How quantum computing impacts business data encryption
Related Articles
- “importance Of Regular Cybersecurity Audits For Enterprises”
- “how To Create A Cybersecurity Response Plan For SMBs”
- “trends In Cybersecurity Education For Employees In 2025”
- “best Practices For Securing Business Data Backups”
- “impact Of Remote Work On Data Security Risks In 2025”
Introduction
In this article, we dive into How quantum computing impacts business data encryption, giving you a full overview of what’s to come
Businesses rely on robust encryption to protect sensitive customer information, intellectual property, and financial records. However, a looming shadow threatens this foundation: quantum computing. While still in its nascent stages, the potential of quantum computers to break widely used encryption algorithms presents a significant challenge, demanding a proactive and comprehensive response from businesses worldwide. This article delves into the intricacies of this threat, exploring how quantum computing impacts business data encryption and outlining strategies for mitigating the risk.
1. Understanding the Quantum Threat: Shor’s Algorithm and its Implications
The core of the quantum threat lies in Shor’s algorithm, a revolutionary quantum algorithm developed by Peter Shor in 1994. This algorithm efficiently factors large numbers into their prime components, a problem that is computationally intractable for even the most powerful classical computers. The security of many widely used public-key cryptography systems, such as RSA and ECC (Elliptic Curve Cryptography), relies on the difficulty of this factoring problem. Shor’s algorithm, when implemented on a sufficiently powerful quantum computer, could break these systems, rendering vast amounts of encrypted data vulnerable.
This isn’t a theoretical threat relegated to the distant future. While fault-tolerant, large-scale quantum computers are still under development, significant progress is being made. Governments and private companies are investing heavily in quantum computing research, and experts predict that within the next decade or two, quantum computers capable of breaking current encryption standards could emerge. The implications for businesses are profound: sensitive data encrypted today could be easily decrypted tomorrow, leading to massive data breaches, financial losses, and reputational damage.
2. The Vulnerability of Current Encryption Standards: RSA, ECC, and Beyond
RSA, based on the difficulty of factoring large numbers, and ECC, relying on the complexity of the elliptic curve discrete logarithm problem, are the cornerstones of modern online security. These algorithms are used to secure everything from online banking transactions and email communication to secure web browsing (HTTPS) and digital signatures. Their vulnerability to Shor’s algorithm necessitates a fundamental shift in our approach to data encryption.
Other cryptographic systems, while not directly reliant on factoring, could also be impacted indirectly. For instance, the security of many digital signature schemes depends on the security of underlying public-key cryptosystems like RSA or ECC. A successful attack on these underlying systems would compromise the integrity and authenticity of the digital signatures, leading to widespread trust issues.
3. Post-Quantum Cryptography: The Race to Develop Quantum-Resistant Algorithms
Recognizing the impending threat, the cryptographic community is actively engaged in developing post-quantum cryptography (PQC). PQC refers to cryptographic algorithms that are believed to be resistant to attacks from both classical and quantum computers. These algorithms rely on mathematical problems that are believed to be hard for both classical and quantum computers to solve, offering a potential safeguard against the quantum threat.
Several promising PQC candidates are currently under consideration by standardization bodies like NIST (National Institute of Standards and Technology). These algorithms fall into various categories, including lattice-based cryptography, code-based cryptography, multivariate cryptography, hash-based cryptography, and isogeny-based cryptography. Each approach offers different strengths and weaknesses, and the selection of the most suitable algorithm will depend on the specific application and security requirements.
4. Migrating to Post-Quantum Cryptography: A Gradual and Strategic Approach

Migrating to PQC is not a simple switch-and-go process. It requires a carefully planned and phased approach. Businesses need to:
- Assess their current cryptographic infrastructure: Identify all systems and applications that rely on vulnerable encryption algorithms.
- Evaluate PQC candidates: Determine which PQC algorithms are best suited for their specific needs, considering factors such as performance, security level, and implementation complexity.
- Develop and test migration strategies: Create a detailed plan for migrating to PQC, including testing the new algorithms in a controlled environment to ensure compatibility and functionality.
- Implement and monitor: Gradually deploy PQC algorithms across their systems, closely monitoring performance and security.
