Best cybersecurity frameworks for small businesses 2025
Related Articles
- “cybersecurity Measures For Protecting Business APIs”
- “how Blockchain Can Enhance Data Security In Business”
- “role Of Blockchain In Enhancing Business Cybersecurity”
- “cybersecurity Risks Associated With AI-powered Tools”
- “cost Analysis Of Cybersecurity Solutions For SMEs In 2025”
Introduction
Join us as we explore Best cybersecurity frameworks for small businesses 2025, packed with exciting updates
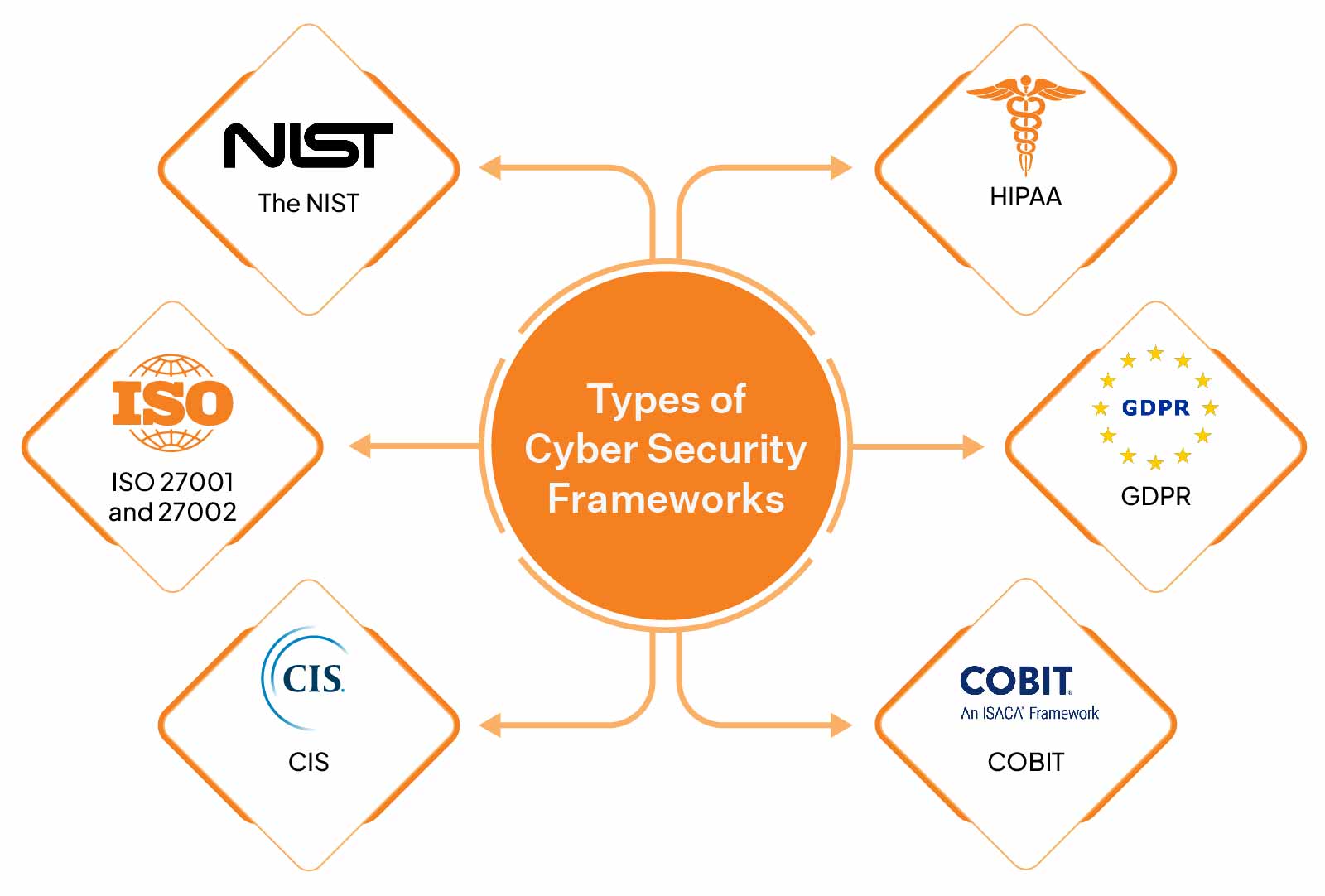
Traditional threats like phishing and malware remain prevalent, but we’re seeing a surge in sophistication. Ransomware attacks are becoming more targeted and destructive, leveraging AI and automation to bypass traditional security measures. Supply chain attacks are also on the rise, targeting vulnerabilities in third-party software and services. Furthermore, the increasing adoption of IoT devices expands the attack surface, creating numerous entry points for malicious actors. Small businesses often lack the resources of larger corporations, making them particularly vulnerable. Therefore, choosing the right framework and implementing it effectively is crucial.

2. NIST Cybersecurity Framework: A Foundation for Success
The National Institute of Standards and Technology (NIST) Cybersecurity Framework is a widely adopted, flexible framework that provides a valuable foundation for small businesses. It’s not prescriptive; instead, it offers a voluntary set of guidelines and best practices that can be adapted to suit various organizational sizes and needs. The framework’s core functions – Identify, Protect, Detect, Respond, and Recover – provide a structured approach to managing cybersecurity risks.
