“2025 guide to securing business emails from threats”
Related Articles
- “how To Balance Security And Usability In Enterprise Systems”
- “best Tools For Monitoring Business Data Access”
- “best VPN Services For Corporate Use”
- “role Of Endpoint Detection And Response (EDR) In Business Security”
- “best Practices For Implementing Zero Trust Architecture In Business”
Introduction
Join us as we explore “2025 guide to securing business emails from threats”, packed with exciting updates
In 2025, securing business emails will require a multi-layered, proactive approach that goes beyond basic antivirus software. This guide delves into the "big secret" tips and tricks that will ensure your business emails remain protected from increasingly advanced attacks. We’ll move beyond the obvious and explore the nuanced strategies crucial for robust email security in a world increasingly reliant on digital communication.
1. Beyond Antivirus: Implementing Advanced Threat Protection (ATP)
Antivirus software remains a crucial foundation, but it’s no longer sufficient on its own. Advanced threats utilize sophisticated techniques like polymorphic malware and zero-day exploits that bypass traditional signature-based detection. ATP solutions are the key to bridging this gap. These systems employ behavioral analysis, sandboxing, and machine learning to identify and neutralize threats before they can cause damage.
Big Secret Tip: Don’t rely solely on your email provider’s built-in ATP. Many providers offer varying levels of protection. Consider a dedicated third-party ATP solution that integrates seamlessly with your existing email infrastructure. Look for features like URL analysis (to detect malicious links before they’re clicked), attachment analysis (to identify malicious files before they’re opened), and reputation-based filtering (to block emails from known malicious senders). Furthermore, ensure your ATP solution is regularly updated to adapt to the ever-changing threat landscape.
2. Email Authentication: DMARC, SPF, and DKIM – Your Trifecta of Defense
Email authentication protocols are your first line of defense against spoofing and phishing attacks. Implementing DMARC (Domain-based Message Authentication, Reporting & Conformance), SPF (Sender Policy Framework), and DKIM (DomainKeys Identified Mail) creates a robust system that verifies the sender’s authenticity.
Big Secret Tip: Don’t just implement these protocols; meticulously configure them. Incorrectly configured SPF and DKIM records can lead to legitimate emails being blocked. Thoroughly test your configurations after implementation to ensure everything is working correctly. Monitor your DMARC reports regularly to identify potential issues and adapt your policies accordingly. Consider implementing a "quarantine" policy initially, gradually moving towards "reject" as you gain confidence in your setup and improve your email hygiene.
3. Employee Training: The Human Firewall is Your Strongest Asset
Even the most sophisticated technological defenses are vulnerable if your employees are unaware of the risks. Phishing attacks often rely on social engineering, exploiting human psychology to trick individuals into revealing sensitive information or clicking malicious links.
Big Secret Trick: Don’t rely on one-time training sessions. Implement ongoing, interactive security awareness training programs. Use simulated phishing campaigns to assess employee vulnerability and reinforce learning. Make training engaging and relevant to the specific threats your business faces. Reward employees for identifying and reporting suspicious emails. Remember, your employees are your first line of defense, and their vigilance is crucial.
4. Data Loss Prevention (DLP): Protecting Sensitive Information
Business emails often contain sensitive data, including customer information, financial records, and intellectual property. Data loss prevention (DLP) solutions help prevent this sensitive information from leaving your organization’s control.
Big Secret Tip: Go beyond basic keyword-based DLP. Implement advanced DLP solutions that use machine learning to identify sensitive data regardless of its format or location. These solutions can monitor email traffic in real-time, alerting administrators to potential breaches and automatically blocking or quarantining suspicious messages. Consider integrating your DLP solution with your ATP and email authentication protocols for a comprehensive security approach. Regularly review and update your DLP rules to reflect changes in your business and the types of sensitive data you handle.
5. Secure Email Gateway: The Centralized Security Hub
A secure email gateway (SEG) acts as a centralized point for filtering and protecting your email traffic. It sits between your email server and the internet, inspecting all incoming and outgoing emails for threats.
