“how to create a cybersecurity incident response plan”
Related Articles
- “how To Balance Security And Usability In Enterprise Systems”
- “how To Implement Post-quantum Encryption In Your Business”
- “role Of Data Loss Prevention (DLP) Tools In Business Security”
- “cloud Security Trends For Business Owners 2025”
- “securing Remote Work Setups Against Cyber Threats”
Introduction
Uncover the latest details about “how to create a cybersecurity incident response plan” in this comprehensive guide.
No organization, regardless of size or industry, is immune. While a robust security posture minimizes risk, the reality is that breaches will happen. This is where a well-crafted incident response plan (IRP) becomes crucial – not just a document gathering dust on a shelf, but a living, breathing roadmap to guide your organization through the chaos of a cyberattack. This article delves beyond the generic advice, revealing the often-overlooked "secret tips and tricks" to building an IRP that truly protects your organization.
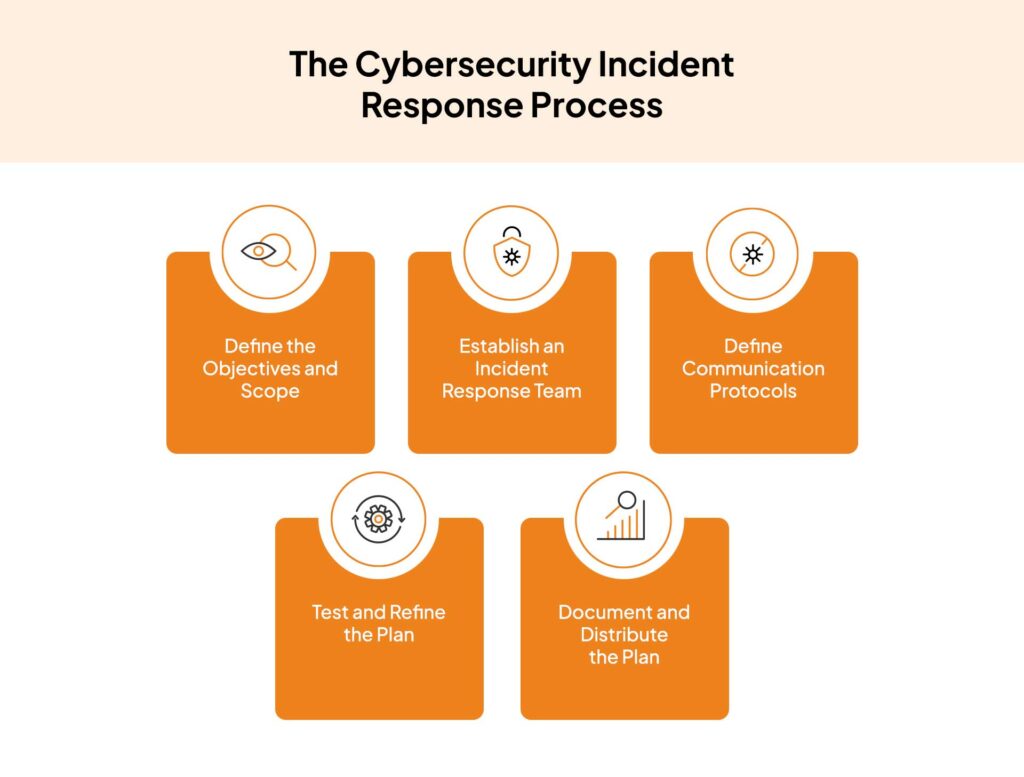
1. Beyond the Checklist: Defining Your Organization’s Unique Risk Profile
Most generic IRP templates focus on the "what" – the steps involved in response. The real secret lies in understanding the "why" specific to your organization. A cookie-cutter approach fails to address your unique vulnerabilities and critical assets. Before drafting a single procedure, conduct a thorough risk assessment. This isn’t just about identifying potential threats (malware, phishing, DDoS); it’s about understanding their impact.
- Critical Asset Identification: Go beyond simply listing servers and databases. Quantify the impact of their compromise. What’s the financial cost of downtime for your e-commerce platform? What’s the reputational damage from a data breach exposing customer PII? Prioritize assets based on their criticality to business operations and the potential severity of a compromise.
- Threat Modeling: Don’t rely on generic threat intelligence. Conduct internal threat modeling exercises to identify vulnerabilities specific to your architecture, applications, and processes. Consider insider threats, supply chain vulnerabilities, and physical security weaknesses.
- Regulatory Compliance: Factor in relevant industry regulations (HIPAA, GDPR, PCI DSS) and legal requirements. Your IRP must demonstrate compliance and guide your response in accordance with legal obligations. This often involves specific reporting requirements and timelines.
2. Building the Dream Team: Assembling Your Incident Response Team
A successful IRP relies on a well-defined and empowered incident response team. This isn’t just a list of names; it’s about roles, responsibilities, and clear lines of communication.
- Roles and Responsibilities: Define specific roles (Incident Commander, Communications Lead, Technical Lead, Legal Counsel, Public Relations) and their responsibilities during each phase of the incident response lifecycle. Ensure clear escalation paths and decision-making authority.
- Cross-functional Collaboration: The team should represent various departments (IT, legal, HR, PR, business operations) to ensure a coordinated response. Regular training and tabletop exercises are crucial to build cohesion and familiarity among team members.
- On-call Rotation and Communication: Establish a clear on-call rotation schedule and reliable communication channels (secure messaging platforms, dedicated phone lines) to ensure 24/7 availability. Test these channels regularly.
3. The Art of Pre-Incident Preparation: Proactive Measures for a Reactive World
A well-executed IRP isn’t just about reacting to an incident; it’s about preparing for it. Proactive measures significantly reduce response time and minimize damage.