Secret Tip #1: Focus on the "Identify" Function: Many small businesses overlook the critical importance of the "Identify" function. This involves understanding your assets, your vulnerabilities, and your risks. Conduct a thorough asset inventory, identify critical systems and data, and assess your potential vulnerabilities. This forms the basis for effective risk management.
Secret Tip #2: Prioritize "Protect" Based on Risk: Don’t try to protect everything equally. Prioritize your efforts based on the identified risks. Focus on protecting your most critical assets and systems first. This might involve implementing strong access controls, data encryption, and regular software updates.
3. CIS Controls: A Prioritized Approach to Security
The Center for Internet Security (CIS) Controls provide a prioritized set of security controls that can be tailored to the specific needs of small businesses. These controls are categorized based on their impact and feasibility, allowing organizations to focus on the most effective measures first. The CIS Controls are particularly beneficial for small businesses with limited resources, as they provide a clear roadmap for improving their cybersecurity posture.
Secret Tip #3: Start with the Top 10 CIS Controls: Don’t feel overwhelmed by the entire list. Begin by implementing the top 10 CIS Controls, which address the most critical security issues. This provides a solid foundation upon which you can build more advanced security measures.
Secret Tip #4: Leverage Automation: Many CIS Controls can be automated, significantly reducing the workload on your IT team. Consider using security information and event management (SIEM) tools or automated vulnerability scanners to streamline your security processes.
4. ISO 27001: Achieving International Standards
For businesses that aim for international recognition of their security practices, ISO 27001 is a valuable certification. This internationally recognized standard provides a comprehensive framework for establishing, implementing, maintaining, and continually improving an information security management system (ISMS). While more complex than other frameworks, obtaining ISO 27001 certification can enhance your credibility and attract more clients.
Secret Tip #5: Start Small, Build Gradually: Implementing ISO 27001 is a significant undertaking. Don’t try to do everything at once. Start by focusing on specific areas and gradually expanding your ISMS over time.
Secret Tip #6: Document Everything: Meticulous documentation is crucial for ISO 27001 compliance. Maintain detailed records of your security policies, procedures, and controls. This will be essential during audits and will help ensure the ongoing effectiveness of your ISMS.
5. Integrating Frameworks: A Synergistic Approach
The best approach often involves integrating elements from multiple frameworks. For example, you might use the NIST Cybersecurity Framework as a guiding principle, incorporating specific controls from the CIS Controls to address prioritized risks, and potentially working towards ISO 27001 certification in the long term. This hybrid approach allows you to tailor your security posture to your specific needs and resources.
Secret Tip #7: Don’t Reinvent the Wheel: Leverage existing resources and tools. Many free and open-source tools are available to assist with various aspects of cybersecurity, such as vulnerability scanning, intrusion detection, and security awareness training.
Secret Tip #8: Regularly Review and Update: The cybersecurity landscape is constantly evolving. Regularly review and update your chosen framework and security controls to ensure they remain effective against emerging threats. Schedule annual reviews, or even more frequently if significant changes occur within your business.
6. Beyond Frameworks: The Human Element
No cybersecurity framework is foolproof without a strong emphasis on the human element. Employee training is crucial in mitigating risks associated with phishing attacks, social engineering, and accidental data breaches. Implementing robust security awareness training programs can significantly reduce the likelihood of human error leading to security incidents.
7. Choosing the Right Framework for Your Business
The ideal framework for your small business depends on various factors, including your industry, size, resources, and risk tolerance. Smaller businesses with limited resources might find the CIS Controls or a simplified version of the NIST Framework more manageable. Businesses with more complex operations and higher risk tolerance might opt for ISO 27001 certification. Consider consulting with a cybersecurity professional to determine the most appropriate framework for your specific needs.
8. Frequently Asked Questions (FAQs)
-
Q: How much does it cost to implement a cybersecurity framework? A: The cost varies significantly depending on the chosen framework, the size of your business, and the level of expertise required. Smaller businesses can often implement basic security measures at a relatively low cost, while more comprehensive implementations may require significant investment.
-
Q: How long does it take to implement a cybersecurity framework? A: The implementation time depends on the complexity of the framework and the resources available. Some frameworks can be implemented relatively quickly, while others may take months or even years to fully implement.
-
Q: Do I need a dedicated IT team to manage cybersecurity? A: Not necessarily. For smaller businesses, managed security service providers (MSSPs) can provide cost-effective solutions for managing cybersecurity.
-
Q: What happens if I experience a cyberattack? A: Have an incident response plan in place. This should outline the steps to take in the event of a security breach, including containment, eradication, recovery, and post-incident activity.
-
Q: How can I stay updated on the latest cybersecurity threats? A: Stay informed by subscribing to cybersecurity news sources, attending industry conferences, and participating in online communities.
By carefully considering these factors and implementing the appropriate cybersecurity framework, small businesses can significantly reduce their risk of cyberattacks and protect their valuable assets in the ever-evolving digital landscape of 2025. Remember that cybersecurity is an ongoing process, requiring continuous vigilance and adaptation. Don’t wait for a breach to happen; proactive measures are the key to success.
Source URL: [Insert a relevant URL from a reputable cybersecurity source here, e.g., NIST website, CIS website, etc.]
Closure
Thank you for reading! Stay with us for more insights on Best cybersecurity frameworks for small businesses 2025.
Don’t forget to check back for the latest news and updates on Best cybersecurity frameworks for small businesses 2025!
Feel free to share your experience with Best cybersecurity frameworks for small businesses 2025 in the comment section.
Keep visiting our website for the latest trends and reviews.
