Benefits of multi-factor authentication for business data security
Related Articles
- “how To Train Employees To Prevent Phishing Attacks”
- “impact Of Quantum Computing On Business Data Encryption”
- “importance Of Vendor Assessments In Supply Chain Security”
- “top-rated Cybersecurity Software For Businesses In 2025”
- “top Data Breach Prevention Tools For Businesses 2025”
Introduction
In this article, we dive into Benefits of multi-factor authentication for business data security, giving you a full overview of what’s to come
Businesses of all sizes grapple with the constant pressure to safeguard sensitive customer information, intellectual property, and financial records. While robust cybersecurity strategies are paramount, one often-overlooked yet incredibly powerful tool stands as a formidable shield against unauthorized access: Multi-Factor Authentication (MFA). This article delves into the often-unseen benefits of MFA, revealing insider tips and tricks to maximize its effectiveness and bolster your business’s data security posture.
1. Beyond the Password: Understanding the Multi-Layered Defense of MFA
Traditional password-based authentication, a single point of failure, is increasingly vulnerable to sophisticated attacks like phishing, brute-forcing, and credential stuffing. MFA elevates security by demanding multiple forms of verification before granting access. This layered approach significantly reduces the risk of unauthorized entry, even if one authentication factor is compromised. Imagine a fortress with multiple gates and guards – breaching one won’t grant access to the entire stronghold. That’s the essence of MFA.
Common authentication factors include:
- Something you know: Passwords, PINs, security questions.
- Something you have: Smartphones, security tokens, smart cards.
- Something you are: Biometrics like fingerprints, facial recognition, or voice recognition.
The combination of these factors creates a robust, multi-layered defense that significantly improves the overall security of your business data. The "secret" lies not just in implementing MFA, but in understanding how to strategically combine these factors for optimal protection.
2. The Secret Sauce: Optimizing MFA for Maximum Impact

While simply implementing MFA is a significant step forward, maximizing its effectiveness requires strategic planning and implementation. Here are some often-overlooked tips:
-
Factor Diversity: Don’t rely solely on one type of authentication factor. Combine "something you know" with "something you have" or "something you are" for enhanced security. For example, using a password alongside a one-time code from an authenticator app provides a much stronger defense than relying on a password alone.
-
Risk-Based Authentication: Implement adaptive MFA, which adjusts the authentication requirements based on assessed risk. For instance, if a login attempt originates from an unfamiliar location or device, the system might require additional authentication factors, such as a biometric scan.
-
Regular Audits and Reviews: Regularly review your MFA configuration and policies. Ensure all employees understand the procedures and are using the system correctly. Outdated or poorly configured MFA can be as vulnerable as no MFA at all. Consider conducting security awareness training to reinforce the importance of MFA and educate employees on best practices.
-
Strong Password Hygiene: Even with MFA, strong password practices remain crucial. Encourage employees to create complex, unique passwords for all accounts, and enforce regular password changes. A weak password can still be exploited, even with MFA, if an attacker gains access to other authentication factors.
-
Centralized Management: Utilize a centralized MFA solution that allows for easy management and monitoring of all user accounts and authentication factors. This simplifies administration and ensures consistent security across your organization.
