systems. Employ strong authentication and authorization mechanisms.
The "secret" is in the detail of your key management processes. Weak key management can negate the security benefits of PQC.
5. Integration with Existing Systems: Bridging the Gap
Integrating PQC into existing systems often requires modifications to software and hardware. Consider these strategies:
- Library Updates: Update cryptographic libraries to support PQC algorithms. Ensure compatibility with your existing systems and applications.
- API Changes: Adapt APIs to accommodate the changes in key sizes and algorithm parameters.
- Protocol Modifications: Modify protocols to support the new algorithms. This might involve changes to network communication and data formats.
- Testing and Validation: Thoroughly test the integration to ensure functionality, performance, and security.
The "secret" is in careful planning and thorough testing. Integration issues can lead to significant delays and security vulnerabilities.
6. Addressing Interoperability Challenges: The Ecosystem Approach
PQC implementation requires a collaborative ecosystem approach. Different organizations may adopt different algorithms, leading to interoperability challenges. Strategies to address this include:
- Standardization: Adherence to NIST standardized algorithms ensures broader compatibility.
- Hybrid Approaches: Using hybrid cryptosystems that combine classical and post-quantum algorithms can bridge the gap during the transition period.
- Open-Source Libraries: Utilizing open-source libraries can improve interoperability and facilitate community-driven development and testing.
- Collaboration and Information Sharing: Open communication and collaboration among organizations are essential for overcoming interoperability challenges.
The "secret" is in proactive collaboration and commitment to standardization. A fragmented approach will hinder the successful transition to a post-quantum world.
7. Continuous Monitoring and Adaptation: The Ongoing Journey
Implementing PQC is not a one-time event but an ongoing process. Continuous monitoring and adaptation are crucial for maintaining security in the face of evolving threats.
- Vulnerability Monitoring: Stay informed about newly discovered vulnerabilities in PQC algorithms and promptly address any issues.
- Performance Monitoring: Continuously monitor the performance of PQC algorithms and optimize them as needed.
- Algorithm Updates: Be prepared to update to newer, more secure algorithms as they become available.
- Security Audits: Regularly conduct security audits to identify and address any weaknesses in your PQC implementation.
The "secret" is in maintaining vigilance. The threat landscape is constantly evolving, and your security posture must adapt accordingly.
8. The Human Factor: Training and Awareness
The success of PQC implementation relies heavily on the human element. Training and awareness programs are crucial for ensuring that personnel understand the importance of PQC and can effectively manage it.
- Training Programs: Provide training to IT staff on the principles of PQC, the chosen algorithms, and the associated security practices.
- Security Awareness Campaigns: Educate employees about the importance of strong passwords, secure practices, and the potential risks of quantum computing.
- Incident Response Plans: Develop and test incident response plans to handle potential security breaches related to PQC implementation.
The "secret" is in empowering your workforce. Informed and trained personnel are the first line of defense.
Frequently Asked Questions (FAQs)
Q: When will quantum computers pose a real threat to current encryption?
A: The timeline is uncertain. While powerful quantum computers are still under development, experts predict that they could pose a significant threat within the next 10-20 years, or even sooner for specific applications. Proactive migration to PQC is crucial to avoid being caught unprepared.
Q: Are all post-quantum algorithms equally secure?
A: No. Different algorithms offer different levels of security and performance. NIST’s standardization process aims to identify algorithms that provide a high level of security, but ongoing research and cryptanalysis could reveal vulnerabilities in the future.
Q: How expensive is implementing post-quantum cryptography?
A: The cost varies depending on the scale and complexity of your infrastructure. It involves software and hardware upgrades, training, and ongoing maintenance. However, the cost of inaction – a large-scale data breach – is likely far greater.
Q: Can I implement PQC myself?
A: Implementing PQC effectively requires specialized expertise in cryptography, security engineering, and systems administration. While some aspects can be handled internally, engaging with experienced security consultants is often recommended, especially for large-scale deployments.
Q: Will PQC completely replace current encryption methods?
A: Initially, a hybrid approach combining classical and post-quantum algorithms is likely. Over time, as PQC matures and becomes more widely adopted, a complete transition is expected.
Q: What is the role of standardization in PQC?
A: Standardization is crucial for ensuring interoperability and widespread adoption of PQC. NIST’s standardized algorithms provide a baseline for secure and compatible implementations across different systems and organizations.
This deep dive into implementing post-quantum encryption technologies provides a roadmap for navigating this crucial transition. Remember, proactive planning, meticulous implementation, and continuous monitoring are key to securing your digital assets in the quantum era. The "big secret" isn’t a single trick but a holistic approach encompassing all the aspects discussed above.
Source URL: https://csrc.nist.gov/projects/post-quantum-cryptography
Closure
We hope this article has helped you understand everything about “how to implement post-quantum encryption technologies”. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on “how to implement post-quantum encryption technologies”!
We’d love to hear your thoughts about “how to implement post-quantum encryption technologies”—leave your comments below!
Stay informed with our next updates on “how to implement post-quantum encryption technologies” and other exciting topics.
