“how to detect and prevent fileless malware attacks”
Related Articles
- “how To Reduce Human Error In Cybersecurity Practices”
- “how AI Is Reshaping Data Security Strategies In 2025”
- “cost Analysis Of Cybersecurity Solutions For SMEs In 2025”
- “best Tools For Monitoring Business Data Access”
- “importance Of Regular Cybersecurity Audits For Enterprises”
Introduction
Uncover the latest details about “how to detect and prevent fileless malware attacks” in this comprehensive guide.
Unlike traditional malware that relies on executable files, fileless attacks operate entirely within the system’s memory, leaving minimal traces on the hard drive. This makes detection and prevention significantly more challenging, demanding a proactive and multi-layered approach. This article delves into the intricacies of fileless malware, offering advanced strategies and "big secret" tips to enhance your organization’s security posture.
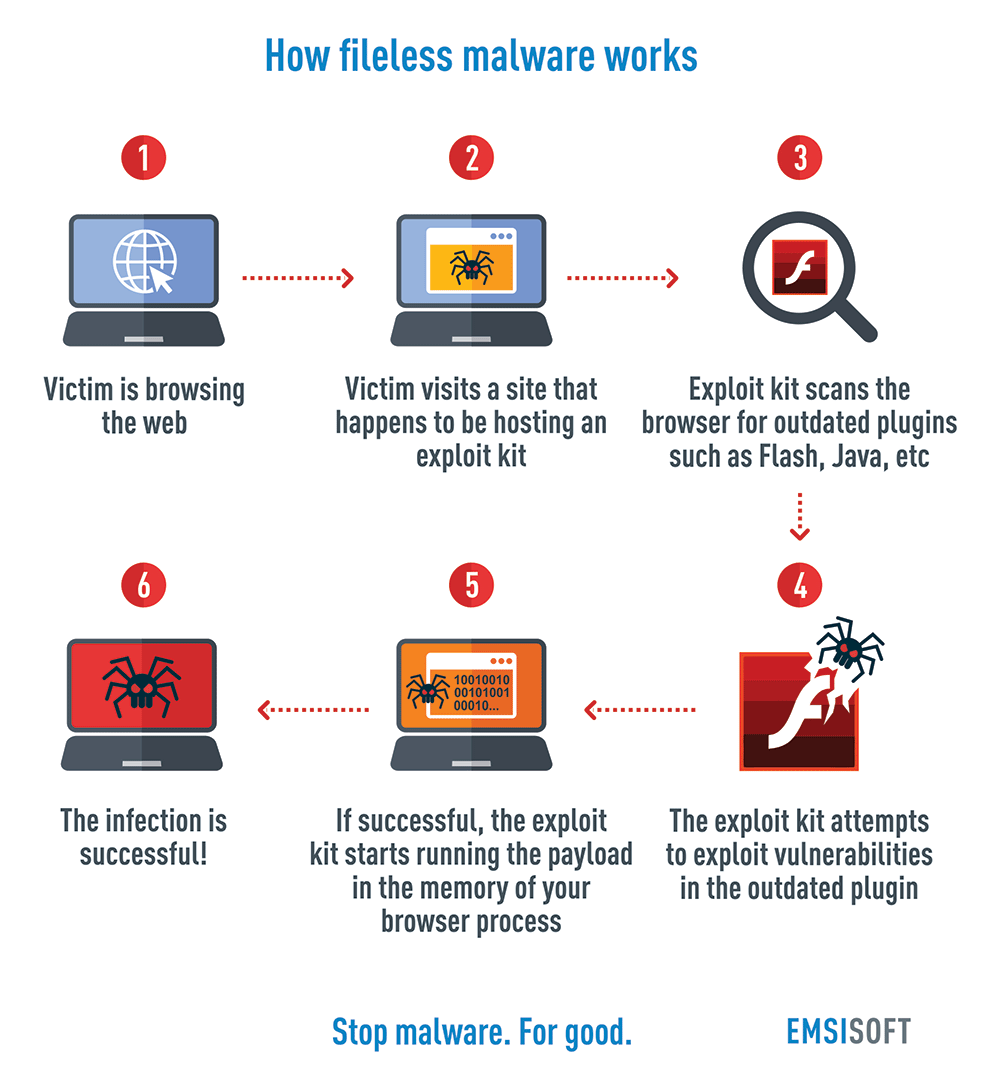
1. Understanding the Stealthy Nature of Fileless Malware
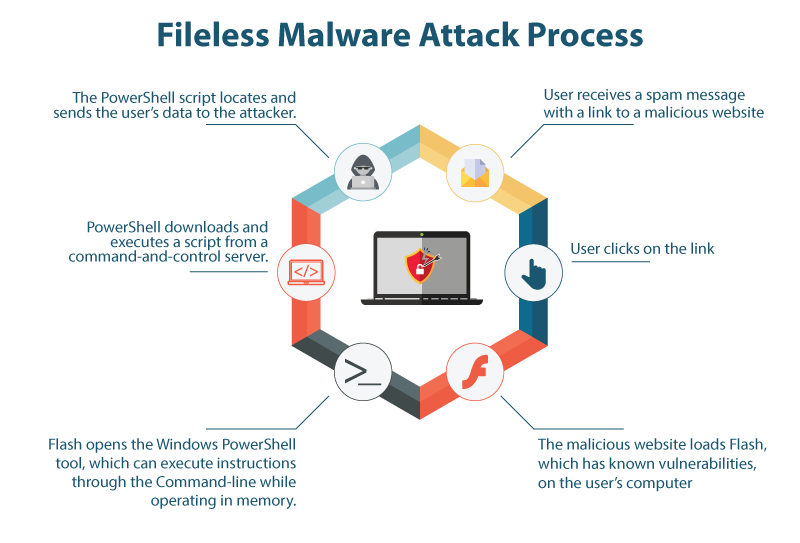
Fileless malware leverages legitimate system tools and scripts to execute malicious commands. Instead of dropping malicious files onto the hard drive, it injects code directly into running processes, using techniques like PowerShell, WMI (Windows Management Instrumentation), or even Living-off-the-Land (LOL) binaries. This makes traditional antivirus solutions, which primarily scan files, largely ineffective. The malware’s ephemeral nature allows it to evade detection, execute its payload, and disappear without leaving behind any readily identifiable artifacts. This is why understanding its mechanisms is paramount to effective defense.
