“cybersecurity strategies for startup businesses in the US”
Related Articles
- “how To Detect And Prevent Fileless Malware Attacks”
- “managing Third-party Risk In Data Security Strategies”
- “cloud Security Trends For Business Owners 2025”
- “2025 Best Practices For Securing Business Data”
- “how To Secure IoT Devices In Your Business Network”
Introduction
Discover everything you need to know about “cybersecurity strategies for startup businesses in the US”
However, their rapid growth often comes with a significant vulnerability: cybersecurity. While established corporations may have dedicated IT teams and substantial budgets for security, startups frequently operate with limited resources and personnel. This article delves into the often-overlooked cybersecurity strategies crucial for US startups to thrive without becoming victims of cyberattacks. We’ll explore both well-known best practices and lesser-known "secret" tips that can significantly bolster your security posture.

1. Prioritizing People: The Human Firewall is Your First Line of Defense
Many startups mistakenly believe cybersecurity is solely about technology. The reality is that human error accounts for a significant percentage of breaches. Your employees are your first, and often most vulnerable, line of defense. Therefore, investing in comprehensive security awareness training is paramount. This isn’t just a one-time session; it should be an ongoing process incorporating regular updates, phishing simulations, and interactive modules.
Secret Tip: Gamify your security training! Introduce friendly competition, reward participation, and make the learning process engaging. A bored employee is a susceptible employee. Consider using platforms that offer personalized training based on individual risk profiles.
2. Building a Strong Foundation: Essential Security Infrastructure
Before focusing on sophisticated tools, prioritize building a solid security foundation. This includes:
-
Strong Passwords and Multi-Factor Authentication (MFA): Enforce strong password policies and mandate MFA for all accounts, especially those with access to sensitive data. Password managers can significantly assist in managing complex passwords.
Regular Software Updates: Outdated software is a hacker’s dream. Implement a robust patch management system to ensure all software, including operating systems, applications, and firmware, is regularly updated.
-
Secure Network Configuration: Configure your network with strong firewalls, intrusion detection/prevention systems (IDS/IPS), and VPNs to protect against external threats. Segment your network to limit the impact of a potential breach.
-
Data Backup and Recovery: Regularly back up your data to a secure offsite location. Test your recovery procedures to ensure you can restore your data in case of a disaster or ransomware attack.
Secret Tip: Explore open-source security tools. While not always as feature-rich as commercial solutions, they can provide surprisingly robust protection at a fraction of the cost. Thoroughly vet any open-source tools before deployment.
3. Data Security: Protecting Your Most Valuable Asset
Data is the lifeblood of any startup. Protecting it should be a top priority. This involves:
-
Data Loss Prevention (DLP): Implement DLP measures to prevent sensitive data from leaving your network unauthorized. This includes tools that monitor data movement and block suspicious activity.
-
Data Encryption: Encrypt sensitive data both in transit and at rest. This protects data even if your systems are compromised.
-
Access Control: Implement the principle of least privilege. Grant users only the access they need to perform their jobs. Regularly review and update access permissions.
-
Compliance: Understand and comply with relevant data privacy regulations, such as GDPR, CCPA, and HIPAA, depending on your industry and the type of data you handle.
Secret Tip: Consider using a zero-trust security model. This approach assumes no implicit trust and verifies every user and device before granting access to resources, significantly reducing the attack surface.
4. Cloud Security: Navigating the Cloud Landscape
Many startups leverage cloud services for scalability and cost-effectiveness. However, cloud security requires careful consideration:
-
Choose Reputable Cloud Providers: Select providers with strong security track records and robust compliance certifications.
-
Secure Cloud Configurations: Configure your cloud environments securely, following best practices for access control, encryption, and data protection.
-
Regular Security Audits: Conduct regular security audits of your cloud infrastructure to identify and address vulnerabilities.
-
Cloud Security Posture Management (CSPM): Utilize CSPM tools to monitor your cloud environment for misconfigurations and security risks.
Secret Tip: Leverage cloud-native security tools offered by your cloud provider. These tools are often integrated directly into the platform and provide enhanced security capabilities.
