“how to implement post-quantum encryption in your business”
Related Articles
- “how Blockchain Can Enhance Data Security In Business”
- “best Tools For Monitoring Business Data Access”
- “securing Business Networks Against AI-based Attacks”
- “securing Financial Transactions With Post-quantum Cryptography”
- “ransomware Recovery Strategies For Enterprises In 2025”
Introduction
Join us as we explore “how to implement post-quantum encryption in your business”, packed with exciting updates
This involves identifying your organization’s most valuable assets – intellectual property, customer data, financial records, etc. – and determining the potential impact of a data breach. Consider the following:

- Data Sensitivity: Categorize your data based on sensitivity levels (e.g., public, confidential, highly confidential). Highly sensitive data requires the most robust protection.
- Data Lifecycle: Analyze the entire lifecycle of your data, from creation and storage to transmission and disposal. Weaknesses at any stage can compromise security.
- Attack Vectors: Identify potential attack points, such as web servers, email systems, databases, and mobile devices. Understand how attackers might exploit vulnerabilities in your current encryption infrastructure.
- Regulatory Compliance: Determine which regulations and standards apply to your industry (e.g., HIPAA, GDPR, PCI DSS). Non-compliance can lead to hefty fines and reputational damage.
This assessment should inform your PQC implementation strategy, prioritizing the protection of your most critical assets and addressing the most likely attack vectors. A well-defined risk assessment will guide your resource allocation and ensure a focused approach.
2. Choosing the Right Post-Quantum Algorithm: Navigating the Landscape
The National Institute of Standards and Technology (NIST) has standardized several post-quantum cryptographic algorithms, offering a diverse range of approaches to address different security needs. Selecting the appropriate algorithm requires careful consideration of several factors:
- Security Level: Each algorithm offers a specific security level, reflecting its resistance to attacks from both classical and quantum computers. Choose an algorithm that provides sufficient security for your data sensitivity level.
- Performance: Different algorithms have varying performance characteristics. Some are computationally more intensive than others, impacting the speed and efficiency of your systems. Consider the performance trade-offs against security requirements.
- Implementation Complexity: The ease of integrating an algorithm into your existing infrastructure varies. Some algorithms are easier to implement than others, requiring less development effort and resources.
