“how 5G technology affects business data security”
Related Articles
- “role Of Endpoint Detection And Response (EDR) In Business Security”
- “ransomware Recovery Strategies For Enterprises In 2025”
- “AI-driven Threat Detection Tools For Businesses”
- “data Security Trends For Financial Institutions In 2025”
- “how To Secure IoT Devices In Corporate Networks”
Introduction
Uncover the latest details about “how 5G technology affects business data security” in this comprehensive guide.
Businesses eagerly anticipate the transformative potential, from enhanced IoT deployments to streamlined cloud operations. However, this technological leap comes with a significant challenge: a dramatically altered landscape for business data security. While 5G offers numerous advantages, it also introduces new vulnerabilities and attack vectors that require careful consideration and proactive mitigation. This article delves into the intricate relationship between 5G and business data security, uncovering both the inherent risks and the strategies for effective protection.
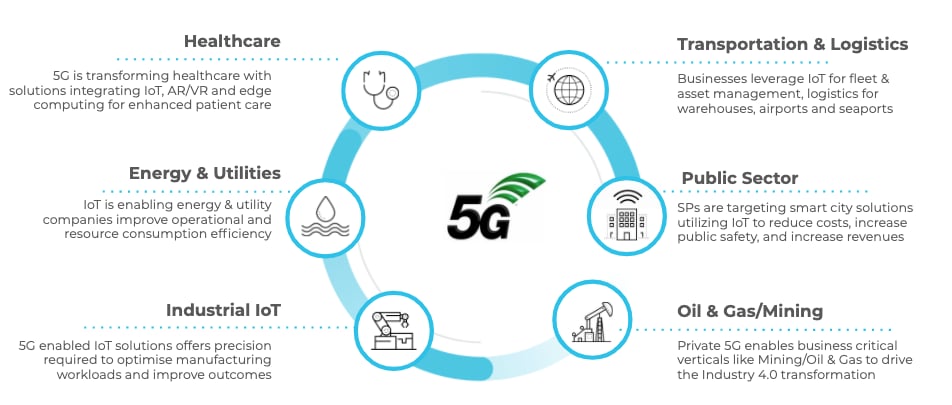
1. The Expanded Attack Surface: More Devices, More Vulnerabilities
5G’s promise of ubiquitous connectivity fuels the Internet of Things (IoT) explosion. Billions of interconnected devices – from smart sensors and industrial robots to wearable health trackers – will generate and transmit vast amounts of sensitive business data. This massive expansion of the network perimeter significantly increases the potential attack surface. Each connected device represents a potential entry point for malicious actors, and even a single compromised device can provide access to the entire network. The sheer volume of devices makes comprehensive security management incredibly challenging, demanding sophisticated monitoring and vulnerability management systems. Moreover, many IoT devices lack robust security features, creating inherent weaknesses that can be exploited. This necessitates a shift towards a more holistic security approach, moving beyond traditional perimeter-based defenses.
2. Increased Data Velocity and Volume: A Security Nightmare
5G’s lightning-fast speeds drastically increase the velocity and volume of data flowing through business networks. This presents a dual challenge for security. First, the sheer volume of data makes real-time threat detection and response far more complex. Traditional security systems may struggle to keep pace, leading to delays in identifying and mitigating breaches. Second, the high data velocity makes it harder to analyze traffic for malicious activity. Advanced techniques like deep packet inspection become crucial, but these require significant processing power and can introduce latency issues if not implemented efficiently. Businesses must invest in scalable and intelligent security solutions capable of handling the increased data load without compromising performance.
3. Network Slicing and its Security Implications
5G’s network slicing capability allows operators to create virtual networks tailored to specific applications, offering customized quality of service (QoS) and security profiles. While this provides flexibility, it also introduces complexity in security management. Each slice requires its own security configuration, increasing the administrative burden and the risk of misconfiguration. A vulnerability in one slice could potentially compromise other slices if not properly isolated. Effective network slicing security requires robust segmentation and access control mechanisms, as well as careful planning and implementation to ensure inter-slice security.
4. Edge Computing and the Decentralization of Security
5G’s architecture promotes edge computing, processing data closer to the source rather than relying solely on centralized cloud servers. While this reduces latency and improves responsiveness, it also decentralizes security responsibilities. Securing numerous edge devices and ensuring consistent security policies across distributed locations presents a significant challenge. Businesses need to adopt a distributed security model, incorporating security measures at the edge while maintaining centralized visibility and control. This requires robust edge security gateways, automated threat response mechanisms, and secure communication protocols between edge devices and the core network.