5. Incident Response Planning: Preparing for the Inevitable
Even with the best security measures, cyberattacks can still occur. A well-defined incident response plan is crucial for minimizing the impact of a breach. This plan should include:
-
Incident Identification and Reporting: Establish clear procedures for identifying and reporting security incidents.
-
Containment and Eradication: Develop strategies for containing and eradicating threats.
-
Recovery and Restoration: Outline procedures for recovering your systems and data.
-
Post-Incident Activity: Define steps for analyzing the incident, improving security measures, and communicating with stakeholders.
Secret Tip: Conduct regular tabletop exercises to simulate real-world scenarios and test your incident response plan. This will help identify weaknesses and improve your team’s preparedness.
6. Outsourcing Security: When to Seek Professional Help
Startups often have limited resources and expertise. Outsourcing certain aspects of cybersecurity can be a cost-effective and efficient solution. Consider outsourcing tasks such as:
-
Penetration Testing: Hire security professionals to conduct penetration tests to identify vulnerabilities in your systems.
-
Vulnerability Scanning: Use automated tools or outsource vulnerability scanning to regularly assess your security posture.
-
Security Auditing: Engage security auditors to conduct independent assessments of your security controls.
-
Managed Security Services Providers (MSSPs): Consider using an MSSP to manage your security infrastructure and operations.
Secret Tip: Negotiate flexible contracts with cybersecurity providers. Start with a smaller scope of work and scale up as your needs and budget allow.
7. Staying Ahead of the Curve: Continuous Monitoring and Adaptation
The cybersecurity landscape is constantly evolving. Staying informed about emerging threats and adapting your security strategies accordingly is critical. This involves:
-
Threat Intelligence: Monitor threat intelligence feeds to stay aware of the latest threats and vulnerabilities.
-
Security News and Blogs: Follow reputable security news sources and blogs to keep up-to-date on industry trends.
-
Security Conferences and Training: Attend security conferences and training events to learn from experts and network with other professionals.
-
Regular Security Assessments: Conduct regular security assessments to evaluate the effectiveness of your security controls and identify areas for improvement.
Secret Tip: Build relationships with other startups and share security best practices. A collaborative approach can help everyone stay ahead of the curve.
8. Budgeting for Cybersecurity: Prioritizing Security Investments
Cybersecurity is an investment, not an expense. While startups operate on tight budgets, neglecting security can lead to far greater costs down the line. Prioritize security investments based on risk, focusing on critical assets and vulnerabilities. Explore cost-effective solutions such as open-source tools and cloud-based services.
Secret Tip: Include cybersecurity costs in your business plan from the outset. This will help secure funding and demonstrate to investors that you take security seriously. Highlight the potential financial losses from a breach to justify the investment.
Frequently Asked Questions (FAQs):
Q: How much should a startup spend on cybersecurity?
A: There’s no one-size-fits-all answer. The budget should be proportional to your risk profile, the sensitivity of your data, and your industry regulations. Start with essential security measures and gradually increase your investment as your business grows.
Q: What are the most common cybersecurity threats to startups?
A: Common threats include phishing attacks, ransomware, malware, denial-of-service (DoS) attacks, and insider threats.
Q: How can I detect a cybersecurity breach?
A: Look for unusual activity such as unauthorized access attempts, unexpected data loss, slow system performance, and suspicious emails. Implement security information and event management (SIEM) tools to help detect and respond to security incidents.
Q: What should I do if I experience a cybersecurity breach?
A: Follow your incident response plan. Immediately contain the breach, investigate the cause, recover your systems, and notify affected parties as required by law.
Q: Is it necessary to hire a dedicated cybersecurity professional?
A: For very small startups, outsourcing or using managed services might be more cost-effective. As you grow and handle more sensitive data, a dedicated professional becomes increasingly important.
This comprehensive guide offers valuable insights into cybersecurity strategies for US startups. By implementing these tips and tricks, startups can significantly reduce their risk of cyberattacks and protect their valuable assets. Remember, cybersecurity is an ongoing process, requiring constant vigilance and adaptation. Investing in security now will safeguard your business’s future and contribute to its long-term success.