- Key Size: The size of the cryptographic keys impacts storage and transmission overhead. Larger keys offer higher security but may increase resource consumption.
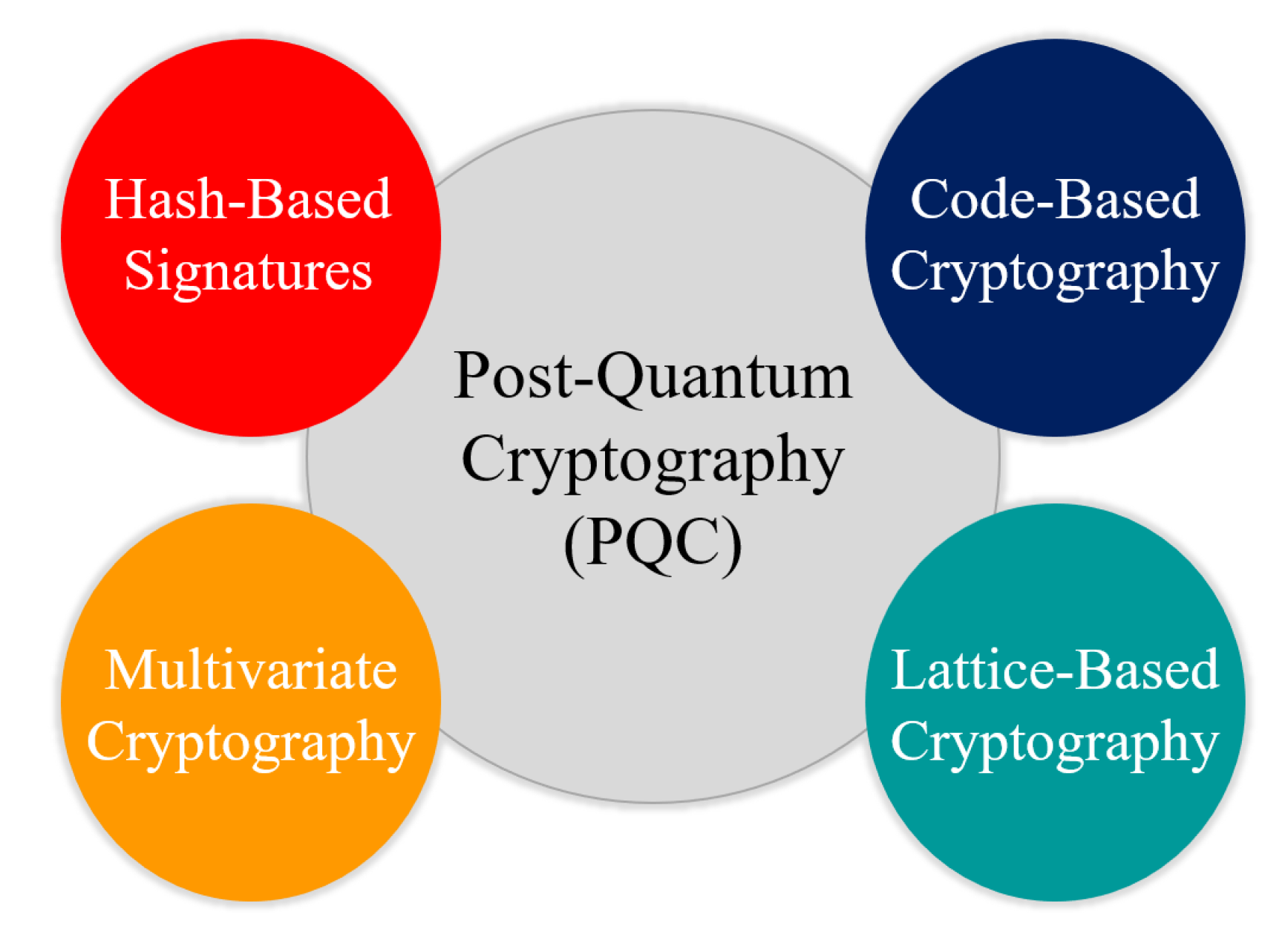
NIST’s standardized algorithms include lattice-based, code-based, multivariate-quadratic, and hash-based cryptography. The "best" algorithm will depend on your specific needs and context. Consulting with cryptography experts is highly recommended to make an informed decision.
3. Gradual Migration: A Phased Approach to Minimize Disruption
Implementing PQC is not a switch-flip operation. A phased migration strategy is crucial to minimize disruption to your business operations. Consider the following phases:
- Pilot Project: Start with a pilot project on a non-critical system to test the chosen algorithm and assess its performance and compatibility with your existing infrastructure.
- Proof-of-Concept: Demonstrate the feasibility of integrating PQC into a critical system before widespread deployment. This allows you to identify and resolve potential issues early on.
- Phased Rollout: Gradually migrate different systems to PQC, prioritizing those handling the most sensitive data. This reduces the risk of widespread failure and allows for continuous monitoring and adjustment.
- Monitoring and Evaluation: Continuously monitor the performance and security of your PQC implementation. Regular audits and security assessments are essential to ensure its effectiveness.
This phased approach minimizes risk, allows for learning and adaptation, and ensures a smoother transition to PQC.
4. Infrastructure Upgrades: Preparing Your Systems for PQC
Implementing PQC may require upgrades to your existing infrastructure. This could involve:
- Hardware Upgrades: Some algorithms are more computationally intensive than others, requiring more powerful hardware. Assess your current hardware capacity and plan for upgrades if necessary.
- Software Updates: You’ll need to update your software libraries and applications to support the chosen PQC algorithm. This may involve integrating new cryptographic libraries or developing custom code.
- Network Infrastructure: Consider the impact of PQC on your network bandwidth and latency. Larger keys and more complex algorithms can increase network overhead.
- Key Management: Secure key management is crucial for PQC. Implement robust key generation, storage, and distribution mechanisms to prevent unauthorized access.
Careful planning and resource allocation are crucial to ensure a smooth infrastructure transition.
5. Security Audits and Penetration Testing: Validating Your Implementation
After implementing PQC, rigorous testing is essential to validate its effectiveness. This involves:
- Security Audits: Conduct regular security audits to identify vulnerabilities and ensure compliance with relevant regulations and standards.