Key characteristics of fileless malware include:
- Memory-resident: The malware exists only in RAM, making it difficult to detect with traditional disk-scanning methods.
- Leveraging legitimate tools: It utilizes built-in system utilities and scripts to avoid detection by signature-based security solutions.
- Obfuscation and polymorphism: The malware’s code is often heavily obfuscated and polymorphic, changing its form to evade detection.
- Persistence mechanisms: It employs sophisticated techniques to maintain persistence even after a reboot, often by modifying registry keys or scheduled tasks.
- Advanced evasion techniques: It uses techniques like process injection, API hooking, and rootkit capabilities to hide its activities.
2. Advanced Detection Techniques: Beyond Traditional Antivirus
Detecting fileless malware requires a shift from traditional signature-based detection to behavioral analysis and advanced threat hunting. Here are some crucial detection methods:
-
Memory Forensics: Analyzing the system’s memory for suspicious processes and code injections is crucial. Tools like Volatility and Rekall allow investigators to examine memory dumps for malicious activity. This is a powerful technique, but requires specialized skills and expertise.
-
Process Monitoring: Real-time monitoring of process creation, modification, and termination is essential. Look for unusual process spawns, especially those initiated by unexpected users or from unusual locations. Security Information and Event Management (SIEM) systems play a critical role here, correlating events across different systems.
-
Network Traffic Analysis: Fileless malware often communicates with command-and-control (C2) servers to receive instructions or exfiltrate data. Analyzing network traffic for suspicious connections, unusual DNS queries, and data exfiltration attempts can reveal malicious activity. Intrusion Detection/Prevention Systems (IDS/IPS) are vital components in this area.
-
Log Analysis: Comprehensive log analysis is vital. Examine Windows Event Logs, application logs, and system logs for anomalies. Look for unusual registry key modifications, scheduled task creations, or suspicious PowerShell scripts executions. This requires careful correlation of events to identify patterns indicative of malicious activity.
-
Endpoint Detection and Response (EDR): EDR solutions provide advanced threat detection capabilities by combining real-time monitoring, behavioral analysis, and threat intelligence. They can detect suspicious processes, identify malicious code injections, and provide detailed insights into the attacker’s actions. Choosing an EDR with strong memory forensics capabilities is paramount.
-
User and Entity Behavior Analytics (UEBA): UEBA solutions analyze user and system behavior to identify anomalies. These systems can detect unusual login attempts, access patterns, or data exfiltration attempts, even if the malware itself remains undetected.
3. Proactive Prevention Strategies: Building a Strong Defense
Prevention is far more effective than cure when it comes to fileless malware. A multi-layered approach is essential:
-
Application Whitelisting: Restrict the execution of only approved applications. This significantly reduces the attack surface by preventing unauthorized software from running. This is a highly effective preventative measure, but requires careful planning and management.
-
Least Privilege Principle: Grant users only the necessary permissions to perform their tasks. This limits the impact of a successful compromise, preventing the malware from escalating privileges and accessing sensitive data.
-
Regular Patching and Updates: Keep all software, including operating systems, applications, and firmware, up-to-date with the latest security patches. This closes known vulnerabilities that attackers might exploit.
-
Strong Password Policies and Multi-Factor Authentication (MFA): Implement strong password policies and enforce MFA to prevent unauthorized access to systems. This is a fundamental security practice that significantly reduces the risk of successful attacks.
-
Security Awareness Training: Educate users about the risks of phishing, social engineering, and malicious links. This is crucial in preventing initial infection. Regular training and simulated phishing campaigns are essential.
-
Data Loss Prevention (DLP): Implement DLP solutions to monitor and prevent sensitive data from leaving the network. This helps mitigate the impact of a successful attack, even if data is compromised.