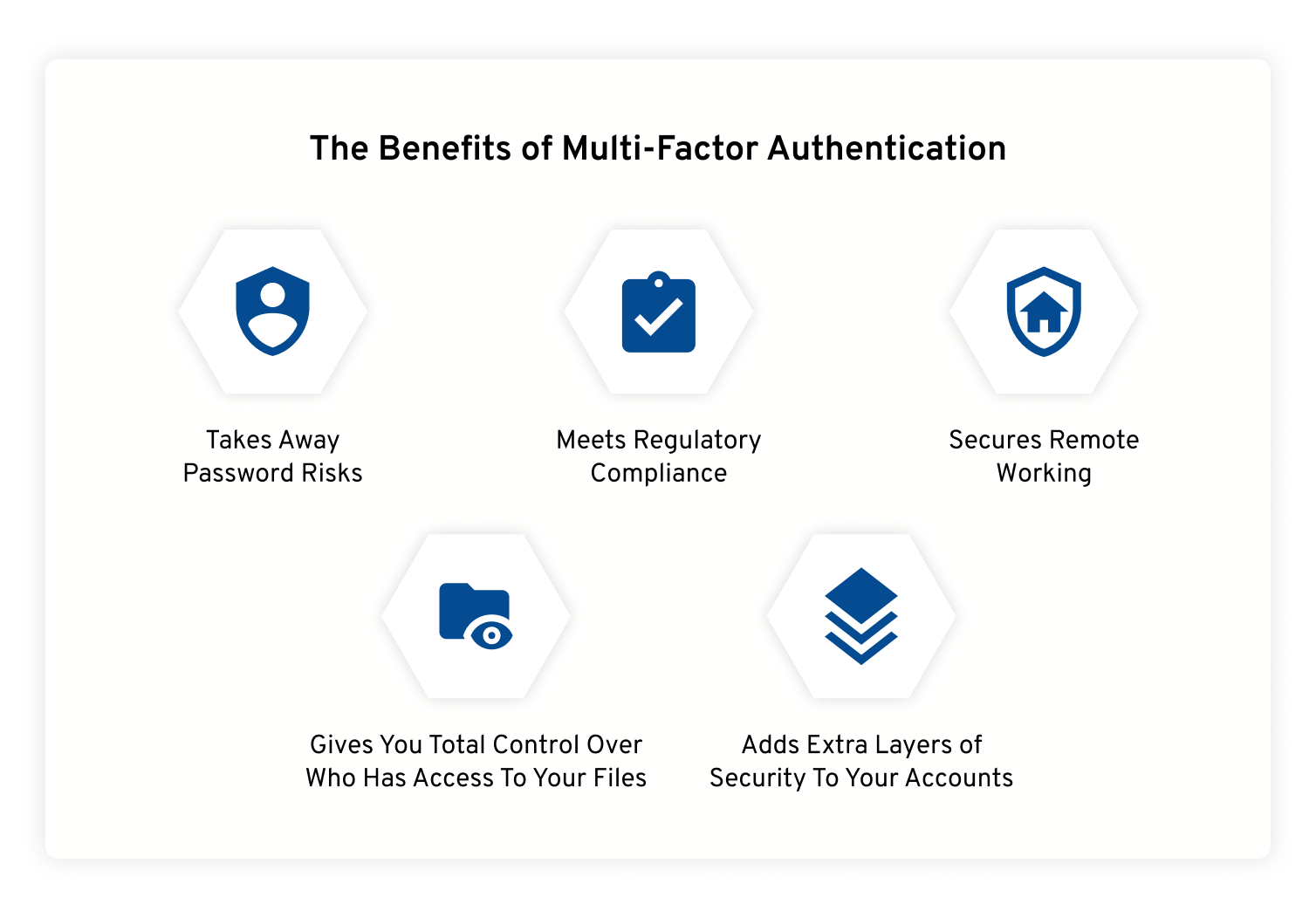
3. Beyond the Obvious: Uncovering Hidden Benefits of MFA
The benefits of MFA extend far beyond simply preventing unauthorized access. Here are some often-overlooked advantages:
-
Improved Compliance: Many industry regulations, such as HIPAA, PCI DSS, and GDPR, mandate or strongly recommend the use of MFA to protect sensitive data. Implementing MFA demonstrates a commitment to compliance and reduces the risk of penalties and reputational damage.
-
Reduced Liability: In the event of a data breach, demonstrating the use of robust security measures, including MFA, can significantly reduce your liability. It shows that you took reasonable steps to protect your data and minimizes potential legal and financial repercussions.
-
Enhanced Employee Trust: Implementing MFA demonstrates a commitment to protecting employee data and company assets. This can boost employee morale and trust in the organization’s security practices.
-
Streamlined Security Processes: While initially implementing MFA might seem like added complexity, a well-integrated system can actually streamline security processes by automating authentication and reducing the need for manual intervention.
4. Addressing Common MFA Challenges: Proactive Solutions
Despite its numerous benefits, MFA implementation can present challenges. Here are some common issues and how to proactively address them:
-
User Friction: Some employees may find MFA inconvenient or cumbersome. To mitigate this, choose user-friendly MFA methods and provide clear instructions and support. Consider offering a variety of authentication factors to cater to different preferences and technological capabilities.
