“challenges of securing data in hybrid cloud environments”
Related Articles
- “ransomware Recovery Strategies For Enterprises In 2025”
- “best Practices For Implementing Zero Trust Architecture In Business”
- “data Breach Insurance Requirements For Businesses”
- “AI-driven Threat Detection Tools For Businesses”
- “importance Of Supply Chain Security In Preventing Data Breaches”
Introduction
Join us as we explore “challenges of securing data in hybrid cloud environments”, packed with exciting updates
Securing data in a hybrid cloud environment presents a unique set of challenges that go beyond traditional on-premises or purely cloud-based security models. This article delves deep into these challenges, unveiling "big secret" tips and tricks to navigate them successfully.

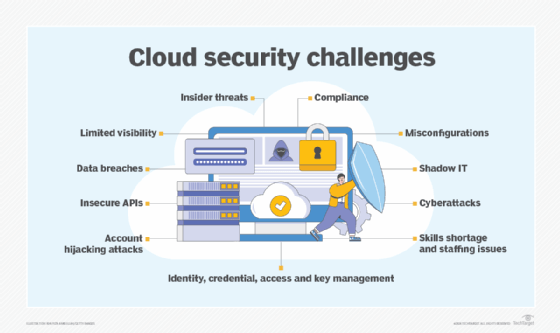
1. The Expanding Attack Surface: A Multi-Layered Threat Landscape
The most significant challenge in hybrid cloud security is the vastly expanded attack surface. Unlike a homogenous on-premises environment or a single public cloud, a hybrid cloud spans multiple physical locations, diverse network topologies, and various security postures. This creates numerous potential entry points for attackers. A breach in one part of the system – whether on-premises, in a public cloud like AWS, Azure, or GCP, or even within a Software-as-a-Service (SaaS) application integrated into the hybrid setup – can compromise the entire system.
Big Secret Tip #1: Implement a Zero Trust Security Model. Don’t trust anything, implicitly. Verify every access request, regardless of its origin (internal or external, on-premises or cloud). This involves strong authentication, authorization, and continuous monitoring across all environments. Micro-segmentation within both on-premises and cloud environments is crucial to limit the impact of a successful breach.
2. Data Visibility and Control: The Blind Spot Problem
Gaining comprehensive visibility into data location and access patterns across a distributed hybrid cloud environment is incredibly challenging. Data might reside in various locations – on-premises servers, multiple public cloud storage services, and even within SaaS applications. Tracking and controlling data movement and access becomes a complex, often fragmented, task. This lack of visibility creates significant blind spots, making it difficult to detect and respond to security incidents effectively.
Big Secret Tip #2: Leverage a Centralized Security Information and Event Management (SIEM) system. A robust SIEM solution aggregates security logs and events from all parts of your hybrid cloud environment, providing a single pane of glass for security monitoring and threat detection. Integrate your SIEM with threat intelligence feeds to proactively identify and mitigate potential threats. Consider using Cloud Access Security Brokers (CASBs) to monitor and control data access to cloud services.
3. Consistent Security Policies: The Enforcement Headache
Maintaining consistent security policies across diverse environments is a major hurdle. Different cloud providers have different security features and configurations. On-premises environments often have legacy systems and security tools that don’t easily integrate with cloud-native security services. Ensuring consistent enforcement of security policies – such as access control, data encryption, and vulnerability management – across this heterogeneous landscape requires significant effort and coordination.
Big Secret Tip #3: Automate security policy enforcement using Infrastructure-as-Code (IaC) tools. IaC allows you to define and manage your infrastructure and security configurations using code, ensuring consistency and repeatability across all environments. This reduces manual configuration errors and improves efficiency. Implement a Configuration Management Database (CMDB) to track and manage the configurations of all your systems, both on-premises and in the cloud.
4. Compliance and Regulatory Requirements: The Legal Labyrinth
Navigating the complex web of compliance and regulatory requirements in a hybrid cloud environment can be daunting. Different jurisdictions have different data protection laws and regulations (e.g., GDPR, CCPA, HIPAA). Ensuring compliance across all parts of your hybrid cloud environment requires meticulous planning and execution. Failure to comply can lead to hefty fines and reputational damage.
Big Secret Tip #4: Develop a comprehensive compliance program that addresses all relevant regulations and standards. This program should include regular audits, risk assessments, and documentation of your security controls. Choose cloud providers and SaaS applications that are compliant with the relevant regulations. Invest in tools that automate compliance reporting and monitoring.