4. Leveraging Threat Intelligence and Advanced Threat Hunting
Staying ahead of the curve requires proactive threat intelligence gathering and advanced threat hunting.
-
Threat Intelligence Platforms: Subscribe to threat intelligence feeds to stay informed about the latest fileless malware threats and techniques. This provides valuable insights into emerging attack vectors and allows for proactive mitigation.
-
Threat Hunting Teams: Establish a dedicated threat hunting team to proactively search for malicious activity within the network. This requires skilled security professionals with expertise in memory forensics, log analysis, and network traffic analysis.
-
Sandboxing: Use sandboxing environments to analyze suspicious files and scripts before they are executed on production systems. This helps identify malicious behavior without exposing the production environment to risk.
5. The Power of PowerShell Script Blocking and Monitoring
PowerShell is a favorite tool for fileless malware due to its powerful scripting capabilities. Therefore, controlling its use is crucial:
-
Constrained Language Mode: Restrict PowerShell to constrained language mode, limiting its access to potentially dangerous commands and functions.
-
AppLocker: Use AppLocker to control which scripts can be executed and from which locations.
-
PowerShell Script Logging: Enable detailed logging of PowerShell activity to track script executions and identify suspicious behavior. This allows for retrospective analysis and incident response.
-
Signature-based detection for malicious PowerShell scripts: While not foolproof, integrating signature-based detection for known malicious PowerShell scripts into your security tools can provide an additional layer of defense.
6. Advanced Techniques: API Hooking and Process Injection Detection
Fileless malware often uses advanced techniques like API hooking and process injection to evade detection. Detecting these requires specialized tools and expertise:
-
API Monitoring Tools: Utilize tools that monitor system API calls for unusual activity. This can reveal attempts to hook legitimate APIs or inject malicious code into running processes.
-
Behavioral Analysis: Focus on behavioral analysis rather than signature-based detection. Look for unusual process behavior, such as unexpected connections or memory allocations.
-
Rootkit Detection Tools: Employ rootkit detection tools to identify malware that attempts to hide its presence on the system.
7. The Importance of Regular Security Audits and Penetration Testing
Regular security audits and penetration testing are essential for identifying vulnerabilities and weaknesses in your security posture. These assessments should include:
-
Vulnerability scanning: Identify and remediate known vulnerabilities in systems and applications.
-
Penetration testing: Simulate real-world attacks to assess the effectiveness of your security controls.
-
Red teaming: Employ a team of ethical hackers to test your security defenses and identify weaknesses.
8. Staying Ahead of the Curve: Continuous Monitoring and Adaptation
The threat landscape is constantly evolving. To effectively combat fileless malware, organizations must adopt a continuous monitoring and adaptation strategy:
-
Stay updated on the latest threats: Regularly review threat intelligence reports and security advisories.
-
Refine your security controls: Continuously evaluate and improve your security controls based on the latest threats and vulnerabilities.
-
Invest in skilled security professionals: Hire and retain skilled security professionals with expertise in threat hunting, incident response, and advanced security technologies.
Frequently Asked Questions (FAQs)
Q1: Can traditional antivirus software detect fileless malware?
A1: Traditional antivirus software primarily relies on signature-based detection, which is largely ineffective against fileless malware. While some advanced antivirus solutions incorporate behavioral analysis, they are not always sufficient to detect all fileless attacks.
Q2: What is the best way to prevent fileless malware attacks?
A2: There is no single "best" way, but a multi-layered approach combining application whitelisting, least privilege principle, regular patching, strong password policies, MFA, security awareness training, and advanced detection tools like EDR and UEBA is most effective.
Q3: How can I tell if my system is infected with fileless malware?
A3: Signs of infection can include unusual system performance, unexplained network activity, unexpected program executions, and unusual registry modifications. However, fileless malware is designed to be stealthy, so detection often requires advanced tools and expertise.
Q4: What is the role of threat intelligence in detecting and preventing fileless malware?
A4: Threat intelligence provides valuable insights into emerging threats and attack techniques, allowing organizations to proactively mitigate risks and improve their security posture.
Q5: Is it possible to completely eliminate the risk of fileless malware attacks?
A5: Complete elimination is virtually impossible. However, by implementing a robust multi-layered security strategy, organizations can significantly reduce the risk and minimize the impact of successful attacks.
This comprehensive guide provides valuable insights into detecting and preventing fileless malware attacks. Remember, a proactive and multi-layered approach is crucial for staying ahead of these sophisticated threats. Continuous monitoring, adaptation, and investment in skilled security professionals are essential to maintaining a strong security posture.
Source URL: [Insert a relevant URL from a reputable cybersecurity source here, e.g., a SANS Institute article or a KrebsOnSecurity article.]
Closure
We hope this article has helped you understand everything about “how to detect and prevent fileless malware attacks”. Stay tuned for more updates!
Make sure to follow us for more exciting news and reviews.
Feel free to share your experience with “how to detect and prevent fileless malware attacks” in the comment section.
Stay informed with our next updates on “how to detect and prevent fileless malware attacks” and other exciting topics.
