“how to balance security and usability in enterprise systems”
Related Articles
- “impact Of Quantum Computing On Business Data Encryption”
- “how To Secure IoT Devices In Corporate Networks”
- “top-rated Cybersecurity Software For Businesses In 2025”
- “how AI Is Reshaping Data Security Strategies In 2025”
- “data Security Trends For Financial Institutions In 2025”
Introduction
Join us as we explore “how to balance security and usability in enterprise systems”, packed with exciting updates
They manage crucial data, facilitate complex workflows, and drive critical business processes. However, the inherent complexity of these systems creates a constant tension between security and usability. Implementing robust security measures often leads to a less user-friendly experience, while prioritizing ease of use can inadvertently compromise security. This article delves into the often-overlooked strategies and "big secret" tips for achieving the delicate balance between these two critical aspects.
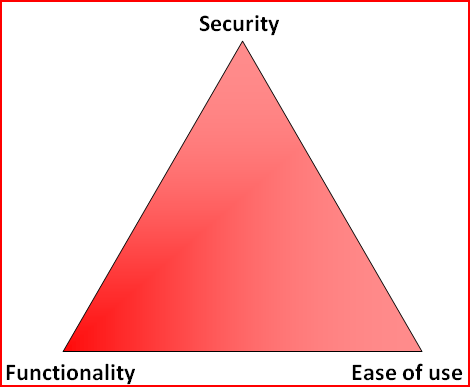
1. Understanding the Enemy: Recognizing the Security-Usability Trade-off
The fundamental challenge lies in the inherent conflict between security and usability. Strong security often demands intricate authentication processes, access controls, and data encryption, all of which can increase the time and effort required for users to complete tasks. Conversely, simplifying the user experience might involve reducing security measures, leaving the system vulnerable to attacks.
This isn’t a binary choice, however. The goal isn’t to sacrifice one for the other, but to find the optimal point on the spectrum where both are adequately addressed. This requires a deep understanding of the specific risks and vulnerabilities faced by the organization, coupled with a thorough assessment of user needs and capabilities. A risk-based approach is crucial, focusing security efforts on the most critical assets and processes.
2. The Power of Context-Aware Security: Adaptive Access Control
One of the most effective strategies for balancing security and usability is implementing context-aware security. This involves dynamically adjusting security measures based on various contextual factors, such as the user’s location, device, time of day, and the sensitivity of the data being accessed.
For example, a user accessing sensitive financial data from a known and trusted corporate network might experience minimal security prompts. However, the same user attempting to access the same data from a public Wi-Fi network might be subjected to multi-factor authentication (MFA) and stricter access controls. This adaptive approach ensures strong security without imposing unnecessary burdens on users in safe environments. Sophisticated systems can leverage machine learning to continuously refine these adaptive security measures based on observed user behavior and threat patterns.
3. User-Centric Design: Security Shouldn’t Feel Like a Punishment
Security measures should be integrated seamlessly into the user experience rather than presented as an obstacle. Poorly designed security systems can frustrate users, leading to workarounds that compromise security. A user-centric design approach prioritizes user experience while ensuring security remains paramount.
This involves:
- Intuitive Interfaces: Security features should be easy to understand and use, with clear instructions and minimal jargon. Complex processes should be streamlined and simplified wherever possible.
- Minimal Friction: Authentication and authorization processes should be as quick and efficient as possible, without sacrificing security. Biometric authentication, single sign-on (SSO), and passwordless authentication methods can significantly improve the user experience.
- Clear Feedback: Users should receive clear and concise feedback on their security actions. This includes confirmation messages, error messages, and progress indicators.
- Progressive Disclosure: Only reveal necessary security features when required. Avoid overwhelming users with complex settings and options that they may not need.
- Usability Testing: Conduct thorough usability testing with real users to identify potential friction points and areas for improvement. Iterative design based on user feedback is crucial for creating a secure and user-friendly system.

4. Leveraging Technology: Automation and AI for Enhanced Security
Modern technologies play a pivotal role in achieving the desired balance. Automation and Artificial Intelligence (AI) can significantly enhance security without sacrificing usability.
- Automated Threat Detection: AI-powered systems can monitor user activity and network traffic for suspicious behavior, automatically identifying and mitigating potential threats. This reduces the burden on security personnel while improving the overall security posture.