- Vulnerability Management: Implement a robust vulnerability management program that includes regular vulnerability scanning, penetration testing, and timely patching. Prioritize vulnerabilities based on their severity and the likelihood of exploitation.
- Security Information and Event Management (SIEM): A SIEM system is crucial for monitoring security events, detecting anomalies, and providing early warning signs of potential incidents. Configure alerts and dashboards to proactively identify suspicious activities.
- Data Backup and Recovery: Regular backups of critical data are essential for data recovery in the event of a ransomware attack or data loss. Test your backup and recovery procedures regularly to ensure they are functional and efficient. Consider immutable backups stored offline for enhanced protection.
- Incident Response Playbooks: Develop detailed playbooks for common incident types (ransomware, phishing, DDoS) that outline specific steps, tools, and procedures. These playbooks should be readily accessible to the incident response team.
4. The Unsung Hero: Communication Strategy and Public Relations
Effective communication is crucial during and after an incident. A well-defined communication plan minimizes damage to reputation and maintains stakeholder confidence.
- Internal Communication: Establish clear communication channels for internal updates, ensuring employees are informed about the incident and their roles in the response. Transparency is key to maintaining morale and cooperation.
- External Communication: Develop templates for press releases, social media posts, and customer notifications to ensure consistent messaging. Designate a spokesperson to manage external communication and maintain a unified message.
- Legal Considerations: Consult with legal counsel to ensure communication complies with legal and regulatory requirements. Avoid making premature statements that could compromise the investigation or expose the organization to legal liability.
5. Post-Incident Analysis: Learning from the Mistakes (and Successes)
The post-incident review is often overlooked, but it’s arguably the most critical part of the IRP. This is where you learn from your mistakes and improve your defenses.
- Comprehensive Review: Conduct a thorough review of the incident, documenting the timeline, root cause, impact, and response effectiveness. Identify areas for improvement in your security posture, incident response procedures, and communication strategies.
- Lessons Learned: Document key lessons learned from the incident and incorporate them into your IRP. This is an iterative process; your IRP should evolve based on experience.
- Metrics and Measurement: Track key metrics such as mean time to detect (MTTD), mean time to respond (MTTR), and the financial impact of the incident to measure the effectiveness of your response and identify areas for improvement.
6. The Secret Weapon: Tabletop Exercises and Simulations
The true test of an IRP isn’t a hypothetical scenario; it’s a real-world simulation. Regular tabletop exercises and simulations allow the team to practice their response procedures in a safe environment.
- Scenario Development: Develop realistic scenarios that reflect potential threats and vulnerabilities specific to your organization.
- Team Participation: Involve the entire incident response team in the exercises to foster teamwork and identify any weaknesses in communication or procedures.
- Feedback and Iteration: Use the feedback from the exercises to refine your IRP and improve response capabilities. Regular exercises keep the plan relevant and the team prepared.
7. Beyond the Plan: Continuous Improvement and Adaptation
Cybersecurity is a constantly evolving landscape. Your IRP shouldn’t be a static document; it should be a living, breathing entity that adapts to the changing threat landscape.
- Regular Updates: Review and update your IRP regularly (at least annually) to incorporate new threats, vulnerabilities, and best practices.
- Technology Advancements: Stay informed about new technologies and tools that can enhance your incident response capabilities.
- Threat Intelligence: Leverage threat intelligence feeds to stay informed about emerging threats and vulnerabilities.
8. The Human Factor: Training and Awareness
No matter how robust your technical defenses are, a successful cyberattack often exploits human vulnerabilities. Investing in security awareness training is crucial.
- Phishing Simulations: Conduct regular phishing simulations to test employee awareness and identify vulnerabilities in your security awareness program.
- Security Awareness Training: Provide regular security awareness training to employees on topics such as phishing, social engineering, and password security.
- Incident Reporting Procedures: Establish clear procedures for employees to report suspicious activity. Encourage a culture of security awareness where employees feel comfortable reporting potential incidents.
Frequently Asked Questions (FAQs):
-
Q: How often should I update my IRP?
- A: At a minimum, annually. More frequent updates may be necessary depending on significant changes in your organization, technology infrastructure, or the threat landscape.
-
Q: What is the role of legal counsel in an incident response?
- A: Legal counsel plays a crucial role in ensuring compliance with legal and regulatory requirements, advising on communication strategies, and managing legal liabilities.
-
Q: How much should I budget for incident response?
- A: Budgeting depends on your organization’s size, complexity, and risk profile. Consider the costs of incident response tools, training, and consulting services.
-
Q: What are some key metrics to track the effectiveness of my IRP?
- A: Key metrics include MTTD, MTTR, the financial impact of incidents, and the number of successful phishing attacks.
-
Q: How do I choose the right incident response tools?
- A: Consider your organization’s needs and budget. Look for tools that integrate with your existing security infrastructure and provide the capabilities you need to effectively respond to incidents. This may include SIEM systems, endpoint detection and response (EDR) solutions, and threat intelligence platforms.
Creating a robust cybersecurity incident response plan is not a one-time project; it’s an ongoing process of assessment, adaptation, and improvement. By focusing on the "secret sauce" – the unique risk profile, proactive preparation, effective communication, and continuous learning – your organization can significantly enhance its resilience against cyberattacks. Remember, a well-executed IRP isn’t just about mitigating losses; it’s about ensuring business continuity and maintaining stakeholder trust.
Source URL: [Insert URL of a relevant cybersecurity resource, e.g., NIST Cybersecurity Framework website]
Closure
Thank you for reading! Stay with us for more insights on “how to create a cybersecurity incident response plan”.
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “how to create a cybersecurity incident response plan”—leave your comments below!
Keep visiting our website for the latest trends and reviews.