- Penetration Testing: Simulate real-world attacks to assess the resilience of your PQC implementation. This helps identify weaknesses that might be exploited by attackers.
- Vulnerability Scanning: Regularly scan your systems for known vulnerabilities that could compromise your PQC implementation.
- Red Teaming: Employ a red team to simulate sophisticated attacks, testing the effectiveness of your security measures beyond standard penetration testing.
These measures provide confidence that your PQC implementation is robust and effective in protecting your sensitive data.
6. Employee Training and Awareness: The Human Element of Security
The success of any security measure depends on the people who use it. Employee training and awareness are crucial components of a comprehensive PQC strategy:
- Security Awareness Training: Educate employees about the importance of PQC and the potential risks of data breaches.
- Best Practices: Provide training on secure password management, phishing awareness, and other security best practices.
- Incident Response: Develop and implement an incident response plan to handle potential security breaches effectively.
- Regular Updates: Keep employees informed about the latest security threats and best practices.
A well-trained and security-conscious workforce is your first line of defense against cyberattacks.
7. Collaboration and Partnerships: Leveraging External Expertise
Implementing PQC can be a complex undertaking. Collaboration and partnerships can provide valuable support:
- Cryptographic Consultants: Engage experienced cryptographic consultants to guide your PQC implementation and address specific technical challenges.
- Technology Vendors: Partner with technology vendors that offer PQC-enabled products and services.
- Industry Groups: Join industry groups and participate in discussions to stay informed about the latest developments in PQC.
- Government Agencies: Engage with government agencies like NIST to access resources and guidance on PQC implementation.
Leveraging external expertise can significantly streamline the process and ensure a successful implementation.
8. Future-Proofing Your Strategy: Adapting to Evolving Threats
The landscape of cybersecurity is constantly evolving. Your PQC strategy should be adaptable to emerging threats:
- Algorithm Updates: Stay informed about updates and advancements in PQC algorithms and be prepared to migrate to newer, more secure algorithms as needed.
- Threat Intelligence: Monitor threat intelligence feeds to stay aware of emerging threats and vulnerabilities.
- Continuous Monitoring: Continuously monitor your systems for suspicious activity and respond promptly to any security incidents.
- Regular Assessments: Conduct regular security assessments to evaluate the effectiveness of your PQC implementation and identify areas for improvement.
Frequently Asked Questions (FAQs)
Q: When will quantum computers pose a real threat to my business?
A: The timeline for quantum computers capable of breaking current encryption is uncertain. While not imminent, the potential threat is significant enough to warrant proactive planning and implementation of PQC.
Q: How much will implementing PQC cost my business?
A: The cost varies depending on the size and complexity of your organization, the chosen algorithm, and the extent of infrastructure upgrades required. However, the cost of inaction – a data breach – could be far greater.
Q: Will PQC slow down my systems?
A: Some PQC algorithms are more computationally intensive than current algorithms, potentially impacting performance. Careful algorithm selection and infrastructure planning can mitigate this impact.
Q: Can I implement PQC myself, or do I need external help?
A: Implementing PQC can be complex, especially for organizations without in-house cryptographic expertise. Engaging external consultants can significantly simplify the process and reduce risks.
Q: What happens if a new, more powerful quantum computer emerges after I implement PQC?
A: The field of PQC is constantly evolving. Staying informed about algorithm updates and advancements is crucial to ensure ongoing protection. Regular security assessments and monitoring will be essential.
Q: Is PQC a silver bullet?
A: No, PQC is a significant step toward securing data against future quantum threats, but it’s not a complete solution. A layered security approach encompassing PQC, robust access controls, and employee training remains crucial.
This article provides a comprehensive overview of implementing post-quantum encryption in your business. Remember that proactive security is crucial, and the sooner you begin your transition to PQC, the better prepared you’ll be for the future of cybersecurity.
Source: https://csrc.nist.gov/projects/post-quantum-cryptography
Closure
Thank you for reading! Stay with us for more insights on “how to implement post-quantum encryption in your business”.
Make sure to follow us for more exciting news and reviews.
Feel free to share your experience with “how to implement post-quantum encryption in your business” in the comment section.
Keep visiting our website for the latest trends and reviews.
