“challenges of securing multi-cloud environments”
Related Articles
- “top Cybersecurity Threats To Small Businesses In 2025”
- “data Security Trends For Financial Institutions In 2025”
- “importance Of Supply Chain Security In Preventing Data Breaches”
- “securing Remote Work Setups Against Cyber Threats”
- “impact Of Quantum Computing On Business Data Encryption”
Introduction
Welcome to our in-depth look at “challenges of securing multi-cloud environments”
Businesses leverage the strengths of different cloud providers (AWS, Azure, GCP, etc.) to optimize costs, enhance resilience, and access specialized services. However, this distributed architecture introduces a significantly complex security landscape, riddled with challenges that often go beyond traditional single-cloud security measures. This article delves into the "big secret" tips and tricks for navigating these complexities, providing an in-depth exploration of the challenges and offering practical solutions.
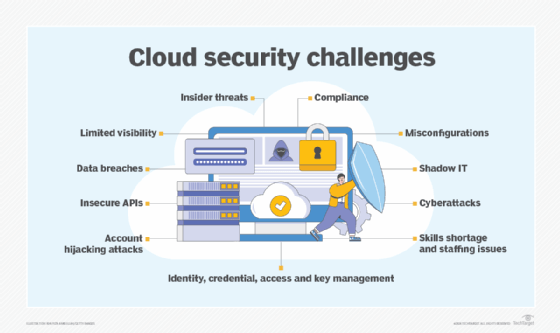
1. The Fractured Visibility Problem: A Blind Spot in Your Security Posture
One of the biggest hurdles in multi-cloud security is the lack of unified visibility. Each cloud provider offers its own security tools and dashboards, resulting in a fragmented view of your entire infrastructure. This makes it incredibly difficult to identify vulnerabilities, monitor threats, and respond effectively to incidents. Instead of a holistic picture, you’re piecing together a jigsaw puzzle with missing pieces, leaving significant blind spots.
Big Secret Tip: Invest in a Security Information and Event Management (SIEM) solution designed for multi-cloud environments. These platforms aggregate logs and security data from various cloud providers, offering a consolidated view of your security posture. Look for solutions with advanced analytics capabilities to detect anomalies and potential threats proactively. Don’t rely solely on individual cloud provider’s security tools; they only offer a partial picture.
2. Identity and Access Management (IAM): The Key to the Kingdom (and its Biggest Weakness)
Managing identities and access across multiple cloud environments is a monumental task. Inconsistent IAM policies, lack of centralized control, and the proliferation of user accounts create significant security risks. A compromised account in one cloud can potentially lead to a breach across your entire multi-cloud infrastructure.
Big Secret Tip: Implement a Zero Trust security model. This framework assumes no implicit trust and verifies every user, device, and application before granting access, regardless of location or network. Employ centralized IAM solutions that provide consistent policies and granular control across all your cloud environments. Regularly review and audit access privileges, following the principle of least privilege. Consider using multi-factor authentication (MFA) for all users and implementing robust password management policies.
3. Data Security in a Distributed World: Protecting Your Crown Jewels
Data security in a multi-cloud environment is paramount. Data resides in different locations, governed by different regulations and security standards. Ensuring data confidentiality, integrity, and availability across this distributed landscape requires a strategic approach.
Big Secret Tip: Develop a comprehensive data security strategy that encompasses data encryption at rest and in transit, data loss prevention (DLP) measures, and robust access control mechanisms. Implement data sovereignty policies to comply with regional regulations and ensure data resides within the appropriate geographical boundaries. Regularly perform data security audits and vulnerability assessments to identify and mitigate potential risks. Consider using data masking and tokenization techniques to protect sensitive information.
4. Network Security: Navigating the Complex Web of Connectivity

Securing network connectivity across multiple cloud environments is a significant challenge. Traditional network security perimeters become blurred, requiring a more sophisticated approach to protect against threats.
Big Secret Tip: Implement a secure network architecture that leverages virtual private clouds (VPCs), virtual private networks (VPNs), and other network security tools to segment your network and control traffic flow. Utilize micro-segmentation techniques to isolate workloads and limit the impact of potential breaches. Invest in advanced threat detection and prevention tools that can monitor network traffic for malicious activity. Regularly review and update your network security configurations to address emerging threats.