Big Secret Trick: Choose an SEG that integrates with your other security solutions, allowing for a unified security posture. Look for features like advanced malware scanning, anti-spam filtering, and content filtering to prevent the dissemination of inappropriate or harmful content. Regularly review and update your SEG’s policies to adapt to emerging threats and ensure optimal performance. Consider using a cloud-based SEG for scalability and ease of management.
6. Multi-Factor Authentication (MFA): Adding an Extra Layer of Security
MFA adds an extra layer of security by requiring multiple forms of authentication to access email accounts. This makes it significantly more difficult for attackers to gain unauthorized access, even if they obtain your password.
Big Secret Tip: Don’t settle for basic MFA methods like SMS codes, which are vulnerable to SIM swapping attacks. Implement strong MFA methods like authenticator apps (like Google Authenticator or Authy) or hardware security keys. Enforce MFA for all employees, especially those with access to sensitive data. Regularly educate employees about the importance of MFA and how to use it securely.
7. Regular Security Audits and Penetration Testing: Proactive Threat Identification
Proactive security measures are essential to identify vulnerabilities before attackers can exploit them. Regular security audits and penetration testing help identify weaknesses in your email security infrastructure.
Big Secret Trick: Don’t just focus on technical vulnerabilities. Include social engineering tests as part of your penetration testing to assess the effectiveness of your employee training programs. Regularly review the results of your audits and penetration tests, implementing necessary remediation measures promptly. Consider engaging external security experts to perform these assessments for an unbiased perspective.
8. Incident Response Plan: Minimizing Damage in Case of a Breach
Despite your best efforts, a security breach may still occur. Having a well-defined incident response plan in place is crucial to minimize the damage and ensure a swift recovery.
Big Secret Tip: Your incident response plan should be detailed and regularly updated. It should outline the steps to take in case of a security incident, including identifying the breach, containing the damage, eradicating the threat, recovering lost data, and notifying affected parties. Conduct regular incident response drills to ensure your team is prepared and familiar with the plan. This preparedness will significantly reduce the impact of any security incident.
Frequently Asked Questions (FAQs)
Q: How often should I update my email security software?