- Behavioral Biometrics: This technology analyzes user behavior patterns to identify anomalies that might indicate unauthorized access. It can detect unusual login attempts, keyboard typing patterns, or mouse movements, providing an additional layer of security without requiring users to remember complex passwords.
- Security Information and Event Management (SIEM): SIEM systems collect and analyze security logs from various sources, providing a comprehensive view of the security landscape. They can automate incident response, reducing the time it takes to identify and address security breaches.
5. Training and Education: Empowering Users to Be Part of the Solution
Security is not solely the responsibility of the IT department. End-users play a critical role in maintaining the security of enterprise systems. Comprehensive training and education programs can empower users to make informed decisions and contribute to a stronger security posture.
This includes:
- Security Awareness Training: Regular training programs should educate users about common security threats, such as phishing scams, malware, and social engineering attacks.
- Best Practices: Users should be trained on best practices for password management, data security, and safe browsing habits.
- Incident Reporting: Establish clear procedures for reporting security incidents, ensuring that potential threats are identified and addressed promptly.
6. The Importance of Regular Audits and Assessments: Continuous Improvement
Maintaining the balance between security and usability is an ongoing process. Regular audits and assessments are essential to identify vulnerabilities and areas for improvement. These assessments should encompass both technical and human factors, evaluating the effectiveness of security measures and the user experience. Penetration testing and vulnerability scanning can identify potential weaknesses in the system, while user surveys and feedback sessions can provide insights into user perceptions and experiences.
7. Zero Trust Architecture: Building a Secure Foundation
Adopting a Zero Trust architecture is a crucial step in enhancing security without compromising usability. This approach assumes no implicit trust, verifying every user and device before granting access to resources. While it might seem counterintuitive, a well-implemented Zero Trust model can simplify access management and enhance security by reducing the attack surface. It allows for granular access control, ensuring that users only have access to the resources they need, reducing the potential impact of a security breach.
8. Embrace Simplicity: Less is Often More
Finally, a core principle to remember is that simplicity is often the key. Overly complex security measures can be counterproductive, leading to user frustration and workarounds that compromise security. Strive for simplicity in design, implementation, and user interaction. A well-designed system that is easy to use and understand is more likely to be adopted and followed, leading to a stronger security posture.
Frequently Asked Questions (FAQs)
Q: How can we balance security and usability when implementing multi-factor authentication (MFA)?
A: While MFA adds a layer of security, it can be cumbersome. Choose MFA methods that are convenient for users, such as push notifications or biometric authentication. Also, carefully consider where MFA is absolutely necessary, applying it to sensitive systems and data rather than every access point.
Q: What are some best practices for password management in an enterprise setting?
A: Implement strong password policies that require complexity and regular changes. Encourage the use of password managers to help users securely store and manage their credentials. Consider passwordless authentication options wherever feasible.
Q: How can we ensure that security measures don’t hinder productivity?
A: Through careful design and implementation. Prioritize user experience, integrate security seamlessly into workflows, and provide adequate training and support. Use automation and AI to streamline security processes and reduce manual intervention.
Q: How often should security audits be conducted?
A: The frequency of audits depends on the sensitivity of the data and the risk profile of the organization. However, regular audits, at least annually, are essential to maintain a strong security posture.
Q: What is the role of user feedback in improving security and usability?
A: User feedback is crucial. Regularly solicit feedback through surveys, focus groups, and usability testing to identify areas for improvement in both security and user experience.
This comprehensive exploration of balancing security and usability in enterprise systems underscores the necessity for a holistic, iterative approach. By understanding the challenges, leveraging technology, and prioritizing user-centric design, organizations can create secure and efficient systems that empower their workforce while mitigating risks. The key is continuous improvement and adaptation based on ongoing assessment and user feedback.
Source URL: [Insert a relevant URL from a reputable source, such as NIST, SANS Institute, or a cybersecurity vendor’s website here]
Closure
Thank you for reading! Stay with us for more insights on “how to balance security and usability in enterprise systems”.
Make sure to follow us for more exciting news and reviews.
Feel free to share your experience with “how to balance security and usability in enterprise systems” in the comment section.
Stay informed with our next updates on “how to balance security and usability in enterprise systems” and other exciting topics.