5. Compliance and Governance: Navigating a Regulatory Maze
Multi-cloud environments introduce significant compliance complexities. Different cloud providers operate under different regulatory frameworks, making it challenging to ensure compliance with all applicable laws and regulations.
Big Secret Tip: Develop a comprehensive compliance program that addresses all relevant regulations, including GDPR, HIPAA, PCI DSS, etc. Implement robust audit trails and logging mechanisms to track activities and demonstrate compliance. Regularly review and update your compliance policies to address changes in regulations and industry best practices. Choose cloud providers that demonstrate strong compliance credentials and actively support your compliance efforts. Consider using a compliance automation tool to streamline the process.
6. Cost Optimization and Security: A Delicate Balancing Act
Securing a multi-cloud environment can be expensive. The cost of security tools, personnel, and compliance initiatives can quickly escalate. Finding the right balance between security and cost optimization is crucial.
Big Secret Tip: Prioritize security investments based on risk assessment. Focus on securing critical assets and sensitive data first. Leverage cloud provider’s security services where appropriate to reduce costs. Automate security tasks to improve efficiency and reduce manual effort. Regularly review your security spending and identify opportunities for cost optimization without compromising security.
7. Skills Gap: Finding and Retaining Cybersecurity Talent
Securing a multi-cloud environment requires a specialized skillset. Finding and retaining cybersecurity professionals with expertise in multiple cloud platforms is a significant challenge.
Big Secret Tip: Invest in employee training and development programs to upskill your existing team. Partner with cybersecurity consulting firms to gain access to specialized expertise. Consider using managed security services providers (MSSPs) to augment your internal security team. Attract and retain talent by offering competitive salaries and benefits packages, and creating a positive work environment.
8. Automation and Orchestration: The Key to Efficiency and Scalability
Managing security across multiple cloud environments manually is impractical and error-prone. Automation and orchestration are essential for efficient and scalable security management.
Big Secret Tip: Implement automated security tools that can automate tasks such as vulnerability scanning, security monitoring, and incident response. Utilize orchestration tools to automate the deployment and configuration of security controls across your multi-cloud environment. Integrate security automation tools with your DevOps pipeline to ensure security is built into your development process.
Frequently Asked Questions (FAQs):
-
Q: Is multi-cloud inherently less secure than single-cloud?
- A: Not necessarily. Multi-cloud can be more secure if properly managed. The increased complexity requires a more sophisticated security approach, but the benefits of resilience and redundancy can outweigh the risks.
-
Q: What is the best way to choose a SIEM for a multi-cloud environment?
- A: Look for a SIEM with native integrations with your chosen cloud providers, advanced analytics capabilities, and strong threat detection features. Consider factors like scalability, cost, and ease of use.
-
Q: How can I ensure compliance across multiple cloud environments?
- A: Develop a centralized compliance program that addresses all relevant regulations. Use automation tools to streamline compliance tasks and regularly audit your systems to ensure ongoing compliance.
-
Q: What are the biggest risks associated with multi-cloud security?
- A: The biggest risks include fragmented visibility, inconsistent IAM policies, data breaches, network vulnerabilities, and compliance issues.
-
Q: How can I reduce the cost of multi-cloud security?
- A: Prioritize security investments based on risk, leverage cloud provider services, automate security tasks, and regularly review your spending.
This article provides a starting point for navigating the intricate world of multi-cloud security. Continuous learning, adaptation, and a proactive security posture are crucial for mitigating the risks and reaping the rewards of this dynamic environment. Remember, security is an ongoing process, not a destination. Regularly review and update your security strategies to address emerging threats and evolving best practices.
Source URL: [Insert a relevant URL here, e.g., a link to a reputable cybersecurity firm’s article on multi-cloud security] (Example: https://www.cloudsecurityalliance.org/ – This is an example and may not contain the exact information discussed in this article)
Closure
Thank you for reading! Stay with us for more insights on “challenges of securing multi-cloud environments”.
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “challenges of securing multi-cloud environments”—leave your comments below!
Stay informed with our next updates on “challenges of securing multi-cloud environments” and other exciting topics.