A: All email security software, including antivirus, ATP, and SEG, should be updated regularly, ideally automatically. Check your vendor’s recommendations for specific update schedules. Many vendors release updates multiple times a day to address emerging threats.
Q: What is the cost of implementing these security measures?
A: The cost varies depending on the size of your organization and the specific solutions you choose. However, the cost of a security breach far outweighs the investment in robust email security. Consider the potential financial and reputational damage of a data breach when evaluating the cost of security measures.
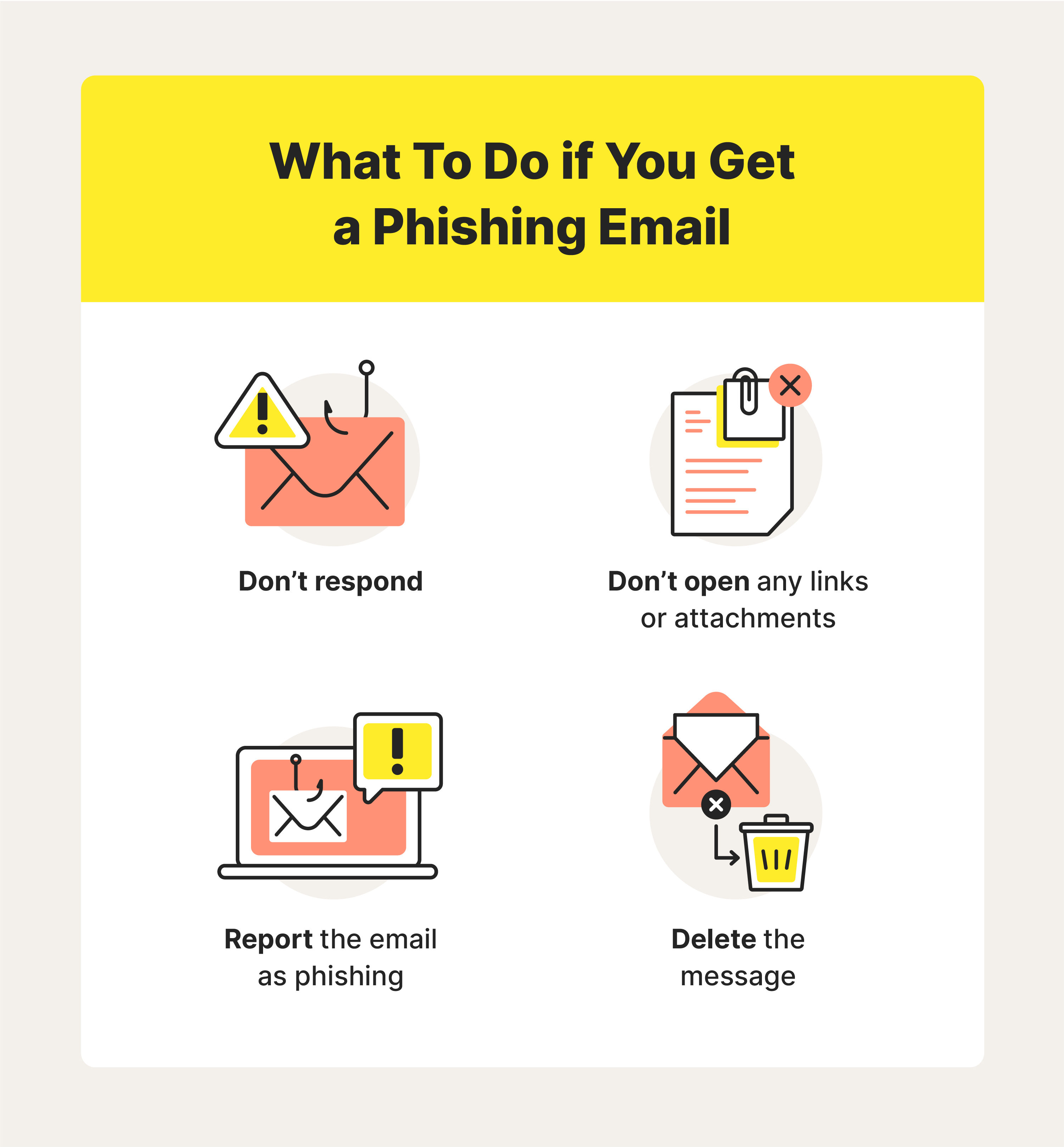
Q: How can I tell if an email is a phishing attempt?
A: Look for suspicious elements such as poor grammar, unexpected attachments, urgent requests for personal information, unusual sender addresses, and links that don’t match the expected domain. If anything seems off, don’t click any links or open any attachments. Instead, contact your IT department or the sender directly using a known, legitimate contact method.
Q: What should I do if I suspect a phishing attempt?
A: Immediately report the suspicious email to your IT department. Do not click any links or open any attachments. If you have already clicked a link or opened an attachment, immediately disconnect from the internet and contact your IT department.
Q: How can I measure the effectiveness of my email security measures?
A: Monitor your security logs, DMARC reports, and ATP alerts regularly. Conduct regular security audits and penetration tests. Track the number of phishing attempts and successful breaches. Use these metrics to identify areas for improvement and refine your security strategy.
In conclusion, securing business emails in 2025 requires a proactive, multi-layered approach. By implementing the strategies outlined in this guide, you can significantly reduce your risk of falling victim to email-borne threats. Remember that vigilance, employee training, and a continuous improvement mindset are just as crucial as the technology you employ. Staying informed about the latest threats and adapting your security measures accordingly is paramount to maintaining a secure email environment.
Source URL: [Insert a relevant URL here, for example, a cybersecurity firm’s blog post on email security best practices. Ensure the URL is accurate and relevant to the content.]
Closure
We hope this article has helped you understand everything about “2025 guide to securing business emails from threats”. Stay tuned for more updates!
Don’t forget to check back for the latest news and updates on “2025 guide to securing business emails from threats”!
Feel free to share your experience with “2025 guide to securing business emails from threats” in the comment section.
Keep visiting our website for the latest trends and reviews.