- Plan for key management: PQC introduces new key management challenges that need to be addressed proactively.
This migration process will likely span several years, requiring significant investment in time, resources, and expertise. Early adoption is crucial to avoid being caught unprepared when quantum computers reach a level of maturity that threatens current encryption standards.
5. Beyond Algorithm Changes: The Broader Implications for Data Security
The quantum threat extends beyond simply replacing algorithms. It necessitates a holistic reassessment of data security practices. This includes:
- Strengthening key management: Implementing robust key management systems is critical to protect the integrity of cryptographic keys, both for current and post-quantum algorithms.
- Improving data governance: Establishing clear policies and procedures for handling sensitive data, including access control, data loss prevention, and incident response.
- Investing in cybersecurity expertise: Businesses need to invest in training and education to develop the necessary expertise to manage the transition to PQC and address the broader implications of quantum computing on data security.
- Staying informed about advancements: The field of quantum computing and cryptography is rapidly evolving. Businesses need to stay informed about the latest developments to ensure their security measures remain effective.
6. Collaboration and Standardization: A Collective Effort
Addressing the quantum threat requires a collaborative effort across industry, government, and academia. Standardization efforts, such as those led by NIST, are crucial for ensuring interoperability and widespread adoption of PQC algorithms. Collaboration between businesses and security experts can help accelerate the development and deployment of quantum-resistant solutions. Open-source initiatives and shared best practices can further enhance the security posture of the entire ecosystem.
7. The Future of Data Encryption in the Quantum Era
The transition to a post-quantum world will be a significant undertaking, but it is essential for safeguarding the integrity and confidentiality of business data. The future of data encryption will likely involve a combination of post-quantum algorithms, improved key management practices, and a more comprehensive approach to data security. Businesses that proactively address the quantum threat will be better positioned to protect their valuable assets and maintain their competitive edge in the years to come. The focus will shift from relying solely on computational hardness to a more multifaceted approach incorporating advanced techniques like lattice-based cryptography and potentially even quantum key distribution (QKD) for ultimate security.
Frequently Asked Questions (FAQs)
Q1: When will quantum computers be able to break current encryption?
A1: It’s difficult to give a precise date. While significant progress is being made, the timeline for building large-scale, fault-tolerant quantum computers capable of breaking widely used encryption remains uncertain. Estimates range from a few years to several decades. However, proactive preparation is crucial, as the time needed for migration is substantial.
Q2: Is my data already at risk?
A2: Your data is not currently at risk from quantum computers, but data encrypted today could be vulnerable in the future when sufficiently powerful quantum computers become available. The key is to plan for the future and migrate to post-quantum cryptography before this becomes a reality.
Q3: What is the cost of migrating to post-quantum cryptography?
A3: The cost will vary depending on the size and complexity of a business’s IT infrastructure. It will involve costs associated with assessing current systems, evaluating and selecting PQC algorithms, developing and testing migration strategies, implementing the new algorithms, and ongoing maintenance and support.
Q4: Are all PQC algorithms equally secure?
A4: No. Different PQC algorithms offer different levels of security and performance characteristics. The choice of algorithm will depend on the specific application and security requirements. NIST’s standardization process aims to select algorithms that provide a high level of security and are suitable for widespread adoption.