5. Enhanced Mobile Threat Landscape: New Attack Vectors
5G’s enhanced mobile capabilities also broaden the attack surface for mobile devices. The increased bandwidth and lower latency make mobile devices more attractive targets for malicious actors. New attack vectors emerge, including attacks targeting the 5G radio access network (RAN) itself, which could disrupt service or compromise data in transit. Businesses need to strengthen their mobile device security posture, including implementing mobile device management (MDM) solutions, enforcing strong authentication, and deploying mobile threat defense (MTD) technologies. Regular security awareness training for employees is also crucial to mitigate risks associated with phishing and other social engineering attacks targeting mobile devices.

6. The Human Factor: A Persistent Weakness
Despite technological advancements, the human factor remains a significant vulnerability in any security system. Phishing attacks, social engineering, and insider threats continue to pose major risks, irrespective of the underlying network technology. 5G’s increased connectivity and data volume can actually exacerbate these risks, providing more opportunities for attackers to exploit human vulnerabilities. Businesses must invest in comprehensive security awareness training, robust access control measures, and effective incident response plans to mitigate the human element. Regular security audits and penetration testing can help identify and address potential weaknesses before they are exploited.
7. Regulatory Compliance and Data Sovereignty
The increasing reliance on 5G for business operations necessitates compliance with a range of data privacy and security regulations. GDPR, CCPA, and other regional regulations impose stringent requirements on how businesses collect, process, and protect personal and sensitive data. Businesses must ensure their 5G deployments comply with these regulations, including data encryption, access control, and data breach notification procedures. The concept of data sovereignty also becomes increasingly relevant, requiring businesses to consider the location of their data storage and processing in relation to applicable regulations.
8. Proactive Security Strategies for the 5G Era
Navigating the security challenges presented by 5G requires a multi-layered and proactive approach. This includes:
- Zero Trust Security: Adopting a zero-trust model, where no user or device is implicitly trusted, regardless of location. This requires strong authentication, authorization, and continuous monitoring of all network activity.
- AI-Powered Security: Leveraging artificial intelligence and machine learning to detect and respond to threats in real-time. AI can analyze vast amounts of data to identify anomalies and predict potential attacks.
- Secure Network Segmentation: Dividing the network into smaller, isolated segments to limit the impact of a breach. This restricts the lateral movement of attackers within the network.
- End-to-End Encryption: Encrypting data at rest and in transit to protect it from unauthorized access. This is crucial for securing sensitive data transmitted over the 5G network.
- Regular Security Audits and Penetration Testing: Conducting regular security assessments to identify and address vulnerabilities. Penetration testing simulates real-world attacks to test the effectiveness of security measures.
- Robust Incident Response Plan: Developing a comprehensive incident response plan to effectively manage and mitigate security incidents. This plan should include clear procedures for detection, containment, eradication, recovery, and post-incident activity.
Frequently Asked Questions (FAQs)
Q: Is 5G inherently less secure than 4G?
A: 5G is not inherently less secure than 4G. However, the increased complexity, connectivity, and data volume associated with 5G introduce new security challenges that require proactive mitigation. With proper security measures in place, 5G can be just as secure, or even more secure, than 4G.
Q: What role does encryption play in 5G security?
A: Encryption is crucial for securing data transmitted over the 5G network. End-to-end encryption, where data is encrypted from source to destination, provides the strongest protection against unauthorized access.
Q: How can businesses ensure the security of their IoT devices on a 5G network?
A: Securing IoT devices requires a multi-faceted approach, including secure device provisioning, firmware updates, access control, and vulnerability management. Regular security assessments and penetration testing are also essential.
Q: What are the key regulatory considerations for businesses using 5G?
A: Businesses must comply with various data privacy and security regulations, including GDPR, CCPA, and other regional laws. This includes data encryption, access control, data breach notification, and data sovereignty considerations.
Q: How can AI and machine learning enhance 5G security?
A: AI and machine learning can significantly improve threat detection and response by analyzing vast amounts of data to identify anomalies and predict potential attacks. They can also automate security tasks, improving efficiency and reducing the risk of human error.
Q: What is the importance of a robust incident response plan in a 5G environment?
A: A well-defined incident response plan is crucial for effectively managing and mitigating security incidents. It enables rapid detection, containment, eradication, recovery, and post-incident analysis, minimizing the impact of a breach.
The transition to 5G presents both exciting opportunities and significant security challenges. By understanding these risks and implementing proactive security measures, businesses can harness the transformative power of 5G while protecting their valuable data and maintaining a secure operational environment. Continuous monitoring, adaptation, and investment in cutting-edge security technologies are essential to navigate this evolving landscape effectively.
[Source URL: Insert relevant URL here – e.g., a NIST publication on 5G security, a report from a reputable cybersecurity firm, etc.]
Closure
We hope this article has helped you understand everything about “how 5G technology affects business data security”. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on “how 5G technology affects business data security”!
We’d love to hear your thoughts about “how 5G technology affects business data security”—leave your comments below!
Stay informed with our next updates on “how 5G technology affects business data security” and other exciting topics.