5. Data Encryption: The Key to Protecting Sensitive Information
Data encryption is crucial for protecting sensitive information both at rest and in transit. However, implementing and managing encryption across a hybrid cloud environment presents its own set of challenges. Different encryption methods and key management systems may be used in different parts of the system, leading to inconsistencies and potential vulnerabilities.
Big Secret Tip #5: Implement a consistent encryption strategy across your entire hybrid cloud environment. Use strong encryption algorithms and key management systems that are integrated across all environments. Consider using hardware security modules (HSMs) for secure key storage and management. Automate encryption key rotation to minimize the impact of potential compromises.
6. Skilled Workforce: The Talent Gap
Managing the security of a hybrid cloud environment requires a highly skilled workforce with expertise in various security domains, including cloud security, network security, and data security. Finding and retaining such talent can be challenging, particularly in the face of a growing skills gap in the cybersecurity industry.
Big Secret Tip #6: Invest in training and development for your existing security personnel. Consider outsourcing certain security functions to specialized security service providers. Leverage automation and orchestration tools to reduce the workload on your security team and improve efficiency.
7. Incident Response: The Speed of Recovery
Responding effectively to security incidents in a hybrid cloud environment requires a well-defined incident response plan and the ability to quickly identify, contain, and remediate threats. The distributed nature of a hybrid cloud environment can make incident response more complex and time-consuming.
Big Secret Tip #7: Develop a comprehensive incident response plan that includes clear roles and responsibilities, communication protocols, and escalation procedures. Regularly test your incident response plan through simulations and tabletop exercises. Invest in security tools that automate incident detection and response.
8. Cost Optimization: Balancing Security and Budget
Securing a hybrid cloud environment can be expensive. The cost of security tools, services, and personnel can quickly add up. Finding the right balance between security and cost optimization is crucial.
Big Secret Tip #8: Prioritize your security investments based on risk. Focus on protecting your most critical assets and data. Explore cost-effective security solutions, such as open-source tools and cloud-native security services. Regularly review your security spending to identify areas for optimization.
Frequently Asked Questions (FAQs)
Q: What is the biggest risk associated with hybrid cloud security?
A: The expanded attack surface and the lack of visibility across multiple environments are arguably the biggest risks. A breach in one part of the system can easily compromise the entire environment if not properly segmented and monitored.
Q: How can I ensure consistent security policies across my hybrid cloud environment?
A: Utilize Infrastructure-as-Code (IaC) for automated deployment and configuration management, enforcing consistent security settings across all environments. Employ a centralized security management platform to orchestrate policies and monitor compliance.
Q: What is the role of automation in hybrid cloud security?
A: Automation is critical for efficiency and consistency. It allows for automated security policy enforcement, incident response, vulnerability scanning, and log analysis, reducing the burden on human resources and minimizing human error.
Q: How can I address the skills gap in hybrid cloud security?
A: Invest in training and upskilling your existing team, partner with managed security service providers (MSSPs) for specialized expertise, and leverage automation tools to reduce the reliance on highly specialized personnel.
Q: What are the key considerations for data encryption in a hybrid cloud?
A: Choose strong encryption algorithms, manage keys securely (ideally using HSMs), implement consistent encryption policies across all environments, and regularly rotate keys. Ensure encryption is applied both at rest and in transit.
Q: How can I ensure compliance with various regulations in a hybrid cloud?
A: Develop a comprehensive compliance program that addresses all relevant regulations, choose cloud providers and SaaS applications that meet compliance standards, and utilize tools that automate compliance reporting and monitoring.
Conclusion:
Securing data in a hybrid cloud environment is a complex undertaking, but with careful planning, the right tools, and a strong security posture, it’s achievable. By understanding the unique challenges and implementing the "big secret" tips and tricks outlined in this article, organizations can significantly improve their security posture and protect their valuable data in this increasingly prevalent IT architecture. Remember that security is an ongoing process, requiring constant vigilance, adaptation, and investment. Continuous monitoring, regular security assessments, and a proactive approach to threat detection are crucial for long-term success.
Source URL: [Insert a relevant URL here, for example, a link to a reputable cloud security vendor’s website or a cybersecurity news article discussing hybrid cloud security] (e.g., https://www.cloudsecurityalliance.org/)
Closure
We hope this article has helped you understand everything about “challenges of securing data in hybrid cloud environments”. Stay tuned for more updates!
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about “challenges of securing data in hybrid cloud environments”—leave your comments below!
Keep visiting our website for the latest trends and reviews.