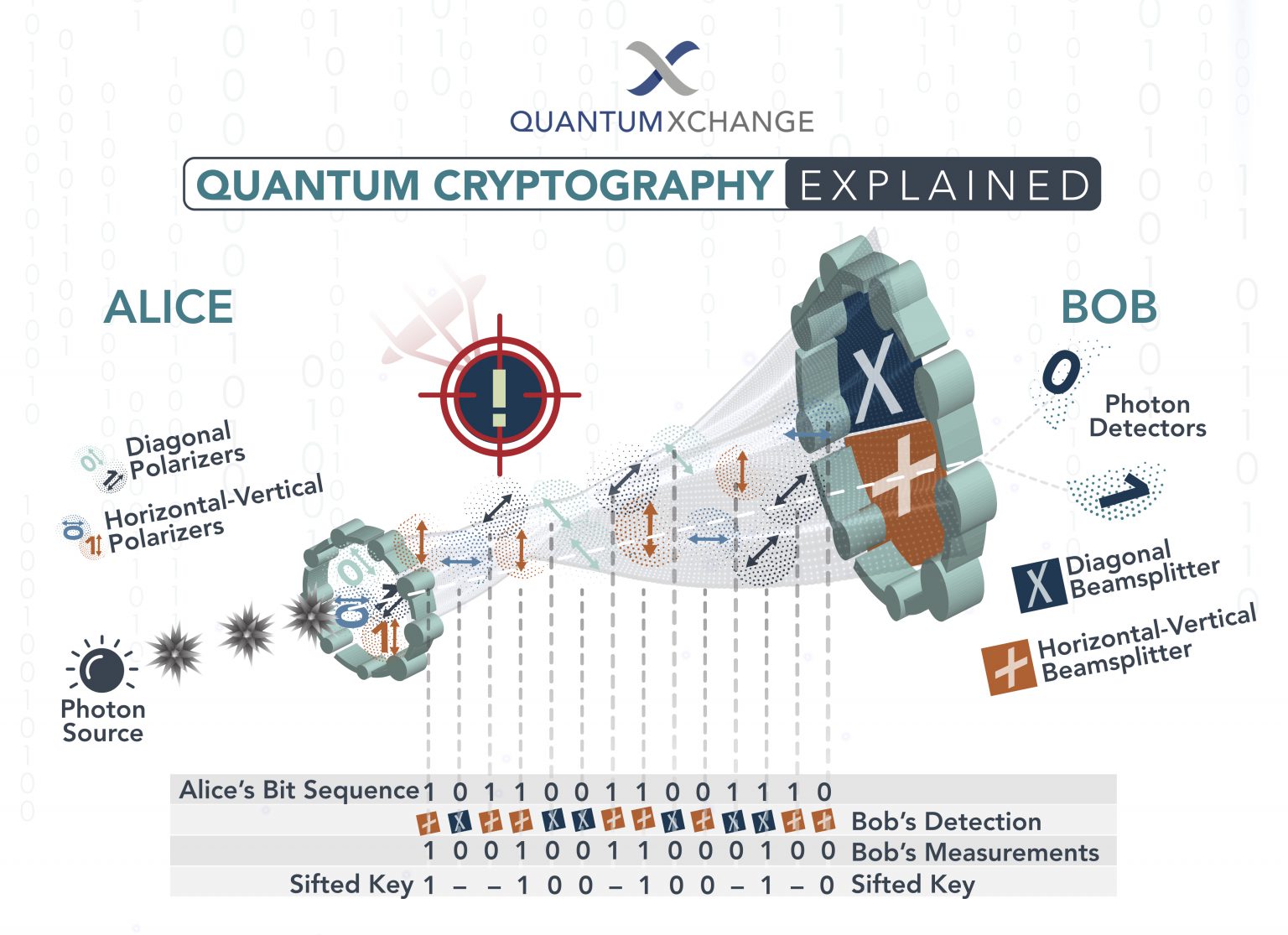
Q5: What role does quantum key distribution (QKD) play?
A5: QKD offers a fundamentally different approach to secure communication by leveraging the principles of quantum mechanics to distribute cryptographic keys. While promising, QKD currently faces limitations in terms of distance and infrastructure requirements. It’s more likely to complement, rather than entirely replace, post-quantum cryptographic algorithms in the near future.
This is a rapidly evolving field, and staying informed is crucial for businesses to protect their data in the quantum era. Continuous monitoring of advancements in quantum computing and cryptography is essential for maintaining a strong security posture.
Source URL: [Insert a relevant URL from a reputable source such as NIST, a cybersecurity firm, or an academic institution discussing post-quantum cryptography. For example, a NIST page on post-quantum cryptography would be appropriate.]
Closure
We hope this article has helped you understand everything about How quantum computing impacts business data encryption. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on How quantum computing impacts business data encryption!
Feel free to share your experience with How quantum computing impacts business data encryption in the comment section.
Keep visiting our website for the latest trends and reviews.