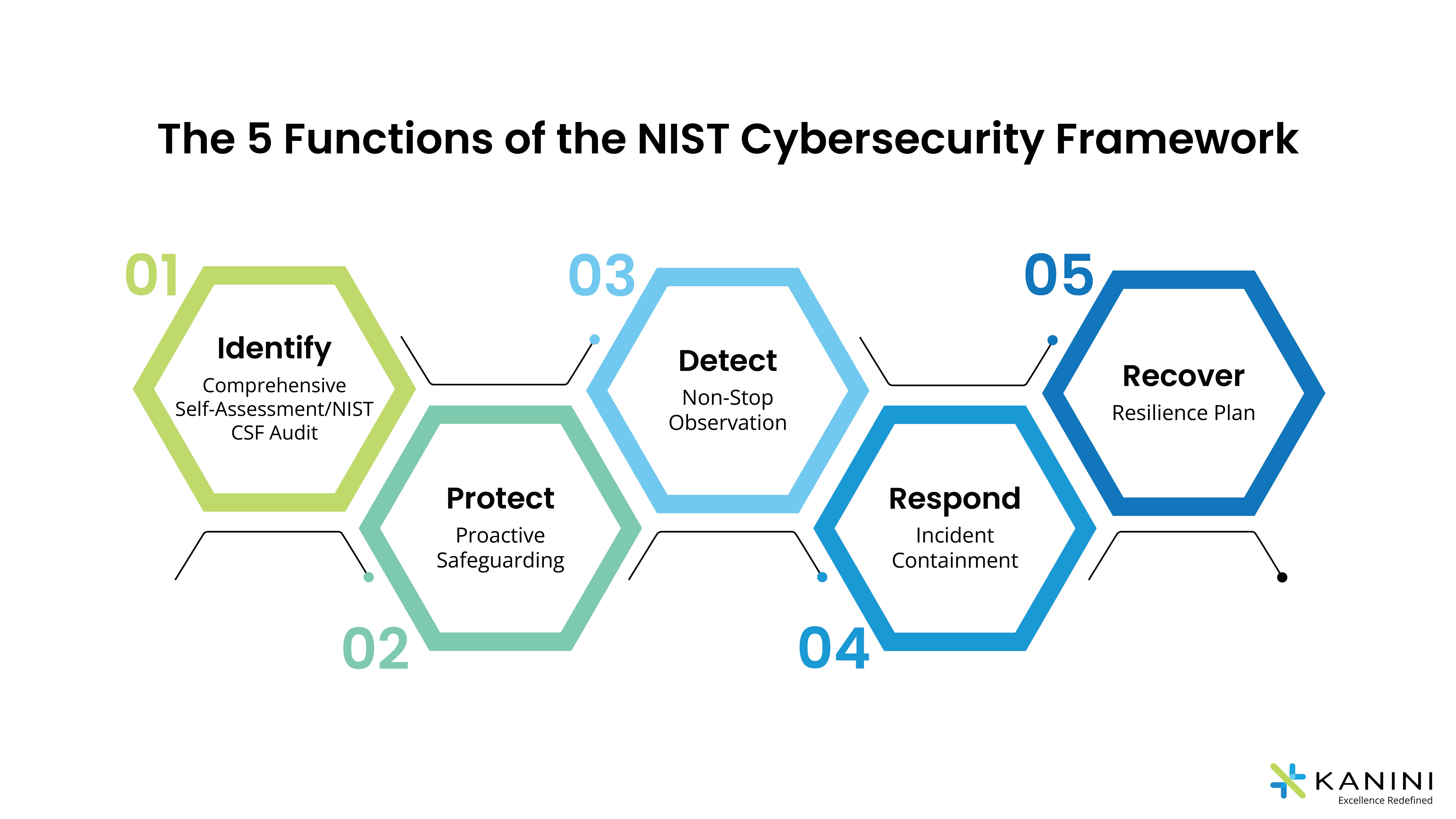
Source URL: [Insert a relevant URL from a reputable cybersecurity resource, such as NIST, SANS Institute, or a similar organization here.] (Example: https://www.nist.gov/cybersecurity)
Closure
We hope this article has helped you understand everything about “cybersecurity strategies for startup businesses in the US”. Stay tuned for more updates!
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “cybersecurity strategies for startup businesses in the US”—leave your comments below!
Keep visiting our website for the latest trends and reviews.