-
Cost: Implementing MFA might involve initial investment in software, hardware, or training. However, the long-term cost savings from preventing data breaches far outweigh the initial investment. Consider the potential financial and reputational damage of a data breach when evaluating the cost-effectiveness of MFA.
-
Integration Complexity: Integrating MFA with existing systems can be complex. Choose MFA solutions that seamlessly integrate with your current infrastructure to minimize disruption and complexity. Seek professional assistance if needed to ensure a smooth and efficient integration.
5. The Future of MFA: Emerging Technologies and Trends
The landscape of MFA is constantly evolving. Several emerging technologies are poised to further enhance its effectiveness and usability:
-
Passwordless Authentication: This emerging trend aims to eliminate passwords altogether, replacing them with more secure and user-friendly authentication methods such as biometrics, push notifications, or hardware security keys.
-
Behavioral Biometrics: This technology analyzes user behavior patterns to detect anomalies and prevent unauthorized access, even if an attacker has obtained legitimate credentials.
-
AI-powered Threat Detection: AI algorithms can analyze authentication data to detect suspicious activity and automatically trigger additional security measures, enhancing the overall effectiveness of MFA.
6. Case Studies: Real-World Examples of MFA Success
Numerous organizations have successfully implemented MFA to enhance their data security. Analyzing real-world case studies reveals valuable insights into best practices and the tangible benefits of MFA implementation. For example, a financial institution that implemented MFA experienced a significant reduction in phishing attacks and successful account compromises. Similarly, a healthcare provider that adopted MFA improved its compliance with HIPAA regulations and reduced the risk of patient data breaches. These case studies underscore the importance of MFA in protecting sensitive data across various industries.
7. MFA and the Small Business: A Practical Guide
While large enterprises often have dedicated security teams, small businesses can also benefit significantly from MFA. Affordable and user-friendly MFA solutions are readily available, making it accessible for businesses of all sizes. Small businesses should prioritize implementing MFA on systems containing sensitive customer data, financial records, and other critical information. Leveraging cloud-based MFA solutions can simplify implementation and reduce administrative overhead.
8. Frequently Asked Questions (FAQs)
Q: Is MFA foolproof?
A: No security system is entirely foolproof. While MFA significantly reduces the risk of unauthorized access, it’s not a guarantee against all attacks. A sophisticated, well-resourced attacker might still find ways to bypass MFA, but the likelihood is considerably reduced.
Q: What if I forget my MFA code or lose my device?
A: Most MFA systems have recovery mechanisms in place. Contact your IT department or administrator for assistance in recovering access. Implement robust password recovery procedures to ensure users can regain access without compromising security.
Q: How much does MFA cost?
A: The cost of MFA varies depending on the solution, the number of users, and the level of features required. Some solutions are free for individual users, while enterprise-level solutions can be more expensive. The cost should be weighed against the potential financial and reputational damage of a data breach.
Q: Is MFA difficult to implement?
A: The complexity of MFA implementation depends on the existing infrastructure and the chosen solution. Cloud-based solutions generally offer easier integration than on-premise solutions. Consider seeking professional assistance if needed to ensure a smooth and efficient implementation.
Q: What types of MFA are best for my business?
A: The optimal MFA strategy depends on your specific needs and risk profile. Consider factors such as budget, technical capabilities, and the sensitivity of the data being protected. A security assessment can help determine the most appropriate MFA solution for your business.
In conclusion, multi-factor authentication is not merely a security feature; it’s a fundamental cornerstone of a robust data protection strategy. By understanding the nuances of MFA, implementing it strategically, and staying ahead of emerging threats, businesses can significantly enhance their data security posture and build a truly impenetrable fortress around their valuable information. The "secret" to success lies not just in the technology itself, but in the informed and proactive approach to its implementation and ongoing management.
Source URL: [Insert a relevant URL from a reputable cybersecurity source here, for example, a NIST publication or a reputable cybersecurity vendor’s website.]
Closure
Thank you for reading! Stay with us for more insights on Benefits of multi-factor authentication for business data security.
Make sure to follow us for more exciting news and reviews.
We’d love to hear your thoughts about Benefits of multi-factor authentication for business data security—leave your comments below!
Stay informed with our next updates on Benefits of multi-factor authentication for business data security and other exciting topics.
